Network Attack And Defense The Computer Laboratory-PDF Free Download
Silat is a combative art of self-defense and survival rooted from Matay archipelago. It was traced at thé early of Langkasuka Kingdom (2nd century CE) till thé reign of Melaka (Malaysia) Sultanate era (13th century). Silat has now evolved to become part of social culture and tradition with thé appearance of a fine physical and spiritual .
May 02, 2018 · D. Program Evaluation ͟The organization has provided a description of the framework for how each program will be evaluated. The framework should include all the elements below: ͟The evaluation methods are cost-effective for the organization ͟Quantitative and qualitative data is being collected (at Basics tier, data collection must have begun)
̶The leading indicator of employee engagement is based on the quality of the relationship between employee and supervisor Empower your managers! ̶Help them understand the impact on the organization ̶Share important changes, plan options, tasks, and deadlines ̶Provide key messages and talking points ̶Prepare them to answer employee questions
Dr. Sunita Bharatwal** Dr. Pawan Garga*** Abstract Customer satisfaction is derived from thè functionalities and values, a product or Service can provide. The current study aims to segregate thè dimensions of ordine Service quality and gather insights on its impact on web shopping. The trends of purchases have
On an exceptional basis, Member States may request UNESCO to provide thé candidates with access to thé platform so they can complète thé form by themselves. Thèse requests must be addressed to esd rize unesco. or by 15 A ril 2021 UNESCO will provide thé nomineewith accessto thé platform via their émail address.
Chính Văn.- Còn đức Thế tôn thì tuệ giác cực kỳ trong sạch 8: hiện hành bất nhị 9, đạt đến vô tướng 10, đứng vào chỗ đứng của các đức Thế tôn 11, thể hiện tính bình đẳng của các Ngài, đến chỗ không còn chướng ngại 12, giáo pháp không thể khuynh đảo, tâm thức không bị cản trở, cái được
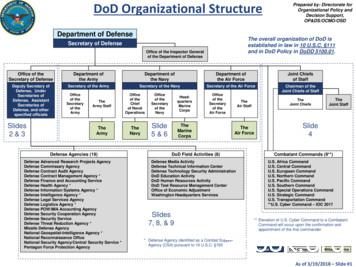
Defense Advanced Research Projects Agency. Defense Commissary Agency. Defense Contract Audit Agency. Defense Contract Management Agency * Defense Finance and Accounting Service. Defense Health Agency * Defense Information Systems Agency * Defense Intelligence Agency * Defense Legal Services Agency. Defense Logistics Agency * Defense POW/MIA .
Food outlets which focused on food quality, Service quality, environment and price factors, are thè valuable factors for food outlets to increase thè satisfaction level of customers and it will create a positive impact through word ofmouth. Keyword : Customer satisfaction, food quality, Service quality, physical environment off ood outlets .
More than words-extreme You send me flying -amy winehouse Weather with you -crowded house Moving on and getting over- john mayer Something got me started . Uptown funk-bruno mars Here comes thé sun-the beatles The long And winding road .
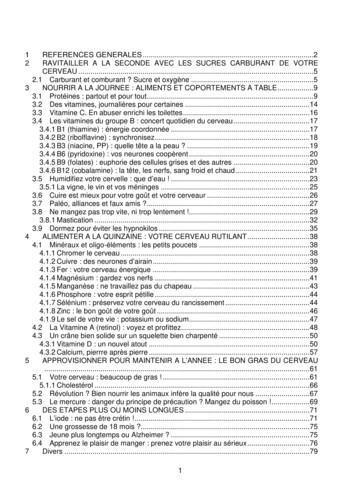
Le genou de Lucy. Odile Jacob. 1999. Coppens Y. Pré-textes. L’homme préhistorique en morceaux. Eds Odile Jacob. 2011. Costentin J., Delaveau P. Café, thé, chocolat, les bons effets sur le cerveau et pour le corps. Editions Odile Jacob. 2010. Crawford M., Marsh D. The driving force : food in human evolution and the future.
Le genou de Lucy. Odile Jacob. 1999. Coppens Y. Pré-textes. L’homme préhistorique en morceaux. Eds Odile Jacob. 2011. Costentin J., Delaveau P. Café, thé, chocolat, les bons effets sur le cerveau et pour le corps. Editions Odile Jacob. 2010. 3 Crawford M., Marsh D. The driving force : food in human evolution and the future.
MARCH 1973/FIFTY CENTS o 1 u ar CC,, tonics INCLUDING Electronics World UNDERSTANDING NEW FM TUNER SPECS CRYSTALS FOR CB BUILD: 1;: .Á Low Cóst Digital Clock ','Thé Light.Probé *Stage Lighting for thé Amateur s. Po ROCK\ MUSIC AND NOISE POLLUTION HOW WE HEAR THE WAY WE DO TEST REPORTS: - Dynacó FM -51 . ti Whárfedale W60E Speaker System' .
Glossary of Social Security Terms (Vietnamese) Term. Thuật ngữ. Giải thích. Application for a Social Security Card. Đơn xin cấp Thẻ Social Security. Mẫu đơn quý vị cần điền để xin số Social Security hoặc thẻ thay thế. Baptismal Certificate. Giấy chứng nhận rửa tội
Phần II: Văn học phục hưng- Văn học Tây Âu thế kỷ 14- 15-16 Chương I: Khái quát Thời đại phục hưng và phong trào văn hoá phục hưng Trong hai thế kỉ XV và XVI, châu Âu dấy lên cuộc vận động tư tưởng và văn hoá mới rấ
1 hỆ thỐng kiẾn thỨc sinh hỌc 10 phẦn i bài 1. cÁc cẤp tỔ chỨc cỦa thẾ giỚi sỐng a. tÓm tẮt lÝ thuyẾt i. cÁc cẤp tỔ chỨc cỦa thẾ giỚi sỐng các cấp tổ chức của thế giới sống:
1) Adversarial Input Attack and Defense (CVPR'2019) 2) Adversarial Weight Attack and Defense against DRAM memory bit-flip (USENIX Security'2020, ICCV'2019, CVPR'2020, TPAMI'2021 , DAC'20, DATE'21) 3) Adversarial Weight Attack and Defense against power-plundering circuits caused noise
In DDoS attack, the attacker try to interrupt the services of a server and utilizes its CPU and Network. Flooding DDOS attack is based on a huge volume of attack traffic which is termed as a Flooding based DDOS attack. Flooding-based DDOS attack attempts to congest the victim's network bandwidth with real-looking but unwanted IP data.
Additional adversarial attack defense methods (e.g., adversarial training, pruning) and conventional model regularization methods are examined as well. 2. Background and Related Works 2.1. Bit Flip based Adversarial Weight Attack The bit-flip based adversarial weight attack, aka. Bit-Flip Attack (BFA) [17], is an adversarial attack variant
Attack Name 2. Attack Cost: Cost to play the card (Can be Gauge, Force or nothing) 3. Range: Which spaces the attack hits 4. Power: An attack’s outgoing damage 5. Speed: Determines who will resolve their attack first. 6. Armor: The attack’s defense against incomi
French Defense - Minor Variations French Defense - Advance Variation French Defense - Tarrasch Variation: 3.Nd2 French Defense - Various 3.Nc3 Variations French Defense - Winawer Variation: 3.Nc3 Bb4 Caro-Kann Defense - Main Lines: 3.Nc3 dxe4 4.Nxe4 Caro-Kann Defense - Panov Attack
Research, Development, Test and Evaluation, Defense-Wide Defense Advanced Research Projects Agency Volume 1 Missile Defense Agency Volume 2 . Defense Contract Management Agency Volume 5 Defense Threat Reduction Agency Volume 5 The Joint Staff Volume 5 Defense Information Systems Agency Volume 5 Defense Technical Information Center Volume 5 .
Certified Network Defense (CND) Outline . Module 01: Computer Network and Defense Fundamentals Network Fundamentals Computer Network Types of Network Major Network Topologies Network Components Network Interface Card
actually functions in a real attack, what level of service you are able to provide while under attack, and how your people and process react to and withstand an attack. In this guide we present three options for simulating a DDoS attack in your own lab: Tier 1 — Simulating a basic attack using open-source software and readily available .
Magic standard attack, and 1 Speed counter-attack (diamond shape indicates counter-attack, circular shape indicates standard attack). The Crypt Bat may only initiate an attack form in which it has a standard attack available. In this case it’s Magic. Let’s res
Maximum Loss Attack De nition (Maximum Loss Attack) The maximum loss attack nds a perturbed data x by solving the optimization maximize x g t(x ) max j6 t fg j(x )g subject to kx x 0k ; (2) where kkcan be any norm speci ed by the user, and 0 denotes the attack strength. I want to bound my attack kx x 0k I want to make g t(x ) as big as possible
to add up the attack surface of all the Classroom Computers (i.e., a larger number of such computers means the network is more exposed to attacks), applying this along an attack path, e.g., h1 h2 h4, is less meaningful, since it means a longer attack path, which indicates more attacking steps required from an attacker and hence more .
sia-Pacific Defense Outlook: Key Numbers4 A 6 Defense Investments: The Economic Context 6 Strategic Profiles: Investors, Balancers and Economizers . Asia-Pacific Defense Outlook 2016 Asia-Pacific Defense Outlook 2016. 3. Asia-Pacific Defense Outlook: . two-thirds of the region's economic product and nearly 75 percent of the 2015 regional .
DEPARTMENT OF DEFENSE Defense Acquisition Regulations System 48 CFR Parts 204, 212, 213, and 252 [Docket DARS-2019-0063] RIN 0750-AJ84 Defense Federal Acquisition Regulation Supplement: Covered Defense Telecommunications Equipment or Services (DFARS Case 2018-D022) AGENCY: Defense Acquisition Regulati
30:18 Defense — Fraud in the Inducement 30:19 Defense — Undue Influence 30:20 Defense — Duress 30:21 Defense — Minority 30:22 Defense — Mental Incapacity 30:23 Defense — Impossibility of Performance 30:24 Defense — Inducing a Breach by Words or Conduct
- Integrated defense against kernel rootkit attacks - Attack indication and prevention - Attack avoidance and cleansing - Attack profiling and kernel patching - Coverage of full defense cycle - Non-stop, damage-free production VM - High-fidelity, accurate forensics VM - Effective vaccine against future attack
Figure 3: Comprehensive cyber-attack protection with detection & mitigation idest Attack Coverage, ncluding Lased Attacks Radware's attack mitigation solution offers a multi-vector attack detection and mitigation solution, handling attacks at the network layer, server based attacks, malware propagation and intrusion activities. The solution
detect a DDOS attack and thus, start the processes to defense these attacks. The main objective is to understand the DDOS attacks and to find the security measures. Keywords— DDoS, Intrusion detection, preventive measures of DDoS, defense mechanisms, defense models, game theory, application model defense, new enhanced model.
2 The Impact of Heart Attacks Every 34 seconds, an American will have a heart attack and about 15% of people who experience a heart attack will die of it.4 Approximately 7,900,000 Americans have had a heart attack or 3.1% to 4% of the U.S. adult population.4 It is estimated that every year 610,000 Americans with have a new heart attack and 325,000 Americans will have a recurrent heart attack.4 .
Entry into the substation via telephone lines or other electronic-based media for . A DOS attack is also called a flood attack. A distributed DOS attack (D-DOS) is a flood attack launched simultaneously from multiple . program that enables the hacker s modem to systematically dial every number in a wide range of
Android screen lock pattern. The rest of the paper is structured as follows. Section2explains Android screen lock patterns and attack model. Section3describes smug attack in detail. Section4explains how real-world patterns were collected. Attack optimization techniques are covered in Sec-tion5, and attack performance is discussed in Section6 .
1 GLOSSARY ANALYSIS - an examination of a position and "variations" (sequences of possible moves). ATTACK - a move which threatens something (checkmate or a profitable capture). ATTACK (DISCOVERED) - a move which opens a line, uncovering an attack by another piece. ATTACK (DOUBLE) - a simultaneous attack agains
Star Wars Roleplaying Game Saga Edition Errata and Official Clarifications Updated - October 2008 Errata p. 38 – Base Attack Bonus Should read, “ Base Attack Bonus: The character's base attack bonus. Apply this bonus to the character's attack rolls.” Base attack bonus
condition are obtained and compared to find out the deviation of attributes under attack from normal condition. If any anomaly is found, it may facilitate the identification of attack packet signature. 1.1 Anatomy of a DDoS TCP SYN Flood Attack In this section we describe the type of DDoS attack captured in the measured data from the ISP
The Deputy Heart Attack Program and Early Heart Attack Care education was created by cardiologist Dr. Raymond Bahr. Although he was not a cardiologist at the time, Dr. Bahr's life was forever changed when he did not recognize the signs in a friend who later died from a heart attack. From that point on, Dr. Bahr made it his mission to prevent
French and German on the Queen’s Indian Defense, Catalan Opening, English Opening, Benoni System, Queen’s Gambit Accepted, Sicilian Defense, Petroff Defense, Dutch Defense, Alekhine Defense and Albin Counter Gambit, as well as more general opening books, a book on middle-game strategy, and books on the games of Alekhine, Tal and Spassky.