Ignition And Java Security: Why And How Ignition Uses Java .
White PaperIgnition and Java Security:Why and How Ignition Uses Java to CreateSecure, Cross-Platform Systems800.266.7798www.inductiveautomation.com
Ignition and Java Security: Why and How IgnitionUses Java to Create Secure, Cross-Platform SystemsIgnition by Inductive Automation isthe first SCADA software solutionbuilt entirely on Java. Ignition’s useof Java makes it totally crossplatform compatible and easily webdeployable, two major reasons forthe software’s growing communityof global Ignition users.Java is a well-established programming languagethat has been used and trusted around the worldfor more than 20 years. Java was released in 1995and quickly became one of the top programminglanguages in the world. Since 2001, it has heldthe number-one or number-two spot on theTIOBE Index.¹According to Oracle, which has owned andsupported Java since 2009, Java is running on 15billion devices, is used by 10 million developersworldwide, 5 million students are learning Java,and it’s the number-one platform for developmentin the cloud.²Java is used by thousands of major companies.Consider that IBM uses Java across all of itscomputing platforms.³ IBM mainframes are usedby 92 of the world’s 100 largest banks and 9 outof the world’s 10 largest insurance companies; andby 71% of global Fortune 500 companies.⁴Why is Ignition Built on Java?At Inductive Automation, our mission is to developindustrial automation software that pushes theboundaries of innovation and empowers ourusers. We understood that technologies from theIT world had great potential to revolutionize theindustrial world. Ignition leverages Java and otherIT technologies such as SQL to enable companiesin almost every industry to do more with new andexisting n.comOur first and foremost reason for using Java isthat it’s based on the concept of “write once, runanywhere.” Its portability enables Ignition to be across-platform solution which users can run on anyoperating system.⁵Also, Java is network-centric, which givesIgnition its web-deployed capability. Developerscan work with resources across a network andcreate network-based applications using client/server architecture.Another reason is that Java is well-supported. TheJava community is over 10 million developersstrong and continues to grow, so there is a gigantictalent pool of skilled Java developers. Java hasan extraordinarily rich set of libraries, so there area phenomenal number of resources available fordeveloping with Java.These are all factors that let us remain nimbleand make Ignition the product that our customersdemand.What About Security?We are confident that Java continues to be the rightchoice for Ignition and delivers the performanceour growing community of users is looking for. Itscontinued, widespread use by major companiesand its popularity among programmers are atestament to its security and reliability.As we’ll explain in the next part of this paper, thereare many different parts within Java, and the securityissues are generally limited to the Java browserplug-in, not the Java language or API. Oracle hasmet these issues head-on by removing the JavaWeb Browser Plug-In from future versions.Furthermore, most web browsers have eitherstopped supporting the Java Web Browser Plug-Inor disabled it by default. Ignition clients do notrequire Java in the web browser in order to run.If you’d like more detail about these issues, pleaseread the rest of this paper for a deeper look insideJava and some steps you can take to keep yourIgnition system safe.Ignition and Java Security 2017 Inductive Automation 2 9
Ignition and Java Security: Why and How IgnitionUses Java to Create Secure, Cross-Platform SystemsWhat is Java? Part 1: The LanguageBefore we get into the details of the recent securityissues, it will help to have a solid understandingof Java technology. Java, first and foremost, is aprogramming language. It is a general-purposelanguage that a computer programmer can useto write any sort of program. In this respect, it issimilar to C, C , .NET, Python, and many otherprogramming languages.Programming languages can broadly be dividedinto two kinds: compiled or interpreted (seediagram A-1). Compiled languages use a compilerto turn the source code into an executable binary.Interpreted languages run source code directlythrough an interpreter, skipping the compilationstep but requiring an interpreter to be present torun the application.Java uses a slightly different model (see diagramA-2). It is a compiled language, but instead of compiling into machine code like traditional compiledlanguages (think C), it compiles into “bytecode.”Bytecode is like machine code for an imaginarytype of machine: not x86, not ARM, not any realCPU that has ever been built. It runs on a virtualmachine, which is a special program that translatesthe bytecode into machine-specific instructions onthe fly.The main advantage of the traditional model isspeed, with the trade-off being portability. Youneed to recompile your program for each differentkind of computer and operating system you wantto run on.The main advantage of the interpreted model isthat you typically get fancier language features,and assuming there is a version of “interpreter.exe”available for different kinds of systems, you getportability as well. Java is a blend of thesetwo models.By using compiled bytecode and a virtual machine,you get speeds that approach or often match thetraditional model, and you get portability as wellbecause there is a version of “jvm.exe” for differentarchitectures and operating systems.What is Java? Part 2: The APIWriting source code and then compiling it or interpreting it or running it through a JVM (Java virtualmachine) gives you the ability to execute ourceCodeSourceCodeDiagram A -1800.266.7798www.inductiveautomation.comIgnition and Java Security 2017 Inductive Automation 3 9
Ignition and Java Security: Why and How IgnitionUses Java to Create Secure, Cross-Platform ompiler“bytecode”“bytecode”Diagram A -2against a computer’s CPU. By itself this is nearlyuseless. Without some access to the operatingsystem, your program can’t do much of anything.Therefore, most programming languages includea rather extensive API (application programminginterface). This is a built-in library of programmingfunctions that give the programmer access tocomputer resources such as the filesystem, thenetwork, and the graphical user interface.It is this API that truly makes Java such a portableprogramming language. Let’s look at an example:Suppose you want to write a program that editsMy Program(Windowsspecific edits)a text file. If you wrote this program in C or C on Windows, you’d be programming against theWindows filesystem API. If you wanted to compilea version that was compatible with Linux, not onlywould you have to re-compile, but you would haveto alter your program to be coded against theLinux filesystem API. For a complex program, this“porting” of the code from one OS to another canbe extremely costly and complex.You can see how adding support for additionaloperating systems and CPU architectures greatlyincreases the complexity (refer to diagram B-1).my program x86.exeWindowsAPIWindowsCompilermy program x64.exeMy Program(original)my program x86My Program(Linuxspecific edits)LinuxAPILinuxCompilermy program x64Diagram B-1800.266.7798www.inductiveautomation.comIgnition and Java Security 2017 Inductive Automation 4 9
Ignition and Java Security: Why and How IgnitionUses Java to Create Secure, Cross-Platform SystemsWindows APIJava APILinux APIMy Program(bytecode)Java APIJava APIJVM on WindowsJavaCompilerJVM on LinuxMy ProgramMy Program(bytecode)Diagram B-2The Java API removes the need for this style ofmanual porting by providing an abstraction layer.Instead of dealing directly with the Windowsfilesystem API or the Linux filesystem API, a Javaprogrammer only deals with the Java filesystemAPI. The virtual machine then handles translatingbetween this “virtual” API to the true operatingsystem API (see diagram B-2).What is Java? Part 3: Java Applets andJava Web StartBeyond the language, compiler, virtual machineand API, Java has a number of ancillary technologies that surround it. Applets and Java Web Start(JWS) are two such technologies used for the samepurpose: making it easy to get Java programsdeployed and running on your computer.Applets (see diagram C-1), the older of these two,were invented in 1995 as a way to include richercontent inside a webpage. Remember that this wasway before HTML5 and AJAX, when the capabilitiesof a basic webpage were very limited. Originallythis functionality was built into the browser itself todownload Java bytecode referenced by a webpageand run it. Later, it became the responsibility of abrowser plug-in provided by Java to load and runthe bytecode for these applets.Web Browser (IE, Firefox, Chrome, etc.)Webpage containing an applet Java Browser Plug-In. Applet running inside a JVMin your browserJava Program(bytecode)Diagram C-1800.266.7798www.inductiveautomation.comIgnition and Java Security 2017 Inductive Automation 5 9
Ignition and Java Security: Why and How IgnitionUses Java to Create Secure, Cross-Platform SystemsJava Web Start, introduced in 2001, is a way to geta full-blown Java program installed and runningon a client computer without requiring an installer.From the user’s perspective, they click on a link,and the application downloads itself and runs.This was preferred over applets for more complexapplications that were better not stuck inside aweb browser.Java Web Start is a remarkably simple idea. Insteadof relying on a plug-in to the web browser, it simplyregisters a file association in the operatingsystem for the filetype “JNLP” (Java NetworkLaunch Protocol).As an example, this mechanism is similar to howAdobe registers an association with the filetype“PDF” so that when you download a PDF, it opensusing Acrobat Reader.JWS opens the JNLP file when you click on a WebStart launch link, which describes where to findthe binaries (bytecode) that makes up the Javaprogram you want to launch. Then it downloads thebinaries and starts up a JVM to run the program.Note that no browser plug-in is required for thisfunctionality (see diagram C-2).Security Concerns ExplainedJava itself, as a general-purpose programminglanguage, can’t really be considered “secure” or“insecure.” Consider that most viruses are written inC, but nobody considers C itself to be “insecure”; it’sjust a tool. This isn’t to belittle the security concerns,Web Browserbut rather to underscore exactly where the securityissues lie. Java programs themselves are actuallyquite secure, in that they are immune to one of themost common types of attacks (buffer overruns).Java is also just a tool: You could just as easily writea virus in Java as in C. The problem, therefore, isnot with Java itself, but rather in the way Java canbe deployed.If someone you did not know emailed you a filenamed “run me.exe”, would you execute thatprogram? Obviously not. We use an array of viruscheckers, filtering routers, and common sense, all fora common purpose: making sure that untrusted programs don’t get a chance to run on our computers.What about Java applets? Here’s a technologywhose entire purpose is to run a program on yourcomputer when you visit a webpage! Unsurprisingly,it is this deployment scheme that has been thecause of the recent security breaches involving Java.When applets and JWS (Java Web Start) weredesigned, the inherent security risk was not overlooked. To address this issue, Java used the ideaof a “sandbox.” A sandbox means that an untrustedJava program being deployed as an applet orthrough JWS would be allowed to run, but only withaccess to a restricted set of the Java API. Notably,the filesystem and the network would be off-limits,unless the applet was trusted. Simply stated, therecent security breaches have all involved runninguntrusted Java programs designed to exploit flawsin order to break out of the sandbox.javaws.exe(Java Web Start)JVMWebpage with JNLP linkLaunch Link: a href “launchfile.jnlp” JNLPJARs(bytecode)Diagram C-2800.266.7798www.inductiveautomation.comIgnition and Java Security 2017 Inductive Automation 6 9
Ignition and Java Security: Why and How IgnitionUses Java to Create Secure, Cross-Platform SystemsThe end result is an untrusted program running onyour computer, without your consent. Long storyshort: the sandbox system cannot be trusted.If the sandbox doesn’t work as advertised, howcan you protect yourself from this issue? Oneoption would be to disable Java applets and JWSentirely. This “nuclear option” is effective, butunfortunately will compromise your ability to conveniently use Ignition, since the Ignition Designerand Ignition clients use JWS to launch.Fortunately, your other option is quite good. Simply set Java’s security settings to not run untrustedapplications at all. This is the default setting forJava security. Instead of running untrusted applications in a sandbox, you can simply opt to not allowthem to run at all. Ignition, like any reputable Javaapplication, uses digital signatures to prove that itis a trusted application.You may also choose to disable the Java plug-inwithin your browser (refer to instructions below).How to Disable the Java Plug-Inin Your BrowserFor additional protection, you may disable theJava browser plug-in from within your browser.This will prevent websites from loading Javaapplets within web pages, but still allow JavaWeb Start to function. The directions fordisabling the Java browser plug-in are differentfor each browser:ChromeType “chrome://plugins” into your address bar.Find the “Java” item on the list and clickbelow it where it says “Disable” in blue. Restartyour browser.FirefoxChoose the “Add-ons” item under the “Tools”menu. Select “Plug-ins” on the left side. Find800.266.7798www.inductiveautomation.comThis will prevent applets from running at all,completely sidestepping the entire Java securityissue. If you do this, launching an Ignition client asan applet will not work, but very few customerschoose this launch option anyhow.The standard launch options (Windowed andFullScreen) which use JWS will work fine withoutthe Java browser plug-in.Trust and Digital SignaturesKeeping Java Web Start enabled for only trustedapplications is Oracle’s recommendation for Java,as well as ours. How is this trust established? We’lltake a moment to explain how digital signatureswork, and why they can be used to establish trust.Java applications can be “signed” with a digitalsignature. When they are signed, they can requestextra permissions: to be elevated out of the sandboxand run as a trusted application, with access to thefilesystem, network, etc. Java first confirms with thethe item in the list called “Java (TM) Platform .”Click the “Disable” button on the right. Restartyour browser.Internet Explorer 8, 9, 10Choose the “Manage Add-ons” item under the“Tools” menu. On the left of the popup under“Show,” select “All Add-ons.” Find the entries inthe list under the group “Oracle America, Inc.”Select each item (if more than one) and disablewith the disable button in the bottom righthand corner. Restart your browser.SafariChoose “Safari” and then “Preferences” onthe taskbar. Click “Security” on the top of thewindow that appears. Uncheck the box“Enabled Java.” Restart your browser.Ignition and Java Security 2017 Inductive Automation 7 9
Ignition and Java Security: Why and How IgnitionUses Java to Create Secure, Cross-Platform Systemsuser that they trust the author of the application.It is the identity of the author that confers thetrust. The digital signature ensures that this identitycannot be forged.To understand how this works, you mustunderstand something called PKI (Public KeyInfrastructure) and its underlying technology:asymmetric encryption (see diagram D-1).Imagine you have two keys. These keys arespecial, in that if you lock something with one key,it can only be unlocked with the other. Now, youkeep one key private, but freely make copies ofthe other key and distribute them to your friends.This is called your public key. If you want to senda message to a friend, you can lock it with yourprivate key. Anyone with your public key can readthe message, but nobody can lock the box with aDiagram D-1Unsigned Datadifferent message inside. The point is that if yourfriend receives the locked box, and your public keyopens that box, they know that you locked the box.The identity of who locked the box is known, andcannot be forged. This is asymmetric encryption.How does this work to prove the identity of a Javaprogram? (See diagram D-2.) We create a keypairwith a public and private key. We then send ourpublic key to a certificate authority. The certificateauthority’s job is to ensure that we are who we saywe are. They check us out, make sure we’re a realcompany, talk to us on the phone, etc. When theyare satisfied, they issue us a certificate, which theysign with their private key so the authenticity of thecertificate can be trusted.There are only a few certificate authorities in theworld, and your computer comes pre-installed withtheir public keys. Examples are Verisign, Thawte,GeoTrust, etc. When we sign our program with ourprivate key, and include the certificate, we becomea trusted identity.Therefore the end user can trust that 1) we are whowe say we are and 2) we signed the program(nobody has altered the program).Ignition Securitysigned withprivate keyprivate keySigned Datapublic keyverified withpublic mThere are other simple steps users can take tosecure their Ignition system. Ignition offers securityfeatures such as client authentication that giveorganizations the ability to assign user roles andpermissions. Users can further create securityzones to allow access to Ignition based ondetermined criteria. Ignition can leverage MicrosoftActive Directory and easily integrate with existingsecurity schemes. Furthermore, administrators canuse auditing to track behavior and changes madeto a project.Ignition includes support for SSL encryption,commonly used in the financial industry, to helpsafeguard communications between clients andservers. This becomes especially useful for remoteor wide-area installations with multiple locations.Ignition and Java Security 2017 Inductive Automation 8 9
Ignition and Java Security: Why and How IgnitionUses Java to Create Secure, Cross-Platform SystemsIf you have questions or would like more information about Java security orIgnition security, please contact Inductive Automation Support at: 800-266-7798 (US)or 916-456-1045 (international), or visit: Inductive AutomationUnsignedJAR(bytecode)Signed by CAIgnition’sCertificateClient ComputerPublicKeySignJARSigned JAR(bytecode)Certificate Authority (CA)Signed JAR(bytecode)[2]CertCert[1] CA’spublic key[1] verify certificate using CA public key[2] verify bytecode using Ignition’s public keyDiagram D-2Footnotes:¹ Krill, Paul. “Java, C Remain Entrenched as Most Popular Languages.” InfoWorld. Nov. 7, 2016.² “Go Java.” https://go.java/index.html³ “Java on z/OS.” IBM Knowledge Center. IBM.com⁴ O’Malley, Chris. “Executive Viewpoint 2017: Compuware – Mainstreaming the Mainframe.” Virtual Strategy Magazine. Feb. 3, 2017.⁵ Supported operating systems for Ignition v7.9: Windows Server 2008/2012; Windows Vista, 7, 8, and 10; Ubuntu Linux 12.04 or later; and otherJava SE-enabled on and Java Security 2017 Inductive Automation 9 9
programmer only deals with the Java filesystem API. The virtual machine then handles translating between this “virtual” API to the true operating system API (see diagram B-2). What is Java? Part 3: Java Applets and Java Web Start Beyond the language, compiler, virtual machine and API, Java has a number of ancillary technolo-gies that .
java.io Input and output java.lang Language support java.math Arbitrary-precision numbers java.net Networking java.nio "New" (memory-mapped) I/O java.rmi Remote method invocations java.security Security support java.sql Database support java.text Internationalized formatting of text and numbers java.time Dates, time, duration, time zones, etc.
Java Version Java FAQs 2. Java Version 2.1 Used Java Version This is how you find your Java version: Start the Control Panel Java General About. 2.2 Checking Java Version Check Java version on https://www.java.com/de/download/installed.jsp. 2.3 Switching on Java Console Start Control Panel Java Advanced. The following window appears:
Spark-ignition engines with turbocharger or direct fuel injection require higher spark energies. The high voltage connection between ignition coil and spark plug must be functional and safe. This is where BERU comes in with high-quality ignition cables with suitable contacts or high-voltage ignition coil connectors. 5 OPERATION OF IGNITION
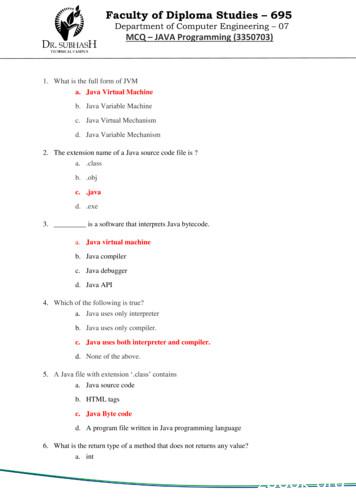
3. _ is a software that interprets Java bytecode. a. Java virtual machine b. Java compiler c. Java debugger d. Java API 4. Which of the following is true? a. Java uses only interpreter b. Java uses only compiler. c. Java uses both interpreter and compiler. d. None of the above. 5. A Java file with
CORE JAVA TRAINING COURSE CONTENT SECTION 1 : INTRODUCTION Introduction about Programming Language Paradigms Why Java? Flavors of Java. Java Designing Goal. Role of Java Programmer in Industry Features of Java Language. Installing Java Di
JAR Javadoc Java Language jar Security Others Toolkits: FX Java 2D Sound . Java Programming -Week 1. 6/25. Outline Java is. Let’s get started! The JDK The Java Sandbox . into your namespace. java.lang contains the most basic classes in the Java language. It is imported automatically, so
Java Consultant, Sun Professional Services, Dallas Other books cover the WHAT of Java (describing the syntax and the libraries) or the HOW of Java (practical programming examples). Thinking in Java is the only book I know that explains the WHY of Java; why it was designed the way it was, why it works the way it does, why it
Andreas Werner The Mermin-Wagner Theorem. How symmetry breaking occurs in principle Actors Proof of the Mermin-Wagner Theorem Discussion The Bogoliubov inequality The Mermin-Wagner Theorem 2 The linearity follows directly from the linearity of the matrix element 3 It is also obvious that (A;A) 0 4 From A 0 it naturally follows that (A;A) 0. The converse is not necessarily true In .