An Internal Auditor’s Guide To Blockchain: Blurring The .
An internal auditor’s guide toblockchain: Blurring the linebetween physical and digitalPart one: Introduction to blockchain
An internal auditor’s guide to blockchain: Blurring the line between physical and digital Part oneThe world is being ushered into the FourthIndustrial Revolution (Industry 4.0) atbreakneck speed. In this age, disruptivetechnological advances and trends arerapidly reshaping business models,improving productivity, and enablinginnovation in the way organizations provideproducts and services to their consumers,thereby creating entirely new markets. AsIndustry 4.0 gains momentum, how theworld works and lives is being redefined,reengineered, and reinvented. The linebetween the digital and physical is blurring.while another 41 percent of respondentssay they expect their organizations todeploy blockchain applications within thenext 12 months. Furthermore, nearly 40percent of respondents reported that theirorganization will invest 5 million or more inblockchain technology in the coming year.Blockchain technology is poised to be one ofthe key pillars of Industry 4.0. According to a2018 report by Gartner,1 the business valuefrom blockchain will reach 3.1 trillion by2030 through cost reduction and revenuegrowth. Further, according to its 2017CEO Survey,2 25 percent of participatingCEOs perceive the impact of blockchainto be either “major” or “transformational.”Blockchain was also the most-searched termon Gartner.com throughout most of 2017.3Only 40 percent of surveyed CAEsreported that their functions had astrong impact and influence withinthe organization. In addition, while 46percent of the respondents believe thatthe broader organization is generallyvery aware of internal audit, only 33percent believe the function is viewedvery positively. In many cases, thesefindings may indicate a need for internalaudit to deliver more value around issuesand risks that impact the organization’sability to achieve its goals.In addition, Deloitte Touche TohmatsuLimited’s (DTTL) global survey4 of morethan 1,000 global blockchain-savvyexecutives from seven countries indicatesthat momentum is shifting from a focuson learning and exploring the potentialof the technology to identifying andbuilding practical business applications.For example, 74 percent of those surveyedreport that their organizations see a“compelling business case” for the use ofblockchain and many of these organizationsare moving forward with the technology.About half of that number (34 percent)report that their organization already hassome blockchain system in production2The evolving role of internal auditand blockchainAccording to the recent DTTL 2018 GlobalChief Audit Executive (CAE) survey5:To enhance its impact and influence withinthe organization, internal audit needs tonot only provide assurance services, butmust also advise on complex businessissues and anticipate risk. Further, at atime when enterprises in every industryare innovating, it is imperative that theinternal audit function also keep pacewith the climate of constant disruption byemploying advanced analytics and focusingon newer technologies.As blockchain technology continues tograb the attention of board members andCXOs of many organizations, it becomesimperative for the internal audit functionto proactively acquaint itself with theopportunities and risks emerging from theimplementation of this technology. Internalaudit functions have an opportunity toenhance their impact and influence withinthe organization. In this age of informationoverload, it becomes very important for theinternal audit practitioner to cut throughthe noise. The internal audit group shouldbe able to separate facts from fiction, andprovide an objective, independent, and wellthought-out point of view.With this objective in mind, this serieson blockchain is designed to educateinternal auditors on the following topicsrelated to blockchain.Part one: Introduction to blockchain:This paper introduces internal auditorsto the concepts of distributed ledgertechnology and blockchains, key featuresand types of blockchains, how blockchainswork, and smart contracts, as well ascryptocurrencies, tokens, wallets, and InitialCoin Offerings (ICOs).Part two: Risk considerations inblockchain. This paper will inform internalauditors on some risks that organizationsare exposed to when implementingblockchain technology, with consideration tospecific use cases.Part three: Auditing blockchainenvironments. This paper will focus onthe uniqueness of auditing in a blockchainenvironment such as how a blockchainprocessing environment differs from atraditional processing environment.
An internal auditor’s guide to blockchain: Blurring the line between physical and digital Part oneIntroduction to blockchainBlockchains are protocols that allow entitiesto store and share transactional informationin a controlled and systematic way.Digital ledgersEvolution of ledgers—physical, digital,distributed: It all started with a need torecord, store, and exchange information.During the Bronze Age, physical ledgerswere used to maintain records of agriculturalgoods. Represented by records stored ina codex, ledgers were “pages” organizedinto volumes that formed an authoritativesource of information. The 1950s and‘60s led to the development of businesscomputers, and a ledger was representedby records stored in a database. Distributedledgers came into prominence in 2008 withthe release of Bitcoin and are representedby the consensus view of a group of peerswho share responsibility for maintainingthe ledger.Today, traditional physical and digitalledgers record entries in a single place. Asa central agency is typically responsible forthem, they are often called central ledgers.Central ledgers allow one authoritativecopy of the data. For physical ledgers, thisis a single codex or a volume in a series.Existing digital ledgers use a single system ofrecord, typically in the form of an enterpriseresource planning (ERP) system. Security ofcentral ledgers focuses on managing accessto this single source of stored information.Access to the ledger enables one to addentries as well as read or change existingones. Distributed ledgers, on the otherhand, do not rely on a single authoritativecopy of information. As a result, ensuring theintegrity of the ledger is more complicatedbecause a central authority to control theledger can no longer be relied upon.What is being “distributed” in a distributedledger is the responsibility for managing theledger—deciding what entries to includeand their order, and ensuring entries arenot changed once added. Generally, a groupof peers shares this responsibility, ratherthan leaving it to a central authority. Withno single agent responsible for maintainingthe ledger, participants must rely on theconsensus of the peers involved. Thecurrent state of the ledger is simply thepeers’ consensus view. Consequently,distributed ledgers aren’t defined in terms ofhow or where the information they containis stored—each peer may store ledgerdata how and where they prefer. Instead,they are defined by the ledger’s consensusmodel—the process peers use to reachconsensus. It is important to note that manydistributed ledgers may not have blocks,nor do they inherently require a blockchain.Based on this, there are different risksand opportunities that are relevant whenconsidering distributed ledger technology.Businesses exist to create and transfervalue and, in the age of Industry 4.0, valueis frequently derived from digital assets,records, and identity. The transfer of valuehas been traditionally seen as an expensiveand slow process. Three technologies havecome together to lay the groundwork forblockchain and to address this challenge(see figure 1): Peer-to-peer network: Every peerin the network is a server and aclient, both supplying and consumingresources. This enables the facilitationof a distributed ledger without a central,privileged third party. Asymmetric key cryptography: Amethod for verifying digital identity with ahigh degree of confidence, enabled by theuse of private and public keys. Consensus mechanisms: A processused to achieve agreement amongdistributed processes or systems. Theseare designed to achieve trustworthinessin a network involving multiple,unreliable nodes.A blockchain is a distributed ledger thatallows digital assets to be transacted ina real-time, immutable manner. In otherwords, a blockchain is a record, or ledger,of digital events organized in chronologicalblocks—one that is encrypted and“distributed” between many differentparties (see figure 1). It can only beupdated by consensus of a majority of theparticipants in the system. Once entered,information is secured using cryptographyin order to preserve the integrity of thedata. The blockchain contains a certainand verifiable record of every singletransaction ever made.Figure 1. Laying the groundwork for blockchain’s invention1Peer-to-peer network2Asymmetric key cryptography3Consensus mechanismsIn a peer-to-peer model, every peer in thenetwork is a server and client, both supplyingand consuming resourcesAsymmetric key cryptography is a method forverifying digital identity with a high degree ofconfidence, enabled by the use of privateand public keysProof-of-work is the consensus mechanismused by Bitcoin to secure the network,validate data authenticity, and control whendata can be written into the systemEnables the facilitation of a distributed ledgerwithout a central, privileged third partyAllows for individual ownership and exchangeof tokens among usersPrevents double spend by ensuring data isrecorded chronologically3
An internal auditor’s guide to blockchain: Blurring the line between physical and digital Part oneFigure 2. Specific features of different types of blockchainEnterprise friendliness“Open”“Federated”Public blockchainPermissioned blockchainPrivate blockchainAccessOpen read and writePermissioned write and/or readCentralized to one entitySpeedSlowerFasterFastestSecurityOpen networkApproved participantsOne participantIdentityAnonymous or pseudonymousKnown identitiesKnown identityNative assetsAny assetDetermined by platform chosenAssetBlockchains are protocols that allowentities to store and share transactionalinformation in a controlled and systematicway. Generally, the technology acts as aplatform and the associated plumbingthat allows applications to build on top.Therefore, it is entirely possible that an enduser of a blockchain-enabled applicationis unaware of the fact that a blockchain isbeing used to support the processing.Because the blockchain protocol uses apeer-to-peer or machine-to-machinevalue-transfer framework, every participantnode on the blockchain has an exact copyof the data, and a consensus protocolsynchronizes the updates across participantnodes. It therefore facilitates a near realtime value transfer (e.g., assets, records,identity) among participants without havingto wait for a central authority (“trusted thirdparty”) to validate the transactions. Thisdisintermediation replaces the need fora “trusted third party” with cryptographicproof. The cryptographic consensusprotocol also ensures immutability andirreversibility of all transactions postedon the ledger. Permissionless – A public, shared systemthat allows anyone to join the network,write to the network, and read thetransactions from those networks. Thesesystems have no single owner—everyoneon the network has an identical copy ofthe “ledger.” Cryptocurrencies such asBitcoin and Ethereum are examples ofproducts that run on these systems. Permissioned (semi-public) – Semipublic, shared systems are a form ofhybrid system that provide for situationswhere only preauthorized nodes arepermitted on the network; therefore, datawould not inherently be viewable to theworld. The data would be viewable onlyto those who have a preauthorized nodeon the network and can view and collectthe data. Permissioned (private) – Private, sharedsystems are those that operate within anentity, whereby outside entities are notable to participate.Features of a blockchainBlockchain consensus models:The lack of trust inherent to public, and toa lesser degree, permissioned blockchainsystems underlines the importance ofconsensus models. This lack of trust requiresconsensus models to function effectively innormal and adversarial conditions.Blockchains can be grouped into thefollowing two categories: permissionlessor permissioned. Where a permissionlesssystem is “open” to the public, apermissioned system can be “private” or“semi-public” (see figure 2):While this paper will not delve into thedifferent types of consensus models, it isimportant for internal audit practitioners tounderstand some examples of issues thatcan result when an inappropriate consensus4“Closed”mechanism is selected. Some issues thatmay result include: Blockchain hard fork(s) – Defined asan event whereby two divergent copiesof the blockchain are created. Typicallyoccurs as a result of a disagreementamongst network participants on the rulesgoverning the blockchain. Double spending – Double spending is aproblem principally with cryptocurrencieswhereby the same digital asset can bepromised/transferred to multiple entities. 51% dominance – Defined as a problemprimarily in the permissionless cryptoworld whereby one entity controls morethan 51% of the processing power of thenetwork. As a result, the entity has thetechnical ability to act maliciously. Poor performance – Consensusmechanisms are a trade-off betweenthe level of distrust amongstparticipants and the speed at whichconsensus needs to be achieved. Somesoftware vendors have developed amultitude of consensus mechanismsthat are measured in transactions persecond of processing power.
An internal auditor’s guide to blockchain: Blurring the line between physical and digital Part oneCryptocurrenciesThere are more than 1,000 different cryptocurrencies that existaccording to CoinMarketCap, each of which have their own digitalasset inherent to their unique blockchain. For example, the bitcoinnetwork has “Bitcoin/BTC” that are created and maintained on theBitcoin blockchain. Cryptocurrency, otherwise known as digitalassets, are stored on the blockchain at addresses that are ownedby participants. The digital assets are secured on the blockchainusing complex cryptographic functions. It is important to notethat cryptocurrencies are just the first real-world use case ofblockchain technology.The minimum viable ecosystem (MVE) for a cryptocurrency thatholds value is generally composed of:Coins: A coin is a unit of value native to a blockchain. It is a meansof exchange within the blockchain to incentivize the network ofparticipants to use the blockchain. Cryptocurrencies such asBitcoin, Ether, XRP, and Litecoin are all examples of native coins.The sole purpose of a coin is to exchange value, and it has limitedfunctionality beyond that. A common feature of all these coins isthat they each possess their own independent blockchain wheretransactions related to their own native coins occur.Wallets: A wallet stores the public addresses and correspondingprivate keys, which can be used to receive or send thecryptocurrency. Unlike physical currency that are stored in physicalwallets, the cryptocurrency itself is stored on the blockchain.Two basic types of cryptocurrency wallets are “hot wallets” and(“cold wallets.”) The key distinction between to the two wallets is thedegree to which the wallets are connected to the Internet. Whilehot wallets are connected to the Internet, cold wallets are offline.There are different reasons why an investor might want his or hercryptocurrency holdings to either be connected to or disconnectedfrom the Internet. It’s not uncommon for cryptocurrency enthusiaststo hold multiple wallets, some of them hot and some of them cold.Digital Currency Exchange (DCE): These are businesses thatallow customers to trade digital assets for other assets, such asconventional fiat money, or other digital currencies.Consensus mechanism: With the proof-of-work consensusmechanism, mining is the process by which transactions are verifiedand added to the blockchain, and also the means through which newbitcoins are released.5
An internal auditor’s guide to blockchain: Blurring the line between physical and digital Part oneSmart contracts, tokens, and ICOsSmart contracts: A smart contract is a computer program thatdirectly controls the transfer of digital assets between partiesunder certain conditions. Smart contracts act in a manner likea vending machine. Customers can put a dollar into a machine,provide a product selection, the machine will validate the dollar andthe product selection, and if available, the machine will dispensethat asset. If the product is unavailable or the dollar is fictitious,the machine will reject the transaction. A smart contract seeks todefine formal contract language into computer code in an effort toautomatically enforce obligations. Smart contracts are inherent inspecific blockchain implementations, but not all blockchains have thefunctionality available. The Ethereum network is an example of onepermissionless network that has smart contract functionality.Tokens: Tokens are created on existing blockchains using smartcontract code. Many tokens have utilized Ethereum’s ERC-20standard, of which code has been made public to allow forthe creation of new tokens. In this context, the smart contractfunctionality allows logic to be coded into the blockchain that allowsfor the creation of tokens based on predefined inputs.ICOs: An initial coin offering (ICO) is a “token sale” or “tokenlaunch” whereby an entity or group of entities creates tokens ona predefined date in order to generate capital or allow users tobuy into an ecosystem. Many of the token launches plan to utilizethe tokens in a future ecosystem that relies on the token in orderto function.Many ICOs have come under recent scrutiny by regulatory entitiesincluding the SEC, which launched their own ICO, known asHoweyCoins (https://www.howeycoins.com/index.html) in an effortto promote awareness and educate the investing public.As internal auditors navigate through this complex ecosystem, theyshould be aware of how inherently complex it is and understand thateach use case should be evaluated and carefully considered in lightof the above concepts.A summary of the key concepts presented in this document arepresented in figure 3.The main difference between coins and tokens is in their structure.Coins are on their own separate blockchains while tokensoperate on top of a blockchain that facilitates the creation ofdecentralized applications.Figure 3. Summary of key conceptsMay not requireDistributedledger(s)6Is always a.Enables trust forBlockchaintechnologyRequireAre a platform forCryptocurrenciesRequireTokensand ICOs
An internal auditor’s guide to blockchain: Blurring the line between physical and digital Part oneInternal audit’s role in thedigital revolutionWhile blockchain may be the next step in thedigital evolution, specific implementationsof blockchain technology are still susceptibleto emerging and existing risks. Thesedevelopments will require Internal Auditto play a pivotal role in not only providingtraditional assurance, but also acting as atrusted business adviser and anticipating/evaluating newer risks to the organization.As a new emerging technology, blockchainwill continue to be evaluated for its use. Therate of adoption of blockchain technologymay differ for each company. Therefore, thepreparedness level of each Internal Auditfunction to respond to the risks posedwill also vary. But the overall challengeremains the same: Staying current on therisks and opportunities that come alongwith technological advancements suchas blockchain.ContactsSandy PundmannUS Managing Partner, Internal AuditDeloitte & Touche LLPspundmann@deloitte.comAdam RegelbruggePartner, Internal AuditDeloitte & Touche LLParegelbrugge@deloitte.comManu MankadManaging Director, Internal AuditDeloitte & Touche LLPmmankad@deloitte.comSeth ConnorsSenior Manager and Deloitte Blockchain FellowDeloitte & Touche LLPsconnors@deloitte.comRajat BhattacharyaSenior Manager, Internal AuditDeloitte & Touche LLPrbhattacharya@deloitte.comAmitesh JoshiSpecialist Master, Internal AuditDeloitte & Touche LLPamjoshi@deloitte.comEndnotes1.Rajesh Kandaswamy and David Furlonger, Blockchain Primer for 2018, Gartner, February 1, n-primer-.2.Linda Pawczuk, Rob Massey, and David Schatsky, Breaking blockchain open: Deloitte’s 2018 global blockchainsurvey, Deloitte Development LLC, 2018, ockchain-survey-report.pdf.3.The innovation imperative: Forging Internal Audit’s path to greater impact and influence, Deloitte ToucheTohmatsu Limited, May 2018, d-influence.html.7
About DeloitteDeloitte refers to one or more of Deloitte Touche Tohmatsu Limited, a UK privatecompany limited by guarantee (“DTTL”), its network of member firms, and theirrelated entities. DTTL and each of its member firms are legally separate andindependent entities. DTTL (also referred to as “Deloitte Global”) does not provideservices to clients. In the United States, Deloitte refers to one or more of the USmember firms of DTTL, their related entities that operate using the “Deloitte” namein the United States and their respective affiliates. Certain services may not beavailable to attest clients under the rules and regulations of public accounting.Please see www.deloitte.com/ about to learn more about our global network ofmember firms.This publication contains general information only and Deloitte is not, by means ofthis publication, rendering accounting, business, financial, investment, legal, tax, orother professional advice or services. This publication is not a substitute for suchprofessional advice or services, nor should it be used as a basis for any decisionor action that may affect your business. Before making any decision or taking anyaction that may affect your business, you should consult a qualified professionaladvisor. Deloitte shall not be responsible for any loss sustained by any person whorelies on this publication.Copyright 2019 Deloitte Development LLC. All rights reserved.
consensus models. This lack of trust requires consensus models to function effectively in normal and adversarial conditions. While this paper will not delve into the different types of consensus models, it is important for internal audit practitioners to understand some examples of issues that can result when an inappropriate consensus
Greene 2 Craig Hege AUDITOR (6 Yr.) 1 Greene 2 Cynthia Tobin AUDITOR (6 Yr.) 1 Greene 2 David Green AUDITOR (6 Yr.) 1 Greene 2 Deez Nuts AUDITOR (6 Yr.) 1 Greene 2 Derek Thomson AUDITOR (6 Yr.) 1 Greene 2 Dr. Andrea Malmont AUDITOR (6 Yr.) 1 Greene 2 Lapinski AUDITOR (6 Yr.) 1 Gree
In this context, the internal auditor is responsible for detecting financial errors and specifically by using the auditing standards (Bedard et al., 2015). Finally, it is worth to mention that the role of internal auditor depends on his practical abilities and professional training in detecting fraud (Petrascu & Tieanu, . Internal Auditor .
PENGARUH ETIKA AUDITOR, PENGALAMAN AUDITOR, FEE AUDIT, DAN MOTIVASI AUDITOR TERHADAP KUALITAS AUDIT (Studi pada Auditor KAP Di Semarang) SKRIPSI Diajukan sebagai salah satu syarat untuk menyelesaikan Program Sarjana (S1) pada Program Sarjana Fakultas Ekonomika dan Bisnis Universitas Diponegoro Disusun oleh: Andreani Hanjani NIM: 12030110130171
6. QMS 9001:2015 internal Audit It covers internal audit process, audit question techniques and guidelines for internal audit as well as auditor criteria. 7. Steps for QMS Internal Audit It covers steps to carry out Quality management system internal audit
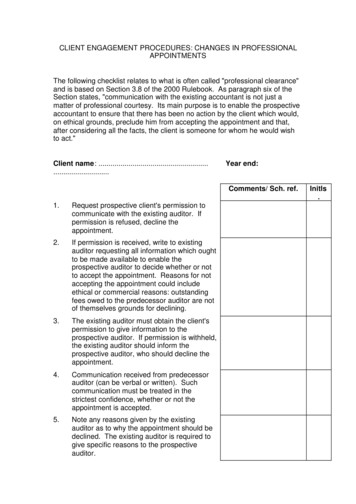
accepting the appointment could include ethical or commercial reasons: outstanding fees owed to the predecessor auditor are not of themselves grounds for declining. 3. The existing auditor must obtain the client's permission to give information to the prospective auditor. If permission is withheld, the existing auditor should inform the prospective auditor, who should decline the appointment .
requirements for IRCA QMS 2008 auditor certification. The British Standards Institution 2014 1 of 5 ISO 9001 Quality Management System Lead Auditor Training (IRCA) Course Description . BSI’s “Quality Management Systems (QMS) Auditor/Lead Auditor Training Course (ISO 9001)” course teaches the principles and
Role of the Lead Auditor Every audit has a lead auditor – even if it’s the only auditor! This person represents the team in communication with the auditee and management. The lead auditor also defines the requirements of each audit assignment, including qualification of other audit team members.
GTAG Global Technology Audit Guides HoA Head of Agency HoIA Head of Internal Audit IA Internal Audit / Internal Auditor IA-CM Internal Audit Capability Model IAS Internal Audit Service . Audit, the Code of Ethics for Internal Auditors and the Auditing Standards. The only way