Network Security Technologies And Solutions
CCIE Professional DevelopmentNetwork SecurityTechnologies and SolutionsYusuf Bhaiji, CCIE No. 9305Cisco PressCisco Press201 West 103rd StreetIndianapolis, IN 46290 USA
iiCCIE Professional DevelopmentNetwork Security Technologies and SolutionsYusuf BhaijiCopyright 2008 Cisco Systems, Inc.Published by:Cisco Press800 East 96th StreetIndianapolis, IN 46240 USAAll rights reserved. No part of this book may be reproduced or transmitted in any form or by any means, electronicor mechanical, including photocopying, recording, or by any information storage and retrieval system, without written permission from the publisher, except for the inclusion of brief quotations in a review.Printed in the United States of AmericaThird Printing September 2011Library of Congress Cataloging-in-Publication Data:Bhaiji, Fahim Hussain Yusuf.Network security technologies and solutions / Yusuf Bhaiji.p. cm.ISBN 978-1-58705-246-0 (pbk.)1. Computer networks--Security measures. I. Title.TK5105.59.B468 2008005.8--dc222008003231ISBN-13: 978-1-58705-246-6ISBN-10: 1-58705-246-6Warning and DisclaimerThis book is designed to provide information about network security technologies and solutions. Every effort hasbeen made to make this book as complete and as accurate as possible, but no warranty or fitness is implied.The information is provided on an “as is” basis. The authors, Cisco Press, and Cisco Systems, Inc. shall have neitherliability nor responsibility to any person or entity with respect to any loss or damages arising from the informationcontained in this book or from the use of the discs or programs that may accompany it.The opinions expressed in this book belong to the author and are not necessarily those of Cisco Systems, Inc.
iiiTrademark AcknowledgmentsAll terms mentioned in this book that are known to be trademarks or service marks have been appropriately capitalized. Cisco Press or Cisco Systems, Inc., cannot attest to the accuracy of this information. Use of a term in this bookshould not be regarded as affecting the validity of any trademark or service mark.Corporate and Government SalesThe publisher offers excellent discounts on this book when ordered in quantity for bulk purchases or special sales,which may include electronic versions and/or custom covers and content particular to your business, training goals,marketing focus, and branding interests. For more information, please contact:U.S. Corporate and Government Sales 1-800-382-3419 corpsales@pearsontechgroup.comFor sales outside the United States please contact: International Sales international@pearsoned.comFeedback InformationAt Cisco Press, our goal is to create in-depth technical books of the highest quality and value. Each book is craftedwith care and precision, undergoing rigorous development that involves the unique expertise of members from theprofessional technical community.Readers’ feedback is a natural continuation of this process. If you have any comments regarding how we couldimprove the quality of this book, or otherwise alter it to better suit your needs, you can contact us through e-mail atfeedback@ciscopress.com. Please make sure to include the book title and ISBN in your message.We greatly appreciate your assistance.PublisherAssociate PublisherCisco RepresentativeCisco Press Program ManagerExecutive EditorManaging EditorDevelopment EditorProject EditorCopy EditorTechnical EditorsEditorial AssistantBook and Cover DesignerCompositionIndexerProofreaderPaul BogerDave DusthimerAnthony WolfendenJeff BradyBrett BartowPatrick KanouseBetsey HenkelsSan Dee PhillipsBarbara HachaNairi Adamian, Kevin Hofstra, Gert DeLaetVanessa EvansLouisa AdairMark ShirarTim WrightKaren A. Gill
ivAbout the AuthorYusuf Bhaiji, CCIE No. 9305 (Routing and Switching and Security), has been with Cisco for sevenyears and is currently the program manager for the Cisco CCIE Security Certification and CCIE proctorin Cisco Dubai Lab. Prior to this, he was technical lead for the Sydney TAC Security and VPN team.Yusuf’s passion for security technologies and solutions has played a dominant role in his 17 years ofindustry experience, from as far back as his initial master’s degree in computer science, and has sincebeen reflected in his numerous certifications.Yusuf prides himself in his knowledge-sharing abilities, which are evident in the fact that he has mentoredmany successful candidates, as well as having designed and delivered a number of Network Securitysolutions around the globe.Yusuf is an advisory board member of several nonprofit organizations for the dissemination of technologies and promotion of indigenous excellence in the field of internetworking through academic and professional activities. Yusuf chairs the Networkers Society of Pakistan (NSP) and IPv6 Forum Pakistanchapter.Yusuf has also authored a Cisco Press publication titled CCIE Security Practice Labs (ISBN1587051346), released in early 2004. He has been a technical reviewer for several Cisco Press publications and written articles, white papers, and presentations on various security technologies. He is a frequent lecturer and well-known speaker presenting in several conferences and seminars worldwide.About the Technical ReviewersNairi Adamian, CCIE Security No. 10294, has been with Cisco since 1999 and currently is a technicalsupport manager at Cisco, Australia. She leads a team of customer support engineers at the Cisco Technical Assistance Center (TAC). She holds a bachelor’s degree in computing science from University ofTechnology, Sydney, and has an MBA from Macquarie Graduate School of Management.Kevin Hofstra, CCIE No. 14619, CCNP, CCDP, CCSP, CCVP, manages a network engineering unitwithin the Air Force Communications Agency of the U.S. Department of Defense. Mr. Hofstra isresponsible for designing, implementing, and optimizing DoD networks and has deployed as a civilianengineer to Iraq, Kuwait, and Qatar in support of Operation Iraqi Freedom. Mr. Hofstra has a computerscience degree from Yale University and a master of engineering degree in telecommunications and amaster of engineering management degree from the University of Colorado.Gert DeLaet, CCIE No. 2657, is a product manager for the CCIE team at Cisco. Gert was a contributing author to CCIE Security Exam Certification Guide and CCDA Exam Certification Guide from CiscoPress. He resides in Brussels, Belgium.
vDedicationsThis book is dedicated to my beloved wife, Farah. Without her support and encouragement, I could nothave completed this book.AcknowledgmentsI would like to thank my family for all their continuous support and encouragement, and especially myfather, Asghar Bhaiji, for his wisdom. Last but not least, I reminisce about my mother, Khatija Bhaiji,whose love is ever shining on me.I would like to especially thank the technical reviewers, Nairi Adamian, Gert DeLaet, and KevinHofstra, who have done an amazing job in contributing to this book. Their valuable feedback and effortsto research each topic are greatly appreciated in the accomplishment of this project.I extend my sincere gratitude to Brett Bartow and the entire development team—Betsey Henkels, DaynaIsley, Barbara Hacha, San Dee Phillips, Chris Cleveland, and members of the Cisco Press team workingon this project, whose expert guidance has been a determining factor in the completion of this book.I would like to take this opportunity to thank my manager, Sarah DeMark, the leadership team of Learning@Cisco group, and my colleagues at Cisco for their support in writing this book and every otherproject. I have benefited greatly from working with them and am honored to be a member of this team.Finally, I would like to thank you, the reader of this book, for helping me to make this book a success.
viThis Book Is Safari EnabledThe Safari Enabled icon on the cover of your favorite technology book meansthe book is available through Safari Bookshelf. When you buy this book, you getfree access to the online edition for 45 days.Safari Bookshelf is an electronic reference library that lets you easily searchthousands of technical books, find code samples, download chapters, and accesstechnical information whenever and wherever you need it.To gain 45-day Safari Enabled access to this book: Go to http://www.ciscopress.com/safarienabled Complete the brief registration form Enter the coupon code SJGV-KMZF-ENN5-ITFN-EYITIf you have difficulty registering on Safari Bookshelf or accessing the onlineedition, please e-mail customer-service@safaribooksonline.com.
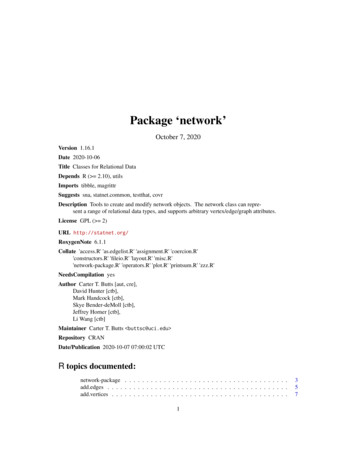
viiContents at a GlanceForewordxxxiiIntroductionxxxiiiPart IPerimeter Security 3Chapter 1Overview of Network Security 5Chapter 2Access Control 21Chapter 3Device Security 53Chapter 4Security Features on Switches 83Chapter 5Cisco IOS Firewall 113Chapter 6Cisco Firewalls: Appliance and Module 139Chapter 7Attack Vectors and Mitigation Techniques 207Part IIIdentity Security and Access Management 265Chapter 8Securing Management Access 267Chapter 9Cisco Secure ACS Software and Appliance 289Chapter 10Multifactor Authentication 311Chapter 11Layer 2 Access Control 325Chapter 12Wireless LAN (WLAN) Security 347Chapter 13Network Admission Control (NAC) 373Part IIIData Privacy 405Chapter 14Cryptography 407Chapter 15IPsec VPN 423Chapter 16Dynamic Multipoint VPN (DMVPN) 469Chapter 17Group Encrypted Transport VPN (GET VPN) 503Chapter 18Secure Sockets Layer VPN (SSL VPN) 521Chapter 19Multiprotocol Label Switching VPN (MPLS VPN) 533Part IVSecurity Monitoring 559Chapter 20Network Intrusion Prevention 561Chapter 21Host Intrusion Prevention 613Chapter 22Anomaly Detection and Mitigation 639Chapter 23Security Monitoring and Correlation 669Part VSecurity Management 697Chapter 24Security and Policy Management 699Chapter 25Security Framework and Regulatory Compliance 747Index 770
viiiContentsForewordxxxiiIntroductionxxxiiiPart IPerimeter Security 3Chapter 1Overview of Network Security 5Fundamental Questions for Network SecurityTransformation of the Security Paradigm57Principles of Security—The CIA Model 8Confidentiality 9Integrity 9Availability 9Policies, Standards, Procedures, Baselines, Guidelines 9Security Policy 9Examples of Security Policies 10Standards 11Procedures 11Baselines 12Guidelines 12Security Models13Perimeter Security 13Is Perimeter Security Disappearing? 14The Difficulty of Defining Perimeter 14A Solid Perimeter Security Solution 14Security in Layers 15Multilayer Perimeter SolutionThe Domino Effect 16Security WheelSummaryReferencesChapter 2171919Access Control 21Traffic Filtering Using ACLs 21ACL Overview 21ACL Applications 21When to Configure ACLs 2315
ixIP Address Overview 23Classes of IP Addresses 24Understanding IP Address Classes 24Private IP Address (RFC 1918) 26Subnet Mask Versus Inverse Mask OverviewSubnet Mask 28Inverse Mask 2827ACL Configuration 29Creating an ACL 29Assigning a Unique Name or Number to Each ACLApplying an ACL to an Interface 30Direction of the ACL 32Understanding ACL Processing 32Inbound ACL 32Outbound ACL 33Packet Flow Rules for Various Packet TypesGuidelines for Implementing ACLs 3633Types of Access Lists 36Standard ACLs 37Extended ACLs 38IP Named ACLs 39Lock and Key (Dynamic ACLs) 40Reflexive ACLs 42Established ACLs 43Time-Based ACLs Using Time Ranges 44Distributed Time-Based ACLs 45Configuring Distributed Time-Based ACLs 45Turbo ACLs 46Receive ACLs (rACL) 46Infrastructure Protection ACLs (iACL) 47Transit ACLs 47Classification ACLs 48Debugging Traffic Using ACLs 49SummaryReferencesChapter 35050Device Security 53Device Security Policy53Hardening the Device 55Physical Security 5529
xPasswords 55Creating Strong Passwords 56Pass-Phrase Technique 56Password Encryption 57ROMMON Security 57User Accounts 60Privilege Levels 61Infrastructure ACL 62Interactive Access Methods 62Console Port 62VTY Ports 63VTY Access Using Telnet 63VTY Access Using SSH 64Auxiliary Port 65Banner Messages 65Cisco IOS Resilient Configuration 67Cisco Discovery Protocol (CDP) 68TCP/UDP Small-Servers 69Finger 69Identification (auth) Protocol 69DHCP and BOOTP Service 69Trivial File Transfer Protocol (TFTP) Server 70File Transfer Protocol (FTP) Server 70Autoloading Device Configuration 70PAD 70IP Source Routing 71Proxy Address Resolution Protocol (ARP) 71Gratuitous ARP 72IP Directed Broadcast 72IP Mask Reply 72IP Redirects 72ICMP Unreachable 73HTTP 73Network Time Protocol (NTP) 74Simple Network Management Protocol (SNMP) 75Auto-Secure Feature 75Securing Management Access for Security Appliance 76PIX 500 and ASA 5500 Security Appliance—Device Access Security 76Telnet Access 76SSH Access 77HTTPS Access for ADSM 77Authenticating and Authorizing Using Local and AAA Database 78
xiIPS 4200 Series Appliance Sensors (formerly known as IDS 4200)IPS Device Manager (IDM) 78HTTP/HTTPS Access 79Telnet and SSH Access 79Access Control List 79User Accounts 80Device Security Checklist 80Summary 81References 81Chapter 4Security Features on Switches 83Securing Layer 2 83Port-Level Traffic Controls 84Storm Control 84Protected Ports (PVLAN Edge) 85Private VLAN (PVLAN) 85Configuring PVLAN 89Port Blocking 91Port Security 92Access Lists on Switches 94Router ACL 94Port ACL 94VLAN ACL (VACL) 95VACL on a Bridged Port 95VACL on a Routed Port 95Configuring VACL 96MAC ACL 97Spanning Tree Protocol Features 98Bridge Protocol Data Unit (BPDU) Guard 98Root Guard 98EtherChannel Guard 99Loop Guard 99Dynamic Host Configuration Protocol (DHCP) SnoopingIP Source Guard102Dynamic ARP Inspection (DAI) 103DAI in a DHCP Environment 105DAI in a Non-DHCP Environment 106Rate Limiting Incoming ARP Packets 106ARP Validation Checks 10710078
xiiAdvanced Integrated Security Features on High-End Catalyst SwitchesControl Plane Policing (CoPP) FeatureCPU Rate LimitersReferencesChapter 5107109Layer 2 Security Best PracticesSummary107109110111Cisco IOS Firewall 113Router-Based Firewall Solution113Context-Based Access Control (CBAC)115CBAC Functions 116Traffic Filtering 116Traffic Inspection 116Alerts and Audit Trails 117How CBAC Works 117Packet Inspection 118Timeout and Threshold Values 118The Session State Table 118UDP Connections 119Dynamic ACL Entries 119Embryonic (Half-Open) Sessions 120Per-Host DoS Prevention 120CBAC-Supported Protocols121Configuring CBAC 122Step 1—Select an Interface: Internal or External 122Step 2—Configure an IP Access List 123Step 3—Define an Inspection Rule 123Step 4—Configure Global Timeouts and Thresholds 123Step 5—Apply the Access List and the Inspection Rule to an InterfaceStep 6—Verifying and Monitoring CBAC 126Putting It All Together 126IOS Firewall Advanced Features 127HTTP Inspection Engine 127E-Mail Inspection Engine 128Firewall ACL Bypass 129Transparent IOS Firewall (Layer 2) 130Virtual Fragmentation Reassembly (VFR) 130VRF-Aware IOS Firewall 131Inspection of Router-Generated Traffic 131125
xiiiZone-Based Policy Firewall (ZFW) 132Zone-Based Policy Overview 132Security Zones 133Configuring Zone-Based Policy Firewall 134Configuring ZFW Using Cisco Policy Language (CPL)Application Inspection and Control (AIC) 136SummaryReferencesChapter 6134137137Cisco Firewalls: Appliance and Module 139Firewalls Overview139Hardware Versus Software Firewalls140Cisco PIX 500 Series Security Appliances140Cisco ASA 5500 Series Adaptive Security AppliancesCisco Firewall Services Module (FWSM)142143Firewall Appliance Software for PIX 500 and ASA 5500Firewall Appliance OS Software145Firewall Modes 145Routed Firewall Mode 146Transparent Firewall Mode (Stealth Firewall)Stateful Inspection144146148Application Layer Protocol InspectionAdaptive Security Algorithm Operation148150Security Context 152Multiple Contexts—Routed Mode (with Shared Resources)Multiple Contexts—Transparent Mode 153Configuring Security Context 155Security Levels157Redundant Interface158IP Routing 159Static and Default Routes 159Static Route 160Static Route Tracking 160Default Route 161Equal Cost Multiple Path (ECMP) Forwarding162153
xivOpen Shortest Path First (OSPF) 163Configuring OSPF 164Securing OSPF 165Monitoring OSPF 166Routing Information Protocol (RIP) 167Configuring RIP 167Enhanced Interior Gateway Routing Protocol (EIGRP)Configuring EIGRP Stub Routing 169Securing EIGRP 169168Network Address Translation (NAT) 170NAT Control 171NAT Types 172Dynamic NAT 173Dynamic PAT 174Configure Dynamic NAT and PAT 176Static NAT 176Static Port Address Translation (PAT) 178Bypassing NAT When NAT Control Is Enabled 179Identity NAT (nat 0 Command) 179Static Identity NAT (static Command) 180NAT Exemption (nat 0 with ACL) 182Policy NAT 183Order of NAT Processing 184Controlling Traffic Flow and Network Access 185ACL Overview and Applications on Security Appliance 185Controlling Inbound and Outbound Traffic Through the Security Appliance byUsing Access Lists 186Step 1—Defining an Access List 186Step 2—Applying an Access List to an Interface 186Simplifying Access Lists with Object Groups 188Modular Policy Framework (MPF) 190Configuring MPF 190Step 1—Identifying Traffic Flow 190Step 2—Creating a Policy Map 191Step 3—Applying a Policy 191Cisco AnyConnect VPN ClientRedundancy and Load BalancingFailover Requirements 194Failover Link 194State Link 194192193
xvFailover Implementation 195Serial Cable Failover Link (PIX 500 Series Only)LAN-Based Failover Link 197Asymmetric Routing Support (ASR) 197196Firewall “Module” Software for Firewall Services Module (FWSM)Firewall Module OS Software199Network Traffic Through the Firewall ModuleInstalling the FWSM198199200Router/MSFC Placement 200In Single Context 200In Multiple Context Mode 201Configuring the FWSMSummaryReferencesChapter 7202204205Attack Vectors and Mitigation Techniques 207Vulnerabilities, Threats, and ExploitsClasses of Attacks 208Attack Vectors 208Attackers Family 210Risk Assessment 211207Mitigation Techniques at Layer 3 212Traffic Characterization 212Using an ACL to Characterize ICMP Flood or Smurf AttackUsing an ACL to Characterize SYN Attacks 215IP Source Tracker 219How IP Source Tracker Works 219Configuring IP Source Tracker 220IP Spoofing Attacks 220Antispoofing with Access Lists 221Antispoofing with uRPF 222Antispoofing with IP Source Guard 222Packet Classification and Marking Techniques 224Committed Access Rate (CAR) 225How CAR Works 225Configuring Committed Access Rate (CAR) 226Modular QoS CLI (MQC) 227Traffic Policing 229212
xviNetwork-Based Application Recognition (NBAR) 230Protocol Discovery 230Packet Description Language Module (PDLM) 231Configuring NBAR 231TCP Intercept 232How TCP Intercept Works 232Configuring TCP Intercept 233TCP Intercept on Firewall 234Policy-Based Routing (PBR) 234Unicast Reverse Path Forwarding (uRPF) 236How uRPF Works 236Configuring uRPF 238NetFlow 239How NetFlow Works 240Configuring NetFlow 240NetFlow Ecosystem 241Mitigation Techniques at Layer 2 242CAM Table Overflow—MAC Attack 242Background 242The Problem 242CAM Table Overflow Attack Mitigation 243MAC Spoofing Attack 243Background 243The Problem 243MAC Spoofing Attack Mitigation 244ARP Spoofing Attack 245Background 245The Problem 245ARP Spoofing Attack Mitigation 245VTP Attack 246Background 246The Problem 246VTP Attack Mitigation 247VLAN Hopping Attack 247Background 247The Problem 248VLAN Hopping Attack Mitigation 249PVLAN Attack 249Background 249The Problem 250PVLAN Attack Mitigation 251Spanning-Tree Attacks 252Background 252
xviiThe Problem 253Spanning-Tree Attacks Mitigation 253DHCP Spoofing and Starvation Attacks 253Background 253The Problem 253DHCP Spoofing and Starvation Attacks Mitigation802.1x Attacks 254Background 254The Problem 255802.1x Attacks Mitigation 255254Security Incident Response Framework 256What Is a Security Incident? 256Security Incident Response Process 257Incident Response Team (IRT) 257Security Incident Response Methodology 258Step 1—Planning and Preparation 259Step 2—Identification and Classification 260Step 3—Reaction 260Step 4—Postmortem and Follow-Up 260Step 5—Archiving 261SummaryReferences262262Part IIIdentity Security and Access Management 265Chapter 8Securing Management Access 267AAA Security Services 267AAA Paradigm 268Authentication 268Authorization 269Accounting 269AAA Dependencies 269Authentication Protocols 270RADIUS (Remote Authentication Dial-In User Service) 270RADIUS Packet 271RADIUS Communication 271RADIUS Security 273TACACS (Terminal Access Controller Access Control System)TACACS Packet 275TACACS Communication 276TACACS Security 277Comparison of RADIUS and TACACS 278274
xviiiImplementing AAA 278AAA Methods 279Authentication Methods 280Authorization Methods 280Accounting Methods 281Server Groups 281Service Types for AAA FunctionsAuthentication Services 282Authorization Services 283Accounting Service 284282Configuration Examples 285PPP Authentication, Authorization, and Accounting Using RADIUS 285Login Authentication and Command Authorization and Accounting UsingTACACS 285Login Authentication with Password Retry Lockout 286SummaryReferencesChapter 9287287Cisco Secure ACS Software and Appliance 289Cisco Secure ACS Software for Windows 289AAA Server: Cisco Secure ACS 290Protocol Compliance 291Advanced ACS Functions and Features 293Shared Profile Components (SPC) 293Downloadable IP ACLs 293Network Access Filter (NAF) 294RADIUS Authorization Components 294Shell Command Authorization Sets 294Network Access Restrictions (NAR) 295Machine Access Restrictions (MAR) 295Network Access Profiles (NAP) 296Cisco NAC Support 296Configuring ACS297Cisco Secure ACS ApplianceSummaryReferences309309307
xixChapter 10Multifactor Authentication 311Identification and Authentication311Two-Factor Authentication System 312One-Time Password (OTP) 312S/KEY 313Countering Replay Attacks Using the OTP Solution 313Attributes of a Two-Factor Authentication System 314Smart Cards and Tokens 314RSA SecurID 315Cisco Secure ACS Support for Two-Factor Authentication Systems 315How Cisco Secure ACS Works 316Configuring Cisco Secure ACS for RADIUS-Enabled Token Server 317Configuring Cisco Secure ACS for RSA SecurID Token Server 321SummaryReferencesChapter 11322322Layer 2 Access Control 325Trust and Identity Management Solutions326Identity-Based Networking Services (IBNS)Cisco Secure ACS 328External Database Support 329327IEEE 802.1x 329IEEE 802.1x Components 330Port States: Authorized Versus UnauthorizedEAP Methods 334332Deploying an 802.1x Solution 334Wired LAN (Point-to-Point) 334Wireless LAN (Multipoint) 335Implementing 802.1x Port-Based Authentication 337Configuring 802.1x and RADIUS on Cisco Catalyst Switches Running Cisco IOSSoftware 337Enabling Multiple Hosts for a Noncompliant Access Point Terminating on theSwitch 338RADIUS Authorization 338Configuring 802.1x and RADIUS on Cisco Aironet Wireless LAN Access PointRunning Cisco IOS 342Supplicant Settings for IEEE 802.1x on Windows XP Client 343
xxSummaryReferencesChapter 12344344Wireless LAN (WLAN) Security 347Wireless LAN (WLAN) 347Radio Waves 347IEEE Protocol Standards 348Communication Method—Radio Frequency (RF)WLAN Components 349348WLAN Security 350Service Set Identifiers (SSID) 351MAC Authentication 352Client Authentication (Open and Shared Key) 352Static Wired Equivalent Privacy (WEP) 353WPA, WPA2, and 802.11i (WEP Enhancements) 353IEEE 802.1x and EAP 355EAP Message Digest 5 (EAP-MD5) 356EAP Transport Layer Security (EAP-TLS) 357EAP Tunneled Transport Layer Security (EAP-TTLS) 359EAP Flexible Authentication via Secure Tunneling (EAP-FAST)Protected EAP (PEAP) 362Cisco Lightweight EAP (LEAP) 364EAP Comparison Chart 365WLAN NAC 366WLAN IPS 367VPN IPsec 367Mitigating WLAN Attacks367Cisco Unified Wireless Network Solution 368Components of Cisco Unified Wireless NetworkSummaryReferencesChapter 13369370371Network Admission Control (NAC) 373Building the Self-Defending Network (SDN)373Network Admission Control (NAC) 375Why NAC? 375Cisco NAC 376Comparing NAC Appliance with NAC FrameworkCisco NAC Appliance Solution 378Mechanics of Cisco NAC Appliance 379NAC Appliance Components 379NAC Appliance Deployment Scenarios 380378359
xxiCisco NAC Framework Solution 382Mechanics of the Cisco NAC Framework SolutionNAC Framework Components 386NAC Framework Deployment Scenarios 391NAC Framework Enforcement Methods 392Implementing NAC-L3-IP 394Implementing NAC-L2-IP 396Implementing NAC-L2-802.1x 399SummaryReferences402403Part IIIData Privacy 405Chapter 14Cryptography 407Secure Communication 407Cryptosystem 407Cryptography Overview 408Cryptographic Terminology 408Cryptographic Algorithms 410Symmetric Key Cryptography 410Asymmetric Key Cryptography 412Hash Algorithm 416Virtual Private Network (VPN)SummaryReferencesChapter 15420421421IPsec VPN 423Virtual Private Network (VPN) 423Types of VPN Technologies 423Secure VPN (Cryptographic VPN) 424Trusted VPN (Non-Cryptographic VPN) 424Hybrid VPN 425Types of VPN Deployment 425IPsec VPN (Secure VPN) 425IPsec Request for Comments (RFCs) 426Generic IPsec RFCs 426IPsec Protocols RFCs 427IPsec Key Exchange RFCs 427IPsec Cryptographic Algorithm RFCs 428IPsec Policy-Handling RFCs 430IPsec Modes 430383
xxiiIPsec Protocol Headers 432IPsec Anti-Replay Service 434ISAKMP and IKE 435Understanding IKE (Internet Key Exchange) ProtocolIKEv2 (Internet Key Exchange—Version 2) 438ISAKMP Profiles 441IPsec Profiles 443IPsec Virtual Tunnel Interface (IPsec VTI) 443435Public Key Infrastructure (PKI) 445PKI Components 446Certificate Enrollment 447Implementing IPsec VPN 449Cisco IPsec VPN ImplementationsSite-to-Site IPsec VPN 451Remote Access IPsec VPN 455Cisco Easy VPN 456Dynamic VTI (DVTI) 461SummaryReferencesChapter 16449465466Dynamic Multipoint VPN (DMVPN) 469DMVPN Solution Architecture 469DMVPN Network Designs 470DMVPN Solution Components 472How DMVPN Works 473DMVPN Data Structures 474DMVPN Deployment Topologies475Implementing DMVPN Hub-and-Spoke Designs 476Implementing Single Hub Single DMVPN (SHSD) Topology 477Implementing Dual Hub Dual DMVPN (DHDD) Topology 483Implementing Server Load-Balancing (SLB) Topology 484Implementing Dynamic Mesh Spoke-to-Spoke DMVPN Designs 486Implementing Dual Hub Single DMVPN (DHSD) Topology 488Implementing Multihub Single DMVPN (MHSD) Topology 498Implementing Hierarchical (Tree-Based) Topology 499SummaryReferences500501
xxiiiChapter 17Group Encrypted Transport VPN (GET VPN) 503GET VPN Solution Architecture 503GET VPN Features 504Why GET VPN? 505GET VPN and DMVPN 506GET VPN Deployment Consideration 507GET VPN Solution Components 507How GET VPN Works 509IP Header Preservation 511Group Member ACL 512Implementing Cisco IOS GET VPNSummaryReferencesChapter 18513519519Secure Sockets Layer VPN (SSL VPN) 521Secure Sockets Layer (SSL) Protocol521SSL VPN Solution Architecture 522SSL VPN Overview 523SSL VPN Features 523SSL VPN Deployment ConsiderationSSL VPN Access Methods 525SSL VPN Citrix Support 527Implementing Cisco IOS SSL VPNCisco AnyConnect VPN ClientSummaryReferencesChapter 19524528530531531Multiprotocol Label Switching VPN (MPLS VPN) 533Multiprotocol Label Switching (MPLS) 533MPLS Architecture Overview 534How MPLS Works 534MPLS VPN and IPsec VPN 536Deployment Scenarios 538Connection-Oriented and Connectionless VPN TechnologiesMPLS VPN (Trusted VPN)540Comparison of L3 and L2 VPNs540539
xxivLayer 3 VPN (L3VPN) 542Components of L3VPN 543How L3VPN Implementation WorksHow VRF Tables Work 543Implementing L3VPNLayer 2 VPN (L2VPN)543544551Implementing L2VPN 553Implementing Ethernet VLAN over MPLS Service—Using VPWS BasedArchitecture 553Implementing Ethernet VLAN over MPLS Service—Using VPLS-BasedArchitecture 554SummaryReferences556557Part IVSecurity Monitoring 559Chapter 20Network Intrusion Prevention 561Intrusion System Terminologies561Network Intrusion Prevention OverviewCisco IPS 4200 Series Sensors562563Cisco IDS Services Module (IDSM-2)565Cisco Advanced Inspection and Protection Security Services Module (AIP-SSM)Cisco IPS Advanced Integration Module (IPS-AIM)Cisco IOS IPS569Deploying IPS570Cisco IPS Sensor OS Software568572Cisco IPS Sensor Software 574Sensor Software—System Architecture 574Sensor Software—Communication Protocols 575Sensor Software—User Roles 576Sensor Software—Partitions 577Sensor Software—Signatures and Signature EnginesSensor Software—IPS Events 580Sensor Software—IPS Event Actions 582Sensor Software—IPS Risk Rating (RR) 583Sensor Software—IPS Threat Rating 584Sensor Software—IPS Interfaces 585578567
xxvSensor Software—IPS Interface Modes 589Sensor Software—IPS Blocking (Shun) 593Sensor Software—IPS Rate Limiting 594Sensor Software—IPS Virtualization 595Sensor Software—IPS Security Policies 596Sensor Software—IPS Anomaly Detection (AD)IPS High Availability 598IPS Fail-Open Mechanism 599Failover Mechanism 599Fail-Open and Failover DeploymentsLoad-Balancing Technique 600IPS Appliance Deployment Guidelines597600600Cisco Intrusion Prevention System Device Manager (IDM)Configuring IPS Inline VLAN Pair ModeConfiguring IPS Inline Interface Pair Mode601604Configuring Custom Signature and IPS BlockingSummaryReferencesChapter 21601609610611Host Intrusion Prevention 613Securing Endpoints Using a Signatureless MechanismCisco Security Agent (CSA)614CSA Architecture 615CSA Interceptor and Correlation 616CSA Correlation Extended Globally 618CSA Access Control Process 618CSA Defense-in-Depth—Zero-Day ProtectionCSA Capabilities and Security Functional RolesCSA Components613619619622Configuring and Managing CSA Deployment by Using CSA MCManaging CSA Hosts 624Managing CSA Agent Kits 626Managing CSA Groups 630CSA Agent User Interface 632CSA Policies, Rule Modules, and Rules 635SummaryReferences636637623
xxviChapter 22Anomaly Detection and Mitigation 639Attack Landscape 639Denial-of-Service (DoS) Attack Defined 639Distributed Denial-of-Service (DDoS) Attack—DefinedAnomaly Detection and Mitigation Systems641Cisco DDoS Anomaly Detection and Mitigation SolutionCisco Traffic Anomaly DetectorCisco Guard DDoS Mitigation641643644647Putting It All Together for Operation649Configuring and Managing the Cisco Traffic Anomaly Detector 653Managing the D
Chapter 15 IPsec VPN 423 Chapter 16 Dynamic Multipoint VPN (DMVPN) 469 Chapter 17 Group Encrypted Transport VPN (GET VPN) 503 Chapter 18 Secure Sockets Layer VPN (SSL VPN) 521 Chapter 19 Multiprotocol Label Switching VPN (MPLS VPN) 533 Part IV Security Monitoring 559 Chapter 20 Network Intrusion Prevention 561 Chapter 21 Host Intrusion .
Integrated Security Technologies and Solutions - Volume I. Jamie is a dynamic presenter and is a Cisco Live Distinguished Speaker. Prior to Cisco, Jamie had various roles, including director of a cyber security practice, senior security consultant, and senior network engineer. vi Integrated Security Technologies and Solutions - Volume II
security in application, transport, network, link layers Network Security 8-3 Chapter 8 roadmap 8.1 What is network security? 8.2 Principles of cryptography 8.3 Message integrity 8.4 Securing e-mail 8.5 Securing TCP connections: SSL 8.6 Network layer security: IPsec 8.7 Securing wireless LANs 8.8 Operational security
3 CONTENTS Notation 10 Preface 12 About the Author 18 PART ONE: BACKGROUND 19 Chapter 1 Computer and Network Security Concepts 19 1.1 Computer Security Concepts 21 1.2 The OSI Security Architecture 26 1.3 Security Attacks 27 1.4 Security Services 29 1.5 Security Mechanisms 32 1.6 Fundamental Security Design Principles 34 1.7 Attack Surfaces and Attack Trees 37
Network Security Groups Network Security Groups are used to provide traffic control at the packet level. You can filter network traffic to and from Azure resources in an Azure virtual network with a network security group. A network security group contains security rules that allo
network.edgecount Return the Number of Edges in a Network Object network.edgelabel Plots a label corresponding to an edge in a network plot. network.extraction Extraction and Replacement Operators for Network Objects network.indicators Indicator Functions for Network Properties network.initialize Initialize a Network Class Object
Cisco security Plus exam. CP-755, section sA11-QC Cisco network security i: routing ios security Emphasizes overall security processes, includ - ing basic and advanced security vulnerabilities, hands-on skills in security policy design and management, security technologies, architec-ture, products, solutions, and design.
Quantum Security is a North American company that supplies and installs high quality physical security barriers across the United States, Canada and Mexico. We provide access control solutions - ranging from security gates and burglar bar doors to roll down window security and hallway security gates - to a wide range of
security challenges that are on the forefront of 5G and need prompt security measures. We further discuss the security solutions for the threats described in this paper. The rest of the paper is organized as follows: Section II describes the key security challenges followed by security solutions for the highlighted security challenges in .