Cyber Security In A Digital Business World - PwC
Cyber securityin a digitalbusiness worldPutting security at the centreof New Zealand organisationsThe Global State of Information Security Survey 201768%of cyber security leaders will investmore in security as their businessmodel evolves.44%are using managed security services21%report that suppliers and businesspartners were the source of a cyberattack in the last 12 monthswww.pwc.co.nz/gsiss2017
ContentsThe cyber challenge ofdigital business4Data privacy as acompetitive advantage5Finding new solutionsto old cyber concerns7Get in touchThe regulatoryimperative68Executive summaryThe megatrend of technological breakthroughs ishere to stay. It’s already reshaped entire industriesand now every organisation is facing a very dynamicrisk profile as they look to realise the manyopportunities that technology presents. The rise ofdigital business models also means that every NewZealand organisation is exposed to an evolving levelof digital risk, either from customers and employeesor from relationships they have up and down theirsupply chain.Digital business models aren’t just limited to internetbusinesses either – we’ve seen in recent years acomplete transformation in both front- and backoffice functions. In fact, it’s often these back-endfunctions where the greatest prize is for cyberattackers.In New Zealand we are experiencing the naturalgrowing pains that come with the widespreadadoption of cloud computing, big data, social mediaand mobile technologies. None of these technologiesare inherently risky in themselves, but that canchange given certain contexts and settings. What’smore, the next generation of wearables, along withthe Internet of Things (IoT) more broadly, willfurther transform the way we approach cybersecurity and privacy.These trends have come through clearly in ourresearch. While we’ve seen local businesses continueto invest in cyber security, we still lag behindcomparable economies. What’s more, our spendingon cyber security is less aligned to business functionsand value than overseas firms and isn’t as focused onwhat specific controls work best for the organisation’scritical information and systems.The adoption of cloud is driven by the ability ofbusinesses of any size to leverage efficiencies, scaleand functionality that was previously beyond theirreach. Which is why our adoption of this technologyis well ahead of the rest of the world. The need now isfor kiwi businesses is to ensure their security andprivacy efforts expand at the same pace as theirbroader business and digital activities.In every organisation, context is key. In order toinvest effectively, organisations have to take apersonalised approach to their cyber security, onethat is specific to their business needs, their existingdigital ecosystem and their relationships withbusiness partners.This is the first of four white papers we will releaseover the next 12 months that explore different anglesof the 2017 Global State of Information SecuritySurvey. I’d like to thank all of our New Zealandrespondents who took part in this year’s survey – the19th we have published – and I hope you enjoy ourextended coverage of this important issue.Adrian van HestPartner and Cyber Practice Leader
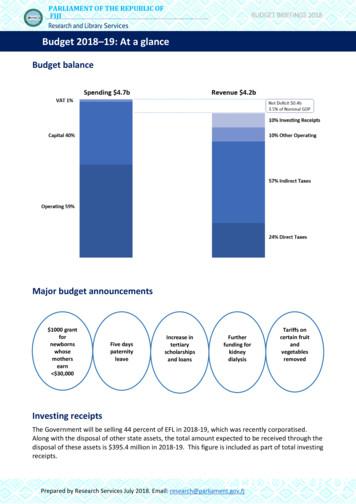
PwC Global State of Information Survey3The state of cyber in New ZealandThe cyber security response from businessesCurrently in placeComplianceaudits ofthird partiesThe majority of cyber security spending isn’taligned with business revenue:A priority for the next12 months29%37%46%SecurityStrategy forbig dataAlignedNot alignedNew Zealand25%21%20.5%20.5%39%45%New Zealand24%Global59%The digital business ecosystem is reshaping cyber securityin New Zealand:57% are investingDon’t know68% will invest in new56% will invest more inAustraliaimprovedmore in security security needscollaborationrelated to evolvingbusiness models betweenbusiness, digitalin the next 12 monthsand IT over the next8%19%73%12 monthsAcross the board, New Zealand companies are responding to agreater range of threatsSecurity incidents are originating from:Current employeesSuppliers/business partners42%36%17%10%47%Current service providersGlobal21%20%Unknown hackers19%38%24%63%201647%2017How New Zealand’s digital businesses compare to Australia’sWe use managedsecurity servicesOpen source software is having awidespread impact on digitalorganisations, bersecurityPreventing Making it easierto customisevendorinfrastructurelock-inWe are currentlyimplementing an IoTsecurity strategy39%39%YesNew ZealandWe have a securitystrategy for the Internetof Things in place20%
4The cyber challenge ofdigital businessHow companies think about their digital assets ischanging. No longer a matter of isolated IT assets,companies are now developing complex, multifaceted digital ecosystems. There’s now no aspect ofa business’s operations that can’t be translated into adigital equivalent, allowing businesses to loweroperating costs, raise employee productivity andscale their operations quickly. The result is a digitalbusiness presence that is not only larger than everbut also has increasingly blurred lines between acompany and its suppliers, not to mention thepersonal presence of their customers and employees.The ability of cloud platforms to deliverfunctionality, storage and processing power, all withno significant capital investment has played a hugerole in creating this ecosystem, providing aframework for businesses to go truly digital.However rapid adoption and simplistic assumptionsabout how it works and just what is secure meansthere is often quite a gap between an organisation’sassumed and actual level of risk.This is proving especially true in New Zealand,where cloud adoption is among the highest in theworld. In fact, 90 per cent of our respondentsidentified they are using some form of cloudcomputing model, either public, private or hybrid.Alongside cloud services, companies are alsomoving into other foundational elements for theirdigital presence, from big data and mobile devicesthrough to social media, all of which are creatingnew data concerns. Despite this, Kiwi companies arehalf as likely as the global average to have a big datasecurity strategy (21 per cent compared to 45 percent).Cloud computing has helped to underpin anotherhallmark of the digital business: Bring Your OwnDevice (BYOD) policies. While these policiesrepresent a valuable way for companies to makework more flexible, they also further blur theboundaries of a company’s digital footprint. In NewZealand, companies are struggling with the securityimplications of BYOD, ranking below the globalaverage for having a security strategy in place forpersonal devices used in the workplace.New Zealand firms are more likely to develop asecurity policy in-house, rather than outsource it toa third party (8 per cent locally compared to 27 percent globally and 32 per cent in Australia).As a result, companies are running the risk ofsaddling themselves with legacy systems andpractices that can’t protect them against new risks,that don’t scale up as the business expands and thataren’t based on industry best practice.Of course, outsourcing isn’t the only method fordigital businesses to improve their cyber security.Relying on open-source technology, both for generalbusiness solutions and also to protect the business’sdata, is an increasingly popular global solution.Open-source has certainly caught on in recent years,with 40 per cent of New Zealand businesses usingopen-sourced software to avoid vendor lock-in, whileallowing them to easily undertake new IT projects.However, compared to our global respondents, NewZealand organisations are considerably less likely touse open source technology or recognise theopportunity it offers to improve their cyber securityefforts. This lack of awareness about the potentialapplications and benefits of open-source softwarerepresents a missed opportunity for New Zealand’spublic and private sectors, although this may be anissue of scale.Safeguarding digital businessIn this digital ecosystem companies have to bemindful that every supplier and service provider is apotential avenue for a cyber attack, and that theyneed to take appropriate steps and hold them toaccount for any breaches.
PwC Global State of Information SurveyData privacyas acompetitiveadvantageWe now generate more data than ever before across multipleconnected devices. More importantly, it has become easierthan ever for people to access that information, eitherlegitimately or as the result of a cyber attack.For sensitive data, the risk posed by a cyber attack hasmorphed from one that is purely operational to one thatsegues across a company’s brand, reputation, businesscontinuity planning, staff and customer relationships. As aresult, data privacy is increasingly being seen internationallyas a key competitive advantage – something that customersand clients now expect.New Zealand organisations are just now realising that theyare no longer seen as the victim in the event of a data breach,but regarded as someone who has abused their client’s trust inthem. From a customer’s perspective, data privacy isn’t anoptional extra, it’s a core component of their willingness topurchase from a business. They are also more willing thanever to hold organisations to account for breaching theirprivacy. Despite this, local companies are struggling to putsafeguards in place to protect the data they gather. In NewZealand, only 42 per cent currently inventory personal datafrom customers and employees, 11 percentage points behindthe global average.Having qualified staff is one part of the puzzle for digitalbusinesses, the other is the third parties that a businesspartners with. Only half (48 per cent) of New Zealandbusinesses require the third parties they work with to complywith their privacy policies. The message here is clear – whileprivacy policies are an important first step in protectingcustomer data, these standards cannot be implemented inisolation - they have to be applied across every aspect of anorganisation’s operations. Effectively this demands a culturalshift across the organisation, equivalent to the strides NewZealand is making in health and safety.5
6The regulatoryimperativeTo date, regulators have been playing catch-upwith changes in our ability to generate andcapture data. Despite this, overseas regulation hascontinued to evolve and digital businesses are nowrecognising the need to not only conform to thedata privacy requirements of their home market,but also those of any overseas territories they areworking in. This is where New Zealand’s lack ofregulation and enforcement hurts us as adestination for digital business.Sixty-four per cent of our Kiwi respondents saidthe reason they have a privacy function is tomaintain compliance with regulation. That’sconsiderably more than the global average(50 per cent) and that of Singapore (56 per cent),a regional economy roughly the same size asNew Zealand.What’s also interesting is what New Zealandcompanies aren’t focusing on. Many globalrespondents (31 per cent) identified that theirprivacy function allows them to get more use outof the data they collect, through better marketinginitiatives, for example. Only 26 per cent of ourlocal respondents identified the same benefit,lower than both Australia and Singapore. In thesecountries, privacy is seen as a way to stand out andappeal to customers who are increasinglyprotective of their data – in New Zealand it’streated solely as a question of compliance.Companies collecting information globally arefacing an increasingly complicated regulatoryenvironment as different jurisdictions introducelegislation to protect their citizens’ data. TheEuropean Union, South Korea, Hong Kong andSingapore have all introduced new data protectionregulations – reflecting a greater awareness acrossNew Zealand’s major trading partners of theimportance of data security. While we might liketo think of digital businesses as being borderless,the increasing complexity of cyber securitylegislation is changing the way businesses manageprivacy concerns.By comparison, New Zealand’s lack of mandatorydisclosures and reporting around data breachesputs us behind many of our major tradingpartners. There is a long-term risk that, withoutupdates to local legislation, New Zealandbusinesses are unprepared to operate in globalmarkets, while the country also becomes lessattractive for companies looking to do businesshere.Responding to changing regulationAmong the key responses NZ organisations are taking to privacy regulations, these are three of the most popular:New ZealandAustraliaGlobal54%34%38% 36%Updating privacy policiesand procedures38%32%Privacy assessments34%28%Improving privacygovernance27%
PwC Global State of Information SurveyFinding new solutionsto old cyber concernsAwareness of cyber security has been growingyear-on-year, and organisations in New Zealandare now more aware than ever of how exposedthey are to cyber risks and how their operationswill be affected if (or when) they are the victim ofa cyber attack. The next challenge that many localorganisations are now struggling with istranslating high-level awareness into a deeperunderstanding of the breadth and depth of riskstheir organisation is facing.Globally this is happening. The conversation ischanging to focus less on knee-jerk reactions andmore on establishing the frameworks andarchitectures that can reduce a company’slong-term exposure to cyber crime. Thesecompanies have a holistic cyber strategy toidentify, protect, detect and respond to the risksthey face. Driving this approach is a leadershipteam who aren’t just aware of cyber risks but whounderstand the breadth of possible threat actorsand are actively championing cyber security.Locally, companies will have to keep up with thisshift and invest in the same best-practices that weare seeing internationally. New Zealandbusinesses that haven’t already implemented adata use framework will have to do so, while thosethat have will need to update the framework astheir digital footprint changes with newtechnologies. This process will allow them toaddress any redundancies in their IT architecture.Likewise, the growth in cyber attacks fromemployees and business partners underscores thenew areas of focus for local companies. Localorganisations now have to develop a collaborativestrategy that crosses both organisational silos andthe traditional “perimeter security” that stoodbetween a company and its third-party serviceproviders. To achieve this, 56 per cent are lookingto increase the collaboration that occurs betweenbusiness, IT and digital. Context is key here – asuccessful strategy won’t be an out-of-the-boxsolution, but carefully tailored to match theorganisation’s structure and digital presence.Digital organisations will have to invest more intomanaging the data lifecycle. In New Zealand, only39 per cent of our respondents will be investing inan accurate inventory of how personal data iscollected and used.Finally, New Zealand firms have to be moreselective when it comes to the third-parties theywork with. The percentage of respondentsexperiencing security breaches from suppliers hasdoubled in the last year and will keep growing inthe future. Formulating a response has to startwith the context – where their data is and who(both within the business and externally) hasaccess to it. From there, they can begin to developa range of advanced security techniques that willallow them to prevent, detect and recover from acyber attack, regardless of its origins.Future opportunities:Bake a cyber security framework into new digital initiatives: Retrofitting digital infrastructure withsecurity measures will never be as effective as building these features in from the start.Invest in detecting and responding to new types of cyber attacks: Local companies are over-relianton penetration tests compared to the rest of the world and have to diversify into more advanced tools likerisk-based authentication/authorization, while also addressing the risk posed by staff and suppliers.Move away from solely in-house cyber security: New Zealand firms rely more on in-house measuresthan their global counterparts. Outsourced expertise, open source security software and scalable thirdparty tools can all provide a more effective security solution – and are all measures that overseas firms areactively pursuing.Be ready to respond. Success or failure in cyber security comes down to how well companies respondafter a breach.7
Get in touchAdrian van HestPartner and Cyber Practice LeaderT: 64 4 462 7109E: adrian.p.van.hest@nz.pwc.comSteve McCabePartnerT: 64 4 462 7050E: steve.c.mccabe@nz.pwc.comCampbell McKenzieDirectorT: 64 9 355 8040E: campbell.b.mckenzie@nz.pwc.comMethodologyThe Global State of Information Security Survey is our annual cyber security publication, polling97 cyber security specialists and decision-makers from across New Zealand as part of a global surveyof more than 10,000 experts in this area. This year’s findings will be published as four whitepapersthroughout the 2017 financial year. The results are published in conjunction with CIO Magazine.pwc.co.nz 2016 PricewaterhouseCoopers New Zealand. All rights reserved. ‘PwC’ and ‘PricewaterhouseCoopers’ refer to the New Zealand member firm,and may sometimes refer to the PwC network. Each member firm is a separate legal entity. Please see www.pwc.com/structure for further details.
Cyber security in a digital business world 68% of cyber security leaders will invest more in security as their business model evolves. 44% are using managed security services 21% report that suppliers and business partners were the source of a cyber attack in the last 12 months www.pwc.co.nz/gsiss2017 Cyber security in a digital business world
the 1st Edition of Botswana Cyber Security Report. This report contains content from a variety of sources and covers highly critical topics in cyber intelligence, cyber security trends, industry risk ranking and Cyber security skills gap. Over the last 6 years, we have consistently strived to demystify the state of Cyber security in Africa.
What is Cyber Security? The term cyber security refers to all safeguards and measures implemented to reduce the likelihood of a digital security breach. Cyber security affects all computers and mobile devices across the board - all of which may be targeted by cyber criminals. Cyber security focuses heavily on privacy and
Cyber Vigilance Cyber Security Cyber Strategy Foreword Next Three fundamental drivers that drive growth and create cyber risks: Managing cyber risk to grow and protect business value The Deloitte CSF is a business-driven, threat-based approach to conducting cyber assessments based on an organization's specific business, threats, and capabilities.
Cyber Security Training For School Staff. Agenda School cyber resilience in numbers Who is behind school cyber attacks? Cyber threats from outside the school Cyber threats from inside the school 4 key ways to defend yourself. of schools experienced some form of cyber
Cyber crimes pose a real threat today and are rising very rapidly both in intensity and complexity with the spread of internet and smart phones. As dismal as it may sound, cyber crime is outpacing cyber security. About 80 percent of cyber attacks are related to cyber crimes. More importantly, cyber crimes have
DHS Cyber Security Programs Cyber Resilience Review (CRR) Evaluate how CIKR providers manage cyber security of significant information services and assets Cyber Infrastructure Survey Tool (C-IST) Identify and document critical cyber security information including system-level configurations and functions, cyber security threats,
risks for cyber incidents and cyber attacks.” Substantial: “a level which aims to minimise known cyber risks, cyber incidents and cyber attacks carried out by actors with limited skills and resources.” High: “level which aims to minimise the risk of state-of-the-art cyber attacks carried out by actors with significant skills and .
Artificial Intelligence shaping the future of the built environment The ability of computers is transforming our lives at an increasing rate. The prospect of machines that can think, rather than just do, is something we are beginning to take for granted. The transformative power of artificial intelligence (AI) to change the infrastructure sector is only just beginning, but now is the time to .