National Protection And Programs Directorate Department Of Homeland .
The Office of Infrastructure ProtectionNational Protection and Programs DirectorateDepartment of Homeland SecurityProtective Security Coordination DivisionProtective Security Advisor Program and DHS Services9/6/2018
Protective Security Advisors PSAs are non-regulatory, field-deployed personnel who serve as criticalinfrastructure security and resilience advisors Link State, local, tribal, and territorial (SLTT) and private sector partnersto DHS resources and services Coordinate vulnerability assessments, training, and other DHS products andservices Share information in steady state, during special events and incidents Assist facility owners and operators with obtaining security clearances During contingency events, PSAs support the response, recovery, andreconstitution efforts Man state and local emergency operations centers Serve as pre-designated Infrastructure Liaisons (IL) at Joint Field Offices2
Protective Security Advisor LocationsCourtesy of DHS3
PSA CrattyPSA Turzanski
Protected Critical InfrastructureInformation Established under the CriticalInfrastructure Information Act of2002 Protects voluntarily submitted criticalinfrastructure information from: Freedom of Information Act State and local sunshine laws Civil litigation proceedings Regulatory usage Provides private sector with legalprotections and “peace of mind.”Courtesy of DHS5
Enhanced Critical InfrastructureProtection Visit Establishes and enhances DHS’s relationship with criticalinfrastructure owners and operators During an Enhanced Critical Infrastructure Protection (ECIP)visit, PSAs focus on coordination, outreach, training, andeducation ECIP visits include local, state, and federal response andsupport partners to enable everyone to gain a betterunderstanding of the site and enable us all to move forwardtogether Perfect one stop shop to meet the local players of importance6
Infrastructure Survey Tool The IST is a web-based vulnerability survey tool that appliesweighted scores to identify infrastructure vulnerabilities andtrends across sectors Collects data for a snapshot in time for sites for feedback Physical Security, Security Force, Security Management,Information Sharing, Protective Measures, Dependencies The Dashboard tool allows facility owners and operators to: Compare a facility’s security in relation to similar facilities Identify security gaps Track progress toward improving critical infrastructure security7
Example Dashboard - Protection8
Active Shooter: Preparation and ResponsePresentations 1-hr. based on 2012 Joint DHS/FBI Bulletin and best practices Background Information on personalities that perpetrate theseattacks Propensity towards violence, mental illness, triggering point To aid employees and disrupt possible events Planning Individual mental maps Organizational plans Response – Situationally based: Run, Hide or Fight Recovery – based on plans and profound nature of attack Also 3-hr TTX available9
Counter-IED Training & Awareness Diverse curriculum of training designed to buildcounter-IED core capabilities, such as: IED Counterterrorism Workshop Surveillance Detection Bomb Threat Management Vehicle-Borne IED (VBIED) Search Protective Measures IED Search Procedures Increases knowledge and ability to detect,prevent, protect against, and respond tobombing threatsCourtesy of DHS OBP10
Homeland Security InformationNetwork (HSIN) HSIN (https://hsin.dhs.gov/) is DHS’s primary technology tool for trustedinformation sharing HSIN – Critical Infrastructure (HSIN-CI) enables direct communicationbetween: DHS Federal, State, and local governments Critical infrastructure owners and operators Content includes: Planning and Preparedness Incident Reporting and Updates Situational Awareness Education and Training11
Infrastructure Protection Report Series Increase awareness of theinfrastructure mission andbuild a baseline of securityand resilience knowledgethroughout the Nation Identify CommonVulnerabilities, PotentialIndicators of TerroristActivity, and associatedProtective Measures, alongwith actions that can beundertaken to enhanceresilienceCourtesy of DHS12
DHS/IP – PartnersInfraGard An information-sharing and analysis effort serving theinterests and combining the knowledge of a widerange of members Partnership between FBI and private sector Businesses, academic institutions, state and local lawenforcement agencies, and other participantsdedicated to sharing information and intelligence toprevent/mitigate acts against the United States http://www.infragard.net13
See Something Say Something Nationwide Suspicious ActivityReporting Initiative (NSI) States control most localprograms with information andposters available Customized products can alsobe obtained DHS support in preparation ofmaterial, posters, etc Contact seesay@hq.dhs.gov
Private Sector Resources Catalog www.dhs.gov/private-sector-resources-catalog All DHS agencies have available material Training- FEMA, Active Shooter, Workplace Violence, Surveillance Detection Information- Homeland Security Information Network, TripWire, National Terrorism AlertSystem, National Suspicious Activity Reporting Services- Wireless Priority Service (WPS)/Government Emergency Telephone System(GETS), Geographic Information Systems Systems-Protected Critical Infrastructure Information, Chemical Facility AntiTerrorism Standards, Business Continuity Cyber – Assessments, bulletins, and best practices
DHS Cyber Security Programs Cyber Hygiene Evaluations Assess Internet accessible systems for known vulnerabilities andconfiguration errors ICS Architecture Review Intensive and exhaustive review of the security architecture forindustrial control, process automation, and other cyber-physicalsystems Penetration Test/Risk and Vulnerability Assessment Conducts red-team assessments and provides remediationrecommendations
DHS Cyber Security Programs Cyber Resilience Review (CRR) Evaluate how CIKR providers manage cyber security of significantinformation services and assets Cyber Infrastructure Survey Tool (C-IST) Identify and document critical cyber security information includingsystem-level configurations and functions, cyber security threats,cyber security measures, IT business continuity/disaster recoveryand cyber security organizational management Cyber Security Evaluation Tool (CSET) Self-assessment using recognized standards http:/us-cert.gov/control systems/csetdownload.html
DHS Cyber Security Programs - CSET Network Mapping System comparisons to chosen standards Hard copy reports Resource library
Cyber Security Contact InformationEvaluation Inquiriescse@hq.dhs.govGeneral Inquiriescyberadvisor@hq.dhs.govDepartment of Homeland SecurityNational Protection and Programs DirectorateOffice of Cybersecurity and Communications
For more information visit:www.dhs.gov/critical-infrastructureBob Winters - bob.winters@dhs.govProtective Security Advisor - PittsburghNationally – psaoperations@hq.dhs.gov
DHS Cyber Security Programs Cyber Resilience Review (CRR) Evaluate how CIKR providers manage cyber security of significant information services and assets Cyber Infrastructure Survey Tool (C-IST) Identify and document critical cyber security information including system-level configurations and functions, cyber security threats,
DES Directorate of Economics and Statistics DFPD Department of Food & Public Distribution . xi DGCI&S Directorate General of Commercial Intelligence & Statistics DMI Directorate of Marketing and Inspection DMS Delhi Milk Scheme E Estimated EARAS Establishment of an Agency for
U.S. Army Test and Evaluation Command . Directorate Command Brief 05 August 2018. Agenda OTC Organization Directorate Mission Directorate History Test Parachutist Overview Customers Supported Task Organization . T-6 Training (Air to Air Video) *Redstone Test Center Safety – Risk Mitigation Individual .
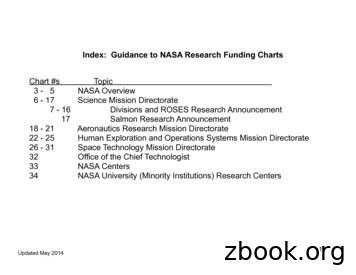
6 - 17 Science Mission Directorate 7 - 16 Divisions and ROSES Research Announcement 17 Salmon Research Announcement 18 - 21 Aeronautics Research Mission Directorate 22 - 25 Human Exploration and Operations Systems Mission Directorate 26 - 31 Space Technology Mission Directorate 32 Office of the Chief Technologist
Annual activity report 2018 DG PRES, European Parliament 1 EXECUTIVE SUMMARY Directorate General for the Presidency . Annual activity report 2018 DG PRES, European Parliament 2 EXECUTIVE SUMMARY TABLE OF CONTENTS 1. EXECUTIVE SUMMARY 4 2. ENVIRONMENT OF THE DIRECTORATE-GENERAL, OBJECTIVES AND RESULTS 7 2.1 The Directorate-General (m ission statement, operational context) 7 2.2 Key results and .
377th ABW Kirtland AFB, N.M. Nuclear operations, base support AFRL Aerospace Systems Directorate WPAFB, Ohio R&D Air Force Office of Scientific Research Arlington, Va. Research Directed Energy Directorate Kirtland AFB, N.M. R&D Information Directorate Rome, N.Y. R&D Materials and Manufacturing Directorate WPAFB, Ohio R&D
Electronic Sensors Product Realization Directorate ECBC NNSSCC TARDEC Intelligence & Information Warfare 4 UNCLASSIFIED Directorate Directorate Current Operations Principal Deputy Counter IED CERDEC Flight Activity EW Air/Ground Survivability Div ision Radar & Combat ID Div ision Cyber/ Offensive Operations Div ision SIGINT & Quick Reaction .
NASA SPACE TECHNOLOGY MISSION DIRECTORATE - Dr. Michael Gazarik, Associate Administrator, Space Technology Mission Directorate Dr. Michael Gazarik, NASA Associate Administrator for the Space Technology Mission Directorate (STMD), provided the update. He said STMD is the newest directorate at NASA, a little over a year old.
2016 Surface Operations Workshop Response Directorate 2 . Ground Rules This Workshop should be Interactive, NOT . Surface Operations Division National Response Directorate . Coxswains/owners are responsible for ensuring the facility inspection will be current on the date of the mission 2016 Surface Operations Workshop Response .