Network-Free documents Library
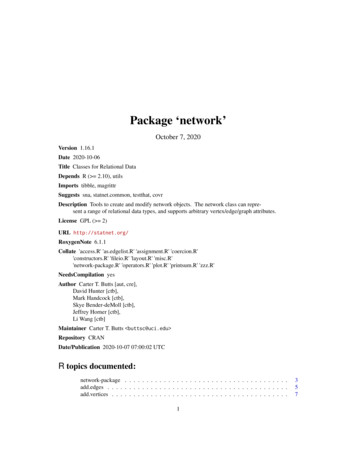
network.edgecount Return the Number of Edges in a Network Object network.edgelabel Plots a label corresponding to an edge in a network plot. network.extraction Extraction and Replacement Operators for Network Objects network.indicators Indicator Functions for Network Properties network.initialize Initialize a Network Class Object
Certified Network Defense (CND) Outline . Module 01: Computer Network and Defense Fundamentals Network Fundamentals Computer Network Types of Network Major Network Topologies Network Components Network Interface Card
Old Objectives (N10-005) New Objectives (N10-006) Network Concepts 1 Network Architecture Network Installation & Configuration 2 Network Operations Network Media & Topologies 3 Network Security Network Management 4 Troubleshooting Network Sec
FOR NETWORK FUNCTIONS VIRTUALIZATION NETWORK FUNCTIONS VIRTUALIZATION: A PRIMER 3 VIRTUALIZING NETWORK FUNCTIONS: COULD NFV MEAN NETWORK NIRVANA? NEW MODELS New Management Models Needed for NFV When a cadre of giant global network oper-ators started the initiative known as Network Functions Virtualization (NFV) in late 2012,
Administrator Guide SolarWinds Orion Network Atlas 14 Installing Orion Network Atlas 3. In the Network Map resource, click Download Network Atlas. Note: If you do not see a Download Network Atlas link in your Network Map resource, click Edit, and then check the Show Network Atlas Download link option on the Edit Network Map resource page
Subnetting, VLSM, and IPv6 161 3. Refer to Figure 8.2. All routers in the network have been config-ured with the ip subnet-zero command. Which subnet addresses should be used for Network A and Network B? (Choose two.) FIGURE 8.2 Network diagram. A. Network A – 192.168.1.112/25 B. Network A – 192.168.1.112/26 C. Network A – 192.168.1.128/25
CSCE515 – Computer Network Programming Host and Network Addresses A single network interface is assigned a single IP address called the host address. A host may have multiple interfaces, and therefore multiple host addresses. Hosts that share a network all have the same IP network address (the network ID). Dis
What is the Oracle Social Network add-in for Outlook? 14-2 How do I download and install the add-in for Outlook? 14-2 How do I log-in to the add-in for Outlook? 14-2 How do I get to Oracle Social Network? Oracle Social Network. Oracle Social Network. 1-3. 2. network? Social Network.
Key Reasons to Download SolarWinds Network Topology Mapper (NTM): Automate network discovery and diagramming Modular scanning - Build multiple maps from a single network scan . Easy export to popular formats - Visio , PNG, PDF [and Orion Network Atlas] PCI & HIPAA compliant network documentation -Robust reporting tools Inventory report .
Premier Network Narrow access to care, fewer providers Greater potential out-of-network impact, lower premiums Kaiser Permanente Network Exclusive network of providers and facilities. 6 Sample Broad Network Map Sample Premier Network Map Kaiser Permanente Network Map. 7 2018 Medical Plan Designs Design Feature 2014 - 2018 LM HealthWorks
Network Automation 101 Ivan Pepelnjak ([email protected]) Network Architect . Lack of programming skills Lack of reliable automation tools and programmatic interfaces . NetworkAutomation 101 Network Programmability 101 Network Automation Tools Network Automation Use Cases.
The Wired Home Network and Wi-Fi Home Network is actually the same Network. Your naming and use may / can be different. See Figure 1 - Overview Diagram. Figure 1 - Overview Diagram With this setup, the Home Network (both Wired and Wi-Fi) is able to initiate connections / communicate with devices on both the Wired IOT Network and the Wi-Fi IOT .
Hidden gems
- Tous Les Sites De Paris Sportifs Belgique
- Site De Paris Sportif Belgique
- Meilleur Casino Belgique En Ligne
- Site Paris Sportif Belgique
- Casino App
- Specialiste Tennis Paris Sportif
- Plinko Game Avis
- ライブ カジノ
- オンラインカジノ 本人確認不要
- オンラインカジノ 出金早い
- KYC 미인증 카지노
- 稼げるカジノ アプリ
- 비트코인 스포츠베팅
- Nhà Cái Châu âu
- Scommesse Crypto
- Scommesse In Crypto
- Nouveau Casino En Ligne Avec Bonus Sans Dépôt
- Avis Cresus Casino
- Bonus Casino En Ligne
- Casino Sans Depot
- Bonus Sans Dépôt Nouveau Casino
- 연령 인증 없는 카지노사이트
- Siti Non Aams
- Meilleur Casino En Ligne Français
- Siti Non Aams Sicuri
- Migliori Casino Non Aams
- Siti Scommesse Stranieri Legali
- Meilleur Casino Live Francais
- Trang Cá độ Bóng đá
- 안전한 코인카지노
- Meilleur Casino En Ligne France
- Casino En Ligne
- Meilleurs Casino En Ligne
- Site De Casino En Ligne
- Casino En Ligne
- Casino En Ligne Fiable
- Nouveau Casino En Ligne 2026
- Nouveaux Casinos En Ligne
- Crypto Trusted Online Casino Malaysia 2026
- Top Malaysia Online Casino Sites