Cisco 800, 1900, 2900, 3900 Series Integrated Service .
Cisco ISR STAugust 2011Cisco 800, 1900, 2900, 3900Series Integrated ServiceRouters (ISR)Security TargetRevision 1.0August 20111
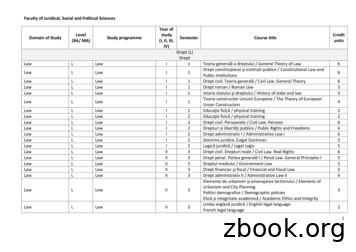
Cisco ISR STAugust 2011Table of Contents1SECURITY TARGET INTRODUCTION . 61.1 ST and TOE Reference . 61.2 Acronyms and Abbreviations . 61.3 TOE Overview . 71.3.1 TOE Product Type . 71.3.2 Supported non-TOE Hardware/ Software/ Firmware . 81.4 TOE DESCRIPTION . 81.5 Physical Scope of the TOE. 81.6 Logical Scope of the TOE . 101.6.1 Identification and Authentication . 101.6.2 Secure Management . 111.6.3 Information Flow Control . 111.6.4 Cryptography . 121.6.5 Secure Auditing . 121.7 TOE Evaluated Configuration . 121.7.1 Excluded Functionality . 132Conformance Claims . 142.1 Common Criteria Conformance Claim . 142.2 Protection Profile Conformance . 142.2.1 Protection Profile Refinements . 142.2.2 Protection Profile Additions . 142.3 Protection Profile Conformance Claim Rationale. 152.3.1 TOE Appropriateness. 152.3.2 TOE Security Problem Definition Consistency . 152.3.3 Statement of Security Objectives Consistency . 162.3.4 Statement of Security Requirements Consistency . 173SECURITY PROBLEM DEFINITION . 193.13.23.34SECURITY OBJECTIVES . 224.14.25Assumptions . 19Threats . 19Organizational Security Policies . 21Security Objectives for the TOE . 22Security Objectives for the Environment . 23SECURITY REQUIREMENTS . 245.1 Conventions. 245.2 TOE Security Functional Requirements . 245.3 SFRs Drawn from pp fw tf br v1.1. 255.3.1 Security audit (FAU). 255.3.2 Cryptographic Support (FCS) . 275.3.3 User data protection (FDP) . 275.3.4 Identification and authentication (FIA) . 295.3.5 Security management (FMT) . 305.3.6 Protection of the TSF (FPT) . 315.4 SFRs in addition to the SFRs found in pp fw tf br v1.1 . 312
Cisco ISR STAugust 20115.4.1 Cryptographic Support (FCS) . 315.4.2 User data protection (FDP) . 355.4.3 Security management (FMT) . 385.4.4 TOE Access (FTA) . 385.4.5 Trusted Path/Channel (FTP) . 395.5 TOE SFR Dependencies Rationale for SFRs Found in pp fw tf br v1.1. 395.6 TOE SFR Dependencies for SFRs in addition to the SFRs found inpp fw tf br v1.1. 395.7 Security Assurance Requirements . 405.7.1 SAR Requirements. 405.7.2 Security Assurance Requirements Rationale . 415.8 Assurance Measures . 416TOE Summary Specification. 436.16.27TOE Security Functional Requirement Measures . 43TOE Bypass and interference/logical tampering Protection Measures . 48RATIONALE . 507.17.27.3Rationale for TOE Security Objectives . 50Rationale for the Security Objectives for the Environment . 52Rationale for requirements/TOE Objectives . 52Annex A: References . 573
Cisco ISR STAugust 2011List of TablesTable 1: ST and TOE Identification. 6Table 2: Acronyms . 6Table 3: IT Environment Components . 8Table 4: TOE Hardware Models (1) . 9Table 5: TOE Hardware Models (2) . 9Table 6: TOE Hardware Models (3) . 10Table 7: TOE Provided Cryptography . 12Table 8: Excluded Functionality . 13Table 9: Protection Profiles . 14Table 10: Protection Profile Refinements . 14Table 11: Protection Profile Threat/OSP Additions . 16Table 12: Protection Profile Security Objective Additions . 16Table 13: Protection Profile Security Objective Additions . 17Table 14 TOE Assumptions . 19Table 15 Threats . 20Table 16 Security Objectives for the TOE . 22Table 17 Security Objectives for the Environment. 23Table 18 Security Functional Requirements . 24Table 19 Security Functional Requirements . 25Table 20: Dependency Rationale . 39Table 21: Assurance Measures . 40Table 22: Assurance Measures . 41Table 23: How TOE SFRs Measures . 43Table 24: Threat/Policies/Objectives Mappings . 50Table 25: Threat/Policies/TOE Objectives Rationale . 50Table 26: Threats/Environment Objectives Mappings . 52Table 27: Assumptions/Threats/Objectives Rationale . 52Table 28: Objective to Requirements Mappings . 53Table 29: Objectives to Requirements Rationale. 54Table 30: References. 574
Cisco ISR STAugust 2011DOCUMENT INTRODUCTIONPrepared By:Cisco Systems, Inc.170 West Tasman Dr.San Jose, CA 95134This document provides the basis for an evaluation of a specific Target of Evaluation(TOE), the Cisco 800, 1900, 2900, 3900 Series Integrated Service Routers (ISR). ThisSecurity Target (ST) defines a set of assumptions about the aspects of the environment, alist of threats that the product intends to counter, a set of security objectives, a set ofsecurity requirements, and the IT security functions provided by the TOE which meet theset of requirements.REVISION HISTORYRev1.0DateAugust 2011DescriptionInitial Release5
Cisco ISR ST1August 2011SECURITY TARGET INTRODUCTIONThe Security Target contains the following sections: Security Target Introduction [Section 1]Conformance Claims [Section 2]Security Problem Definition [Section 3]Security Objectives [Section 4]IT Security Requirements [Section 5]TOE Summary Specification [Section 6]Rationale [Section 7]The structure and content of this ST comply with the requirements specified in theCommon Criteria (CC), Part 1, Annex A, and Part 3, Chapter 4.1.1ST and TOE ReferenceThis section provides information needed to identify and control this ST and its TOE.Table 1: ST and TOE IdentificationST TitleST VersionPublication DateVendor and ST AuthorTOE ReferenceTOE Hardware ModelsTOE Software VersionKeywords1.2Cisco 800, 1900, 2900, 3900 Series Integrated Service Routers (ISR) SecurityTarget1.0August 2011Cisco Systems, Inc.Cisco 800, 1900, 2900, 3900 Series Integrated Service Routers (ISR)Cisco 881 ISR, Cisco 881G ISR, Cisco 891 ISR, Cisco 1905 ISR, Cisco 1921 ISR,Cisco 1941 ISR, Cisco 2901 ISR, Cisco 2911 ISR, Cisco 2921 ISR, Cisco 2951 ISR,Cisco 3925 ISR, Cisco 3925E ISR, Cisco 3945 ISR, Cisco 3945E ISR15.1.2T3Router, Data Protection, Authentication, FirewallAcronyms and AbbreviationsThe following acronyms and abbreviations are used in this Security Target:Table 2: AcronymsAcronyms initionAdministration, Authorization, and AccountingAdvanced Encryption StandardCommon Criteria for Information Technology Security EvaluationCommon Evaluation Methodology for Information Technology SecurityConfiguration ManagementDynamic Host Configuration ProtocolEvaluation Assurance LevelEthernet High-Speed WICHyper-Text Transport Protocol SecureIntegrated Service Router6
Cisco ISR STAugust 2011Acronyms /AbbreviationsITOSPPpp fw tf br mation TechnologyOperating SystemProtection ProfileU.S. Government Protection Profile for Traffic Filter Firewall in Basic RobustnessEnvironmentsSecure Hash StandardSecure Shell (version 2)Security TargetTransport Control ProtocolTSF Scope of ControlTOE Security FunctionTOE Security PolicyWide Area NetworkWAN Interface CardTOE OverviewThe Cisco 800, 1900, 2900, 3900 Series Integrated Service Routers (ISR) TOE is apurpose-built, routing platform that includes firewall and VPN functionality. The firewallfunctionality included within the TOE provides the functionality specified in the U.S.Government Protection Profile for Traffic Filter Firewall in Basic RobustnessEnvironments. The TOE includes fourteen (14) hardware models, Cisco 881 ISR, Cisco881G ISR, Cisco 891 ISR, Cisco 1905 ISR, Cisco 1921 ISR, Cisco 1941 ISR, Cisco 2901ISR, Cisco 2911 ISR, Cisco 2921 ISR, Cisco 2951 ISR, Cisco 3925 ISR, Cisco 3925EISR, Cisco 3945 ISR, and Cisco 3945E ISR.1.3.1 TOE Product TypeThe Cisco 800, 1900, 2900, 3900 Series Integrated Service Routers (ISR) are routerplatforms that provide connectivity and security services onto a single, secure device.These routers offer broadband speeds and simplified management to small businesses,and enterprise small branch and teleworkers.In support of the routing capabilities, the Cisco 800, 1900, 2900, 3900 Series IntegratedService Routers (ISR) provides IPSec connection capabilities for VPN enabled clientsconnecting through the Cisco 800, 1900, 2900, 3900 Series Integrated Service Routers(ISR).The Cisco 800, 1900, 2900, 3900 Series Integrated Service Routers (ISR) also supportsfirewall capabilities consistent with the U.S. Government Protection Profile for TrafficFilter Firewall in Basic Robustness Environments. The Cisco 800, 1900, 2900, 3900Series Integrated Service Routers (ISR) are single-device security and routing solutionsfor protecting the network. The firewall capabilities provided by the TOE are providedimplementing security zones. Zone-based firewall allows grouping of physical and virtualinterfaces into zones to simplify logical network topology. The creation of these zonesfacilitates the application of firewall policies on a zone-to-zone basis, instead of having toconfigure policies separately on each interface.7
Cisco ISR STAugust 20111.3.2 Supported non-TOE Hardware/ Software/ FirmwareThe TOE supports (in some cases optionally) the following hardware, software, andfirmware in its environment:Table 3: IT Environment ComponentsComponentRequiredRADIUS AAAServerYesManagementWorkstation withSSH ClientYesCertificateAuthorityYesVPN PeerNoNTP ServerNoWICYes for all modelsexcept: ISR 881, ISR881G, ISR 891Usage/Purpose Description for TOE performanceThis includes any IT environment RADIUS AAA server that providessingle-use authentication mechanisms. This can be any RADIUSAAA server that provides single-use authentication. The TOEcorrectly leverages the services provided by this RADIUS AAAserver to provide single-use authentication to administrators.This includes any IT Environment Management workstation with aSSH client installed that is used by the TOE administrator to supportTOE administration through SSH protected channels. Any SSH clientthat supports SSHv2 may be used.This includes any IT Environment Certificate Authority on the TOEnetwork. This can be used to provide the TOE with a valid certificateduring certificate enrollment.This includes any peer with which the TOE participates in VPNcommunications. VPN peers may be any device or software clientthat supports IPSec communications. Both VPN clients and VPNgateways are considered VPN peers by the TOE.The TOE supports communications with an NTP server. A solutionmust be used that supports MD5 hashing of communications with upto a 32 character key.Used for connecting to networks. These WICs interface with the TOEto provide the network interfaces that will be used by port adaptors tocommunicate on the network. Any Cisco WIC is supported.Examples include, Ethernet High-Speed WICs, Wireless High-SpeedWICs, Serial WICs, CSU/DSU WICs, and ISDN BRI WICs1.4 TOE DESCRIPTIONThis section provides an overview of the Cisco 800, 1900, 2900, 3900 Series IntegratedService Routers (ISR) Target of Evaluation (TOE). The TOE is comprised of severalhardware models, Cisco 881 ISR, Cisco 881G ISR, Cisco 891 ISR, Cisco 1905 ISR,Cisco 1921 ISR, Cisco 1941 ISR, Cisco 2901 ISR, Cisco 2911 ISR, Cisco 2921 ISR,Cisco 2951 ISR, Cisco 3925 ISR, Cisco 3925E ISR, Cisco 3945 ISR, and Cisco 3945EISR, running Cisco IOS Release 15.1.2.T3.1.5 Physical Scope of the TOEThe TOE is a hardware and software solution that makes up the following router modelsCisco 881 ISR, Cisco 881G ISR, Cisco 891 ISR, Cisco 1905 ISR, Cisco 1921 ISR, Cisco1941 ISR, Cisco 2901 ISR, Cisco 2911 ISR, Cisco 2921 ISR, Cisco 2951 ISR, Cisco3925 ISR, Cisco 3925E ISR, Cisco 3945 ISR, and Cisco 3945E ISR. The TOE iscomprised of the following:8
Cisco ISR STAugust 2011Table 4: TOE Hardware Models (1)HardwareSoftwareCisco 881 ISRc880-advipservicesk9Cisco 881G ISRc880-advipservicesk9Cisco 891 ISRc880advipservicesk9SizePowerInterfaces1.75 x 12.8 x 10.4 in.1.75 x 12.8 x 10.4 in.1.75 x 12.8 x 10.4 in.100 to 240 VAC10/100-Mbps FastEthernet4-port 10/100Mbps managedswitch(3) 802.11 b/gantennas100 to 240 VAC10/100-Mbps FastEthernet4-port 10/100Mbps managedswitch(3) 802.11 b/gantennas100 to 240 VAC(1) GigE(1) Fast Ethernet8-port 10/100Mbps managedswitch(3) 802.11 b/gantennasCisco 1905 ISRc880-advipservicesk9Cisco 1921 ISRc880-advipservicesk91.73 x 13.5 x 10.8 in.1.73 x 13.5 x 10.8 in.(1) slots for ITenvironment providedEHWICs(1) Serial WIC(1) USB Console Port(1) Serial Console Port(1) Auxilary Port(2) 10/100/1000 Port(2) slots for ITenvironment providedEHWICs(1) USB Console Port(1) Serial Console Port(1) Auxilary Port(2) 10/100/1000 PortTable 5: TOE Hardware Models (2)HardwareSoftwareCisco 1941 ISRc880-advipservicesk9Cisco 2901 ISRc880-advipservicesk9Cisco 2911 ISRc880-advipservicesk9Cisco 2921 ISRc880advipservicesk9Cisco 2951 ISRc880advipservicesk9Size1.73 x 13.5 x 10.8 in.1.72 x 17.5 x 16.5 in.1.75 x 17.25 x 16.4in.3.5 x 17.25 x 16.4in.3.5 x 17.25 x 16.4in.PowerWANInterfaces100 to 240 VAC(2) slots for ITenvironment providedEHWICs(1) USB Console Port(1) Serial Console Port(1) Auxilary Port(2) 10/100/1000 Port100 to 240 VAC(4) slots for ITenvironment providedEHWICs(1) USB Console Port(1) Serial ConsolePort(1) Auxilary Port(2) 10/100/1000 Port100 to 240 VAC(4) slots for ITenvironmentprovided EHWICs(1) Service moduleport(1) USB ConsolePort(1) Serial ConsolePort(1) Auxilary Port(3) 10/100/1000Port100 to 240 VAC(4) slots for ITenvironmentprovided EHWICs(1) SFP-basedports(2) Service moduleport(1) USB ConsolePort(1) Serial ConsolePort(1) Auxilary Port(3) 10/100/1000Port100 to 240 VAC(4) slots for ITenvironmentprovided EHWICs(1) SFP-basedports(2) Service moduleport(1) USB ConsolePort(1) Serial ConsolePort(1) Auxilary Port(3) 10/100/1000Port9
Cisco ISR STAugust 2011Table 6: TOE Hardware Models (3)HardwareSoftwareCisco 3925 ISRc880-advipservicesk9SizePowerWANInterfacesCisco 3925E ISRc880-advipservicesk9Cisco 3945 ISRc880-advipservicesk9Cisco 3945E ISRc880-advipservicesk93.5 x 17.1 x 14.7 in.3.5 x 17.1 x 14.7 in.5.25 x 17.25 x 16 in.5.25 x 17.25 x 16 in.100 to 240 VAC(4) slots for ITenvironment providedEHWICs(2) SFP-based ports(2) Service module port(1) USB Console Port(1) Serial Console Port(1) Auxilary Port(3) 10/100/1000 Port100 to 240 VAC(3) slots for ITenvironment providedEHWICs(2) SFP-based ports(2) Service module port(1) USB Console Port(1) Serial Console Port(1) Auxilary Port(4) GigE Port(4) 10/100/1000 Port100 to 240 VAC(4) slots for ITenvironment providedEHWICs(2) SFP-based ports(4) Service module port(1) USB Console Port(1) Serial Console Port(1) Auxilary Port(3) 10/100/1000 Port100 to 240 VAC(3) slots for ITenvironment providedEHWICs(2) SFP-based ports(4) Service module port(1) USB Console Port(1) Serial Console Port(1) Auxilary Port(4) GigE Port(4) 10/100/1000 Port1.6 Logical Scope of the TOEThe TOE is comprised of several security features. Each of the security featuresidentified above consists of several security functionalities, as identified below.1.2.3.4.5.Identification and AuthenticationSecure ManagementVPN and/or Firewall Information Flow ControlCryptographySecure AuditingThese features are described in more detail in the subsections below.1.6.1 Identification and AuthenticationThe TOE performs two types of authentication: device-level authentication of the remotedevice (VPN peers) and user authentication for the Authorized Administrator of the TOE.Device-level authentication allows the TOE to establish a secure channel with a trustedpeer. The secure channel is established only after each device authenticates itself. Devicelevel authentication is performed via IKE/IPSec mutual authentication. The TOEprovides authentication services for administrative users wishing to connect to the TOEssecure CLI administrative interface. The TOE requires authorized administrators toauthenticate prior to being granted access to any of the management functionality.The TOE optionally facilitates single use authentication for administrative usersattempting to connect to the TOE by invoking an external RADIUS AAA (ITenvironment) to provide single-use authentication. The TOE provides single useauthentication to administrative users of the TOE through the use of and external AAAserver. This is consistent with the rationale presented in US-PD 115.10
Cisco ISR STAugust 20111.6.2 Secure ManagementThe TOE provides secure administrative services for management of general TOEconfiguration and the security functionality provided by the TOE. All TOEadministration occurs either through a secure SSHv2 session via terminal server or via alocal console connection. The TOE provides the ability to securely manage all TOEadministrative users; all identification and authentication; all audit functionality of theTOE; all TOE cryptographic functionality; the timestamps maintained by the TOE; TOEconfiguration backup and recovery, and the information flow control policies enforced bythe TOE. The TOE supports two separate administrative roles: non-privilegedAdministrator and privileged Administrator. All of the security relevant managementfunctionality described in the paragraph above can only be performed by the privilegedAdministrator.When an administrative session is initially established, the TOE displays anAdministrator configurable warning banner. This is used to provide any informationdeemed necessary by the Administrator. Once a configured threshold of consecutiveauthentication failures is reached, the TOE locks-out the administrative user attempting tolog into the TOE until an administrator unlocks the administrator’s account. Anadministrative user cannot unlock their account. An administrative user must be unlockedby a different/separate privileged administrative user.1.6.3 Information Flow Control1.6.3.1 Firewall Information Flow ControlThe Cisco 800, 1900, 2900, 3900 Series Integrated Service Routers (ISR) mediateinformation flows through the TOE for unauthenticated information flows. The TOEprovides the ability to classify data flows into zones. Configurable allow or deny rulesets are applied to each information flow on a zone by zone basis. All security attributesare inspected based on the configurable rule set of the information flow. The TOE makesthe decision to allow or deny information flows based on the configured information flowrule set.The TOE ensures that all information flows from the TOE do not contain residualinformation from previous traffic. Packets are padded with zeros. Residual data isnever transmitted from the TOE.1.6.3.2 VPN Information Flow ControlCisco 800, 1900, 2900, 3900 Series Integrated Service Routers (ISR) deliver VPNconnections to remote entities. The VPN process includes remote device authentication,negotiation of specific cryptographic parameters for the session, and providing a secureconnection to and from the remote device. For inbound or outbound connections withexternal IT entities that are capable of supporting VPN (e.g., VPN clients and VPNgateways), the TOE will establish a secure connection. For other inbound or outbound11
Cisco ISR STAugust 2011traffic a secure connection will not be established, clear text traffic is explicitlyconfigured in this case.1.6.3.3 VLAN Information Flow ControlCisco 800, 1900, 2900, 3900 Series Integrated Service Routers (ISR) allow VLANconnections to/from remote entities. The TOE provides that ability to identify the VLANthe network traffic is associated with. The TOE then permits or denies the network trafficbased on the VLANs configured on the interface the network traffic is received /destined.1.6.4 CryptographyThe TOE provides cryptography in support of other Cisco 800, 1900, 2900, 3900 SeriesIntegrated Service Routers (ISR) security functionality. This cryptography has beenvalidated for conformance to the requirements of FIPS 140-2 Level 2. The TOE providescryptography in support of VPN connections and remote administrative management viaSSHv2. The cryptographic services provided by the TOE include,Table 7: TOE Provided CryptographyCryptographic MethodInternet Key ExchangeGroup Domain of InterpretationANSI X9.31 PRNG (3 key TDES-based)AESUse within the TOEUsed to establish initial IPSec session.Used in IPSec session establishment.Used in IPSec session establishment.Used to encrypt IPSec session traffic.Used to encrypt SSHv2 session traffic.1.6.5 Secure AuditingThe Cisco 800, 1900, 2900, 3900 Series Integrated Service Routers (ISR) provideextensive auditing capabilities. The TOE can audit events related to cryptographicfunctionality, information flow control enforcement, identification and authentication,and administrative actions. The Cisco 800, 1900, 2900, 3900 Series Integrated ServiceRouters (ISR) generate an audit record for each auditable event. The Cisco 800, 1900,2900, 3900 Series Integrated Service Routers (ISR) provide the administrator with asorting and searching capability to improve audit analysis. The administrator configuresauditable events, backs-up and manages audit data storage. The TOE provides theadministrator with a circular audit trail or a configurable audit trail threshold to track thestorage capacity of the audit trail.1.7 TOE Evaluated ConfigurationThe following figure provides a visual depiction of an example TOE deployment. TheTOE boundary is surrounded with a hashed red line.12
Cisco ISR STAugust 2011P WR0KPW R0KS LO T 0 SLOT 1 SLOT 2000111S LOT 0 S LOT 1 S LOT 2000111Cisco1700E THA CTS E R IE SRO UTERCOLCisco1700ET HACTS E R IE SRO UTERCO LThe previous figure includes the following: Several examples of TOE Modelso Cisco 881 ISRo Cisco 1941 ISRo Cisco 2951 ISRo Cisco 3945 ISR IT Environment: (2) VPN Peers IT Environment: Management Workstation IT Environment: AAA Server IT Environment: NTP Server1.7.1 Excluded FunctionalityThe following functional is excluded from the evaluation.Table 8: Excluded FunctionalityExcluded FunctionalityNon-FIPS 140-2 mode of operation on theStream Control Transmission Protocol (SCTP)Exclusion RationaleThis mode of operation includes non-FIPS allowedoperations.This feature was not tested during the evaluationand therefore is excluded from the evaluatedconfiguration.These services will be disabled by configuration. The exclusion of this functionality doesnot affect compliance to the U.S. Government Protection Profile for Traffic FilterFirewall in Basic Robustness Environments.13
Cisco ISR ST2August 2011CONFORMANCE CLAIMS2.1 Common Criteria Conformance ClaimThe TOE and ST are compliant with the Common Criteria (CC) Version 3.1, Revision 3,dated: September 2009.The TOE and ST are EAL4 Augmented with ALC FLR.2 Part 3 conformant.The TOE and ST are CC Part 2 extended2.2 Protection Profile ConformanceThis ST claims compliance to the following Common Criteria validated Protection Profiles:Table 9: Protection ProfilesProtection ProfileU.S. Government Protection Profile for Traffic Filter Firewall in BasicRobustness Environments (pp fw tf br v1.1)VersionDate1.1July 25, 20072.2.1 Protection Profile RefinementsThe following table identifies the refinements made to the Protection Profile and providesrationale for the refinement:Table 10: Protection Profile RefinementsRefinementChange the Assurance Claim from EAL 2augmented with ALC FLR.2 to EAL 4Augmented with ALC FLR.2.FMT SMR.1FIA ATD.1RationaleThis refinement increases the Assurance of the evaluation. All ofthe assurance provided by EAL2 augmented is included withEAL4 augmented.Refined to also address External IT entitiesRefined to also address External IT entities2.2.2 Protection Profile AdditionsThe foll
Cisco 2951 ISR, Cisco 3925 ISR, Cisco 3925E ISR, Cisco 3945 ISR, and Cisco 3945E ISR, running Cisco IOS Release 15.1.2.T3. 1.5 Physical Scope of the TOE The TOE is a hardware and software solution that makes up the following router models Cisco 881 ISR, Cisco 881G ISR, Cisco 891 ISR, Cisco 1905 ISR, Cisco 1921 ISR, Cisco
In addition to the Cisco 1900 series, Cisco 2900 series, and Cisco 3900 series ISR Software Configuration Guide (this document), the following reference guides are included: Type of Document Links Hardware † Read Me First for the Cisco 1900 Series, 2900 Series, and 3900 Series Integrated Services Routers.
configuration of the router using the Cisco IOS CLI, and additional configuration procedures for the router. v Cisco 3900 Series, 2900 Series, and 1900 Series Integrated Services Routers Software Configuration Guide OL-21850-01 Preface Conventions This document uses the following conventions:
Cisco 1861 and Cisco 2800, 3800, 2900, 3900, and 3900E Series unified communications routers. SRST software automatically detects a connectivity failure between Cisco Unified Communications Manager and IP phones at the branch office. Using the Cisco Simple
Supported Devices - Cisco SiSi NetFlow supported Cisco devices Cisco Catalyst 3560 Cisco 800 Cisco 7200 Cisco Catalyst 3750 Cisco 1800 Cisco 7600 Cisco Catalyst 4500 Cisco 1900 Cisco 12000 Cisco Catalyst 6500 Cisco 2800 Cisco ASR se
Cisco ASA 5505 Cisco ASA 5505SP Cisco ASA 5510 Cisco ASA 5510SP Cisco ASA 5520 Cisco ASA 5520 VPN Cisco ASA 5540 Cisco ASA 5540 VPN Premium Cisco ASA 5540 VPN Cisco ASA 5550 Cisco ASA 5580-20 Cisco ASA 5580-40 Cisco ASA 5585-X Cisco ASA w/ AIP-SSM Cisco ASA w/ CSC-SSM Cisco C7600 Ser
The following Cisco IOS software releases support software activation on Cisco ISRs: † Cisco 3900 series, 2900 series, and 1900 series ISRs running Cisco IOS Release 15.0(1)M. – Cisco 3925E and Cisco 3945E ISR running Cisco IOS Release 15.1(1)T. † Right to Use license is supported on Cisco IOS Release 15.0(1)M4, 15.1(1)T2, 15.1(2)T2, 15.1 .
VWIC3-2MFT-G703 Cisco Voice/WAN Card VWIC3-2MFT-G703 Licenses L-SL-19-DATA-K9 Cisco 1900 IOS License L-SL-19-DATA-K9 Data E-Delivery PAK for Cisco 1900 L-SL-19-SEC-K9 Security License for Cisco 1900 L-SL-19-APP-K9 AppX License with; DATA and WAAS for Cisco 1900 Series Get more information Do you have any question about the Cisco 1921/K9
Am I my Brother’s Keeper? Sibling Spillover E ects: The Case of Developmental Disabilities and Externalizing Behavior Jason Fletcher, Nicole Hair, and Barbara Wolfe July 27, 2012 Abstract Using a sample of sibling pairs from the PSID-CDS, we examine the e ects of sibling health status on early educational outcomes. We nd that sibling developmental dis- ability and externalizing behavior are .