Transport Lavel Security
Transport LevelSecurityRaj JainWashington University in Saint LouisSaint Louis, MO 63130Jain@cse.wustl.eduAudio/Video recordings of this lecture are available at:http://www.cse.wustl.edu/ jain/cse571-17/Washington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-1 2017 Raj Jain
Overview1.2.3.4.Secure Sockets Layer (SSL)Transport Layer Security (TLS)HTTPSSecure Shell (SSH)These slides are based partly on Lawrie Brown’s slides supplied with William Stallings’sbook “Cryptography and Network Security: Principles and Practice,” 7th Ed, 2017.Washington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-2 2017 Raj Jain
Web Traffic Security Approaches SSL/TLS provides the following services over TCP layer:1. Crypto negotiation: Negotiate encryption and hashmethods2. Key Exchange: Secret key exchange using public keycertificates3. Privacy: Encryption using a secret key4. Integrity: Message authentication using a keyed hashWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-3 2017 Raj Jain
History SSL was developed by Netscape. V1 was never deployed. V2had major issues.SSL v3 is most commonly deployed protocolIETF standardized SSL V3 with some upgrades as TransportLayer Security (TLS) V1 in RFC 2246 1999TLS is encoded as SSL V3.1The differences are small but the protocols do not interoperate.TLS v1.1 (SSL V3.2) added protection against CBC attacks[RFC 4346 2006]Ref: http://en.wikipedia.org/wiki/Transport Layer SecurityWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-4 2017 Raj Jain
History (Cont) TLS v1.2 (SSL V3.3) in RFC 5246 August 2008 added: MD5-SHA-1 pseudorandom function (PRF) replaced withSHA-256 MD5-SHA-1 Finished message hash replaced with SHA256 MD5-SHA-1 in digitally-signed element replaced with asingle hash negotiated during handshake, default SHA-1. Enhanced Client's and server's specification for hash andsignature algorithms Expansion of support for authenticated encryption ciphers TLS Extensions definition and Advanced EncryptionStandard Cipher SuitesRFC 6176 updated TLS v1.2 by requiring that SSL V2 is neveraccepted.Ref: http://en.wikipedia.org/wiki/Transport Layer Security#TLS 1.3 .28draft.29http://www.cse.wustl.edu/ jain/cse571-17/Washington University in St. Louis17-5Must Read 2017 Raj Jain
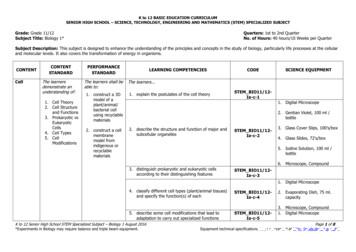
SSL Architecture 1.2.3.4.SSL has 4 components in two layersHandshake protocol: Negotiates crypto parameters for an“SSL session” that can be used for many “SSL/TCPconnections”Record Protocol: Provides encryption and MACAlert protocol: To convey problemsChange Cipher Spec Protocol: Implement negotiated cryptoparametersWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-6 2017 Raj Jain
SSL Handshake Protocol Allows server and client to: Authenticate each other To negotiate encryption & MAC algorithms To negotiate cryptographic keys to be usedComprises a series of messages in phases1.Establish Security Capabilities2.Server Authentication3.Client Authentication and Key Exchange4.FinishWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-7 2017 Raj Jain
SSL Handshake Protocol ActionsClientServerClient Hello: Crypto Choices (Protocol Version, Cipher Suite, Compression, RClientServer Hello: Crypto Selected, RServerCertificate: Server Certificate (Optional)Server Key Exchange (Optional)Certificate Request (Optional)Server Hello DoneGeneraterandomPMS SCertificate: Client CertificateClient Key Exchange: E(Kserver Public Key, PreMasterSecret)ComputeMS KComputeMS KCertificate VerifyChange Cipher SpecHandshake Finished: Hash and MAC of Previous messagesChange Cipher SpecHandshake FinishedWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-8 2017 Raj Jain
Handshake MessagesAll messages are Type-Length-Value (TLV) encoded.Types1 Client Hello: Highest Version Supported, RClient, Session ID, Cipher Suites,Compressions2 Server Hello: Version Accepted, RServer, Session ID, Chosen Cipher,Chosen Compression14 Server Hello Done16 Client Key Exchange: Encrypted pre-master key12 Server Key Exchange: Modulus p, Exponent g, Signature (export only)13 Certificate Request: CA Names (requested by the server)11 Certificate: sent by the server15 Certificate Verify: Signature of Hash of messages20 Handshake Finished: MD5 and SHA Digest of message halvesWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-9 2017 Raj Jain
Security Capability Negotiation Key-Exchange Methods: RSA Fixed D-H: Shared secret generated using fixed public keys Ephemeral D-H: Ephemeral Temporary, one-time secret key isgenerated after certificate exchange and authentication Anonymous D-H: No authentication. Only public key exchange.Subject to MITM attack Fortezza: Using PC-Cards (http://en.wikipedia.org/wiki/Fortezza)CipherSpec: Cipher Algorithm: RC4, RC2, DES, 3DES, DES40, IDEA, or Fortezza MAC Algorithm: MD5 or SHA-1 CipherType: Stream or Block IsExportable: True or False HashSize: 0, 16 (for MD5), or 20 (for SHA-1) bytes Key Material: info used to generate keys IV Size: Size of IV for CBCRef: http://en.wikipedia.org/wiki/Cipher suiteWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-10 2017 Raj Jain
Cryptographic Computations Master secret creation A one-time 48-byte value based on nonces A 48-byte pre-master secret is exchanged/generated usingsecure key exchange (RSA / Diffie-Hellman) and thenhashing: Master Secret MD5(Pre master Secret SHA(‘A’ pre master secret clientHello.random ServerHello.random)) MD5(Pre master Secret SHA(‘BBB’ pre master secret clientHello.random ServerHello.random)) MD5(Pre master Secret SHA(‘CCC’ pre master secret clientHello.random ServerHello.random))Generation of cryptographic parameters Client write MAC secret, a server write MAC secret, aclient write key, a server write key, a client write IV, and aserver write IV Generated by hashing master secretWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-11 2017 Raj Jain
SSL Change Cipher Spec Protocol A single 1-byte messageCauses negotiated parameters to become currentHence updating the cipher suite in useWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-12 2017 Raj Jain
SSL Alert ProtocolConveys SSL-related alerts to peer entityTwo byte message: Level-Alert, level warning or fatal,fatal Immediate termination0 Close notify (warning or fatal)10Unexpected message (fatal)20Bad record MAC (fatal)21Decryption failed (fatal, TLS only)22Record overflow (fatal, TLS only)41No certificate (SSL v3 only) (warning or fatal)42Bad certificate (warning or fatal)43Unsupported certificate (warning or fatal)44Certificate revoked (warning or fatal)45Certificate expired (warning or fatal) .Washington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-13 2017 Raj Jain
SSL Record Protocol Services Confidentiality Using symmetric encryption with a shared secret keydefined by Handshake Protocol AES, IDEA, RC2-40, DES-40, DES, 3DES, Fortezza, RC440, RC4-128 The message is compressed before encryptionMessage integrity Using a MAC with shared secret key Similar to HMAC but with different paddingWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-14 2017 Raj Jain
SSL Record Protocol OperationWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-15 2017 Raj Jain
Encoding All exchanges are in records up to 214B or 216-1B.The standard allows multiple messages in one record ormultiple records.Most implementations use one message per record.Four Record Types: 20 Change Cipher Spec 21 Alerts (1 Warning, 2 Fatal) 22 Handshake 23 Application DataRecord header:Record Type Version # Rec Length1B2B2BEach message starts with a 1B message-type and 3B messagelength.Msg Type Msg Len MsgWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-16 2017 Raj Jain
TLS (Transport Layer Security) IETF standard RFC 2246 similar to SSLv3With minor differences In record format version number Uses HMAC for MAC A pseudo-random function expands secrets Based on HMAC using SHA-1 or MD5 Has additional alert codes Some changes in supported ciphers Changes in certificate types & negotiations Changes in crypto computations & paddingWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-17 2017 Raj Jain
HTTPS HTTPS (HTTP over SSL) Combination of HTTP & SSL/TLS to securecommunications between browser & server Documented in RFC2818 No fundamental change using either SSL or TLSUse https:// URL rather than http:// And port 443 rather than 80Encrypts URL, document contents, form data, cookies, HTTPheadersRef: http://en.wikipedia.org/wiki/HTTP SecureWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-18 2017 Raj Jain
HTTPS Use Connection initiation TLS handshake then HTTP request(s)Connection closure Have “Connection: close” in HTTP record TLS level exchange close notify alerts Can then close the TCP connection Must handle abnormal TCP close before alert exchange sentor completedWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-19 2017 Raj Jain
Secure Shell (SSH) Secure remote loginSSH1 provided secure remote logon facility Replace TELNET & other insecure schemes Also has more general client/server capabilitySSH2 fixes a number of security flawsDocumented in RFCs 4250 through 4254SSH clients & servers are widely availableRef: http://en.wikipedia.org/wiki/Secure ShellWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-20 2017 Raj Jain
SSH Protocol Layers IP: Routes messages to destinationTCP: end-to-end reliable deliverySSH Transport Layer Protocol: Server authentication, confidentiality, integrity May optionally provide compressionSSH User Authentication Protocol: Authenticates clientSSH Connection Protocol: Provided multiple logical channels2. SSH User Authentication Protocol 3. SSH Connection Protocol1. SSH Transport Layer ProtocolTCPIPWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-21 2017 Raj Jain
SSH Transport Layer Server Authentication,Privacy and IntegrityThe client must know theserver's public key inadvancePadding LengthPacket LengthRef: RFC 4253Washington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-22 2017 Raj Jain
SSH User Authentication Layer Authenticates client to serverThree message types: SSH MSG USERAUTH REQUEST SSH MSG USERAUTH FAILURE SSH MSG USERAUTH SUCCESSAuthentication methods used: Public-key, password, host-basedClientServerSSH MSG USERAUTH REQUESTMethod NoneSSH MSG USERAUTH FAILUREAccept public key, passwordSSH MSG USERAUTH REQUESTMethod Password, my passwordSSH MSG USERAUTH SUCCESSRef: RFC 4252Washington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-23 2017 Raj Jain
SSH Connection Layer Runs on SSH Transport Layer ProtocolAssumes secure authenticationconnectionUsed for multiple logical channels SSH communications use separatechannels Either side can open with unique idnumber Flow controlled Have three stages: Opening a channel, datatransfer, closing a channel Four types: Session, x11, forwarded-tcpip(remote port forwarding),direct-tcpip (local portforwarding).Ref: RFC 4254Washington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-24 2017 Raj Jain
Port ForwardingApplicationApplicationFirewallHost SHost HHost WSSHSSHx aTCPbc dTCPApplicationApplicationFirewallHost SHost H Host WSSHSSHyTCPxaTCPbc dTCPyTCP(a) Local Forwarding(a) Remote Forwardingssh –La:S:y Wssh –Ra:S:y HPort forwarding or tunneling allows insecure applications to run over secure SSH.SSH tells location application to connect to H:a rather than S:y. SSH listens to H:a,encrypts the traffic and sends to other side where SSH sends to S:y.Note: All TCP connections are bidirectional. Arrows show the TCP connectmessage direction. If application server is on W, “localhost” is used in place of S.Local forwarding: Client SSH (Host H) starts the tunnel, informs the server SSH(Host W): “Please forward the traffic on this channel to S:y”Remote Forwarding: Client SSH (Host W) starts the tunnel, informs the server SSH(Host H): “I will forward the traffic on this channel to S:y”Ref: http://docstore.mik.ua/orelly/networking 2ndEd/ssh/ch09 02.htmWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-25 2017 Raj Jain
Summary1.2.3.4.5.SSL provides security at transport layer. TLS is astandardization of SSL V3.SSL consists of 4 protocols: Handshake (Crypto Negotiation),Change Cipher, Alert, and Record (Encryption and MAC)HTTPS is simply http over SSL.SSH provides secure remote login and consists of 3 protocols:User authentication, Connection (Channels), Transport layer(Encryption, MAC, Server authentication)SSH port forwarding (tunneling) allows insecure applicationsto run in a secure mode.Washington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-26 2017 Raj Jain
Homework 17Consider the following threats to Web security and describe howeach is encountered by a particular feature of SSL.A. Brute-Force Cryptanalytic Attack: An exhaustive search ofthe key space for a conventional encryption algorithmB. Know Plaintext Dictionary Attack: Many messages willcontain predictable plain text, such as the HTTP GETcommand. An attacker constructs a dictionary containing everypossible encryption of the known-plaintext message. When anencrypted message is intercepted, the attacker takes the portioncontaining the encrypted known plaintext and looks up theciphertext in the dictionary. The ciphertext should matchagainst an entry that was encrypted wit the same secret key. Ifthere are several matches, each of these can be tried against thefull ciphertext to determine the right one. This attack isespecially effective against small key sizes (e.g., 40-bite keys).Washington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-27 2017 Raj Jain
Homework 17 (Cont)C. Replay Attack: Earlier SSL handshake messages are replayed.D. Man in the middle Attack: An attacker interposes during keyexchange, active as the client to the server and as the server tothe client.E. Password Sniffing: Passwords in HTTP or other applicationtraffic are eaves dropped.F. IP Spoofing: Uses forced IP addresses to fool a host intoaccepting bogus data.G. IP Hijacking: An active, authenticated connection betweentwo hosts is disrupted and the attacker takes the place of one ofthe hosts.H. SYN Flooding: An attacker sends TCP SYN messages torequest a connection but does not respond to the final messageto establish the connection fully. The attacked TCP moduletypically leaves the “half-open connection” around for a fewminutes. Repeated SYN messages can clog the TCP module.Washington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-28 2017 Raj Jain
Lab 17: SSL Message ExchangeIn this lab, you will capture an SSL exchange and analyzevarious messages. Open Wireshark and start monitoring with appropriate filters Browse to https://google.com Analyze the captured trace and answer the following questions.Submit screenshots that support your answers. Also, specifythe web browser used and its version.1. What version of TLS is used?2. What number identifies the SSL Handshake content type?3. What number identifies the SSL Application Data contenttype? Ref: Adapted from N. Saxena, sec-f13/labs/HW3.pdfhttp://www.cse.wustl.edu/ jain/cse571-17/Washington University in St. Louis17-29 2017 Raj Jain
Lab 17: SSL Message Exchange (Cont)4. What number identifies the SSL Change Cipher Spec contenttype?5. In your Wireshark trace, what sets of messages are bundledtogether into single frames6. What is ClientRandomValue included in the Client Hellomessage?7. What are the first 5 cipher suites, suggested by the clientmachine8. What is the cipher suite selected by the server?9. Establish another secure session with google, do you get thesame answer? Which answers changed?Washington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-30 2017 Raj Jain
Acronyms MD5Triple-DESAdvanced Encryption AlgorithmCertificate AuthorityCipher Block ChainingData Encryption StandardHybrid Message Authentication CodeHypertext Transfer ProtocolHypertext Transfer Protocol SecureIdentifierInternational Data Encryption AlgorithmInternet Engineering Task ForceInternet ProtocolSecure IPInitialization ValueMessage Authentication CodeMessage Digest 5Washington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-31 2017 Raj Jain
Acronyms (Cont) an-in-the-MiddleMaster SecretMessageMaster Secret KeyPersonal ComputerPre-Master SecretPostoffice ProtocolPseudorandom functionRon's Code 2Ron's Code 4Request for CommentRivest, Shamir, and AdlemanSecure Hash Algorithm 1Secure Hash AlgorithmSecure ShellSecure Socket LayerWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-32 2017 Raj Jain
Acronyms (Cont) SSLv3SYNTCPTLSTLVURLSecure Socket Layer Version 3SynchronizationTransmission Control ProtocolTransport Layer SecurityType-Length-ValueUniform Resource LocatorWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-33 2017 Raj Jain
Scan This to Download These SlidesRaj Jainhttp://rajjain.comWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-34 2017 Raj Jain
Related ModulesCSE571S: Network Security (Spring 2017),http://www.cse.wustl.edu/ jain/cse571-17/index.htmlCSE473S: Introduction to Computer Networks (Fall 2016),http://www.cse.wustl.edu/ jain/cse473-16/index.htmlWireless and Mobile Networking (Spring 2016),http://www.cse.wustl.edu/ jain/cse574-16/index.htmlCSE571S: Network Security (Fall 2014),http://www.cse.wustl.edu/ jain/cse571-14/index.htmlAudio/Video Recordings and Podcasts ofProfessor Raj Jain's P9-ruOzQMs-8NUwWashington University in St. Louishttp://www.cse.wustl.edu/ jain/cse571-17/17-35 2017 Raj Jain
MD5(Pre_master_Secret SHA(‘CCC’ pre_master_secret clientHello.random ServerHello.random)) Generation of cryptographic parameters Client write MAC secret, a server write MAC secret, a client write key, a server write key, a client write IV, and a server write IV Generated by hashing master secret
Transport Management System of Nepal Nepalese transport management is affected by existing topographical condition of the country. Due to this only means of transport used in the country are road transport and air transport. In this paper only road transport is discussed. During the Tenth Plan period, the vehicle transport management
A. Core Transport Management System Forms 149 B. Ghana Transport Policy 173. C. Resources for TMS Stakeholders 183. D. Transport Assessment Tool 185. Figures . 1. A Typical National Transport Management Human Resource Structure 2 . 2. A Typical Health Facility or Provincial/District Office Transport Management Structure 2 . 3. Completed Period .
3. LCA of rail freight transport 4. LCA of IWW transport 5. LCA of road freight transport 6. Comparison of the environmental impacts of the transport modes III. Environmental impact assessment of freight transport 7. Study of intermodal freight transport routes 8. Study of the modal split of inland freight transport in Belgium IV. Conclusions .
Sand transport is herein defined as the transport of particles with sizes in the range of 0.05 to 2 mm as found in the bed of rivers, estuaries and coastal waters. The two main modes of sand transport are bed-load transport and suspended load transport. The bed-load transport is defined to consist of gliding, rolling and saltating particles in
et sur les infrastructures de transport 25 - Transport et activité économique 55 - Entreprises françaises de transport 89 - Emploi et salaires 97 - Les externalités du transport 117 - Le transport de marchandises 129 - Le transport de voyageurs 141 - Bilan de la circulation 149 - Annexes
Transport c. Active Transport d. Bulk/Vesic ular Transport 2. relate the structure and composition of the cell membrane to its function STEM_BIO11/12-Ig-h-12 3. explain transport mechanisms in cells (diffusion osmosis, facilitated transport, active transport) STEM_BIO11
Types of Transport There are 3 types of transport in cells: 1. Passive Transport: does not use the cell’s energy in bringing materials in & out of the cell 2. Active Transport: does use the cell’s energy in bringing materials in & out of the cell 3. Bulk Transport: involves the cell making me
While opening an AutoCAD 2000 drawing, you can use the Partial Open option to work with only part of the drawing file. If you are working with a large drawing, you can partially open the drawing and select a specific view and layers to work with instead of loading the entire drawing. See “Using Par- tial Open and Partial Load” on page 311. To open a drawing 1 In the Startup dialog box .