MikroTik RouterOS Training Class
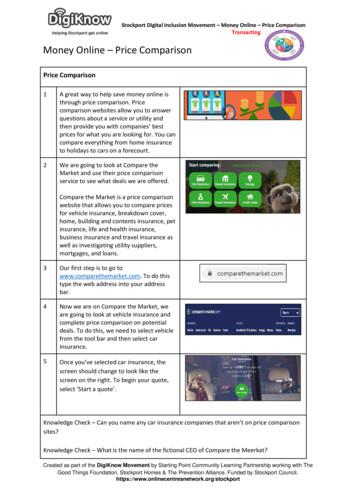
MikroTik RouterOSTraining ClassMTCNA Townet Wispmax 3 Febbraio 2010
Schedule Training day: 9AM - 6PM30 minute Breaks: 10:30AM and 4PM1 hour Lunch: 01:00PM2
Course Objective Overview of RouterOS software andRouterBoard capabilities Hands-on training for MikroTik routerconfiguration, maintenance and basictroubleshooting3
About MikroTik Router software and hardware manufacturer Products used by ISPs, companies andindividuals Make Internet technologies faster, powerfuland affordable to wider range of users4
MikroTik's History 1995: Established 1997: RouterOS software for x86 (PC) 2002: RouterBOARD is born 2006: First MUM5
Where is MikroTik? www.mikrotik.com www.routerboard.com Riga, Latvia, Northern Europe,EU6
Where is MikroTik ?7
IntroduceYourself Please, introduce yourself to the class Your nameYour CompanyYour previous knowledge about RouterOS(?)Your previous knowledge about networking(?)What do you expect from this course? (?)Please, remember your class XY number.8
MikroTik RouterOS9
What is RouterOS ? RouterOS is an operating system that willmake your device: a dedicated router a bandwidth shaper a (transparent) packet filter any 802.11a,b/g wireless device10
What is RouterOS ? The operating system of RouterBOARD Can be also installed on a PC11
What is RouterBOARD ? Hardware created by MikroTik Range from small home routers tocarrier-class access concentrators12
First Time AccessNull ModemCableEthernetcable13
Winbox The application for configuring RouterOS It can be downloaded fromwww.mikrotik.com14
Download Winbox15
ConnectingClick on the [.] button to see your router16
Communication Process of communication is divided intoseven layers Lowest is physical layer, highest isapplication layer17
18
MAC address It is the unique physical address of anetwork device It’s used for communication within LAN Example: 00:0C:42:20:97:6819
IP It is logical address of network device It is used for communication overnetworks Example: 159.148.60.2020
Subnets Range of logical IP addresses thatdivides network into segments Example: 255.255.255.0 or /2421
Subnets Network address is the first IP address ofthe subnet Broadcast address is the last IP addressof the subnet They are reserved and cannot be used22
23
Selecting IP address Select IP address from the same subneton local networks Especially for big network with multiplesubnets24
Selecting IP addressExample Clients use different subnet masks /25 and /26 A has 192.168.0.200/26 IP address B use subnet mask /25, available addresses192.168.0.129-192.168.0.254 B should not use 192.168.0.129-192.168.0.192 B should use IP address from 192.168.0.193 192.168.0.254/2525
ConnectingEthernetCableWinbox26
Connecting Lab Click on the Mac-Address in Winbox Default username “admin” and nopassword27
DiagramClass APYour LaptopYour Router28
Laptop - Router Disable any other interfaces (wireless) inyour laptop Set 192.168.X.1 as IP address Set 255.255.255.0 as Subnet Mask Set 192.168.X.254 as Default Gateway29
Laptop - Router Connect to router with MAC-Winbox Add 192.168.X.254/24 to Ether130
Laptop - Router Close Winbox and connect again usingIP address MAC-address should only be used whenthere is no IP access31
Laptop RouterDiagramClass APYour Laptop Your Router192.168.X. 192.168.X.251432
Router InternetClass APYour Laptop Your Router192.168.X. 192.168.X.251433
Router - Internet The Internet gateway of your class isaccessible over wireless - it is an AP(access point) To connect you have to configure thewireless interface of your router as astation34
Router - InternetTo configurewirelessinterface,double-clickon it’s name35
Router - Internet To see available AP use scan button Select class1 and click on connect Close the scan window You are now connected to AP! Remember class SSID class136
Router - Internet The wireless interface also needs an IPaddress The AP provides automatic IP addressesover DHCP You need to enable DHCP client on yourrouter to get an IP address37
Router - Internet38
Router - InternetCheck Internetconnectivity bytraceroute39
Router InternetClass APYour Laptop Your RouterDHCP-ClientWireless40
Laptop - InternetYour router too can be a DNS server for yourlocal network (laptop)41
Laptop - Internet Tell your Laptop to use your router asthe DNS server Enter your router IP (192.168.x.254) asthe DNS server in laptop networksettings42
Laptop - Internet Laptop can access the router and therouter can access the internet, one morestep is required Make a Masquerade rule to hide yourprivate network behind the router, makeInternet work in your laptop43
Private and Publicspace Masquerade is used for Public network access,where private addresses are present Private networks include 10.0.0.0-10.255.255.255,172.16.0.0-172.31.255.255, 192.168.0.0192.168.255.25544
Laptop - Internet45
Check ConnectivityPing www.mikrotik.com from your laptop46
What Can Be Wrong Router cannot ping further than AP Router cannot resolve names Computer cannot ping further than router Computer cannot resolve names Is masquerade rule working Does the laptop use the router as defaultgateway and DNS47
Network DiagramYour LaptopClass APYour Router192.168.X. 192.168.X.2514DHCP-Client48
User Management Access to the router can be controlled You can create different types of users49
User ManagementLab Add new router user with full access Make sure you remember user name Make admin user as read-only Login with your new user50
Upgrading Router Lab Download packages fromftp://192.168.200.254 Upload them to router with Winbox Reboot the router Newest packages are always available onwww.mikrotik.com51
Upgrading Router UsecombinedRouterOSpackage Drag it to theFiles window52
Package ManagementRouterOSfunctionsare enabledby packages53
Package Information54
Package Lab Disable wireless Reboot Check interface list Enable wireless55
Router IdentityOption to set name for each router56
Router IdentityIdentity information is shown in different places57
Router Identity LabSet your number your name as router identity58
NTP Network Time Protocol, to synchronizetime NTP Client and NTP Server support inRouterOS59
Why NTP To get correct clock on router For routers without internal memory tosave clock information For all RouterBOARDs60
NTP ClientNTP package is not required61
Configuration Backup You can backup and restoreconfiguration in the Files menu ofWinbox Backup file is not editable62
Configuration Backup Additionally use export and importcommands in CLI Export files are editable Passwords are not saved with export/export file conf-august-2009/ ip firewall filter export file firewall-aug-2009/ file print/ import [Tab]63
Backup Lab Create Backup and Export files Download them to your laptop Open export file with text editor64
Netinstall Used for installing and reinstallingRouterOS Runs on Windows computers Direct network connection to router isrequired or over switched LAN Available at www.mikrotik.com65
Netinstall1.List of routers2.Net Booting3.Keep oldconfiguration4.Packages5.Install66
Optional Lab Download Netinstall from ftp://192.168.100.254 Run Netinstall Enable Net booting, set address 192.168.x.13 Use null modem cable and Putty to connect Set router to boot from Ethernet67
RouterOS License All RouterBOARDs shipped with license Several levels available, no upgrades Can be viewed in system license menu License for PC can be purchased frommikrotik.com or from distributors68
License69
Obtain LicenseLogin toyour account70
Update License for802.11N 8-symbolsoftware-IDsystemisintroduced Update key on existing routers to get fullfeatures support (802.11N, etc.)71
Summary72
Useful Links www.mikrotik.com - manage licenses,documentation forum.mikrotik.com - share experiencewith other users wiki.mikrotik.com - tons of examples73
Firewall74
Firewall Protects your router and clients fromunauthorized access This can be done by creating rules inFirewall Filter and NAT facilities75
Firewall Filter Consists of user defined rules that workon the IF-Then principle These rules are ordered in Chains There are predefined Chains, and Usercreated Chains76
Filter Chains Rules can be placed in three defaultchains input (to router) output (from router) forward (trough the router)77
Firewall ChainsOutputPing from RouterInputWinboxForwardWWW E-Mail78
Firewall Chains79
Input Chain contains filter rules that protect therouter itself Let’s block everyone except your laptop80
InputAdd an acceptrule for yourLaptop IPaddress81
InputAdd a drop rulein input chainto dropeveryone else82
Input Lab Change your laptop IP address,192.168.x.y Try to connect. The firewall is working You can still connect with MAC-address,Firewall Filter is only for IP83
Input Access to your router is blocked Internet is not working Because we are blocking DNS requests aswell Change configuration to make Internetworking84
You canInputdisable MACaccess in theMAC Servermenu Change theLaptop IPaddress backto 192.168.X.1,and connectwith IP85
Address-List Address-list allows you to filter group ofthe addresses with one rule Automatically add addresses byaddress-list and then block86
Address-List Create different lists Subnets, separates ranges, one hostaddresses are supported87
Address-List Add specifichost toaddress-list Specify timeoutfor temporaryservice88
Address-List inFirewall Ability to blockby source anddestinationaddresses89
Address-List Lab Create address-list with allowed IPaddresses Add accept rule for the allowed addresses90
Forward Chain contains rules that control packetsgoing trough the router Control traffic to and from the clients91
Forward Create a rulethat will blockTCP port 80(web browsing) Must selectprotocol toblock ports92
Forward Try to open www.mikrotik.com Try to open http://192.168.X.254 Router web page works because droprule is for chain forward traffic93
List of well-knownports94
ForwardCreate a rule that willblock client’s p2ptraffic95
Firewall Log Let’s log clientpings to the router Log rule shouldbe added beforeother action96
Firewall Log97
Firewall chains Except of the built-in chains (input,forward, output), custom chains can becreated Make firewall structure more simple Decrease load of the router98
Firewall chains in Action Sequence ofthe firewallcustomchains Customchains canbe forviruses,TCP, UDPprotocols,etc.99
Firewall chain Lab Download viruses.rsc from router(access by FTP) Export the configuration by importcommand Check the firewall10
Connections10
Connection State Advise, drop invalid connections Firewall should proceed only newpackets, it is recommended to excludeother types of states Filter rules have the “connection state”matcher for this purpose10
Connection State Add rule to drop invalid packets Add rule to accept established packets Add rule to accept related packets Let Firewall to work with new packets only10
Summary10
Network AddressTranslation10
NAT Router is able to change Source orDestination address of packets flowingtrough it This process is called src-nat or dst-nat10
SRC-NATNewSRC-AddressSRC-AddressYour LaptopRemote Server10
DST-NATPrivate NetworkServerPublic HostNew DST-AddressDST-Address10
NAT Chains To achieve these scenarios you have toorder your NAT rules in appropriatechains: dstnat or srcnat NAT rules work on IF-THEN principle10
DST-NAT DST-NAT changes packet’s destinationaddress and port It can be used to direct internet users toa server in your private network11
DST-NAT ExampleWeb Server192.168.1.1Some ComputerNew 8011
DST-NAT ExampleCreate a rule to forward traffic to WEB server inprivate network11
Redirect Special type of DST-NAT This action redirects packets to the routeritself It can be used for proxying services(DNS, HTTP)11
Redirect exampleDST-AddressConfigured DNS Server:53New DST-AddressRouter:53DNS Cache11
Redirect Example Let’s make localusers to useRouter DNScache Also make rulefor udp protocol11
SRC-NAT SRC-NAT changes packet’s sourceaddress You can use it to connect private networkto the Internet through public IP address Masquerade is one type of SRC-NAT11
MasqueradeSrc Address192.168.X.1Src Addressrouter address192.168.X.1Public Server11
SRC-NAT Limitations Connecting to internal servers fromoutside is not possible (DST-NATneeded) Some protocols require NAT helpers towork correctly11
NAT Helpers11
Firewall Tips Add comments to your rules Use Connection Tracking or Torch12
Connection Tracking Connection tracking managesinformation about all active connections. It should be enabled for Filter and NAT12
Connection Tracking12
TorchDetailed actual traffic report for interface12
Firewall Actions Accept Drop Reject Tarpit log add-src-to-addresslist(dst) Jump, Return Passthrough12
NAT Actions Accept DST-NAT/SRC-NAT Redirect Masquerade Netmap12
Summary12
Bandwidth Limit12
Simple Queue The easiest way to limit bandwidth: client download client upload client aggregate, download upload12
Simple Queue You must use Target-Address forSimple Queue Rule order is important for queue rules12
Simple Queue Let’screatelimitationfor yourlaptop 64kUpload,128kDownloadClient’sLimitsaddressto configure13
Simple Queue Check your limits Torch is showing bandwidth rate13
Using Torch Select localnetworkinterface See actualbandwidthSetCheckLaptoptheSet InterfaceAddressResults13
Specific Server Limit Let’s createbandwidthlimit toMikroTik.com DST-addressis used forthis Rules orderis important13
Specific Server Limit Pingwww.mikrotik.com Put MikroTikaddress to DSTaddressMikroTik.comAddress MikroTik addresscan be used asTarget-addresstoo13
Specific Server Limit DST-address is useful to setunlimited access to the localnetwork resources Target-address and DSTaddresses can be vice versa13
Bandwidth Test Utility Bandwidth test can be used to monitorthroughput to remote device Bandwidth test works between twoMikroTik routers Bandwidth test utility available forWindows Bandwidth test is available onMikroTik.com13
Bandwidth Test onRouter Set Test To as testing address Select protocol TCP supports multipleconnections Authentication might berequired13
Bandwidth Server Set Test To as testing address Select protocol TCP supports multipleconnections Authentication might berequired13
Bandwidth Test Server should be enabled It is advised to use enabledAuthenticate13
Traffic Priority Let’s configurehigher priorityfor queues Priority 1 ishigher than 8 There should beat least twopriorityPriorityis inSelectQueueAdvanced TabSet Higher Priority14
Simple Queue Monitor It is possible to get graph for each queuesimple rule Graphs show how much traffic is passedtrough queue14
Simple Queue MonitorLet’s enable graphingfor Queues14
Simple Queue Monitor Graphs areavailable onWWW To viewgraphshttp://router IP You can giveit to yourcustomer14
Advanced Queing14
Mangle Mangle is used to mark packets Separate different type of traffic Marks are active within the router Used for queue to set different limitation Mangle do not change packet structure(except DSCP, TTL specific actions)14
MangleActions14
MangleActions Mark-connection uses connectiontracking Information about new connection added toconnection tracking table Mark-packet works with packet directly Router follows each packet to apply markpacket14
Optimal Mangle Queues have packet-mark option only14
Optimal Mangle Mark new connection with markconnection Add mark-packet for every markconnection14
Mangle Example Imagine you have second client on therouter network with 192.168.X.55 IPaddress Let’s create two different marks (Gold,Silver), one for your computer and secondfor 192.168.X.5515
Mark Connection15
Mark Packet15
Mangle Example Add Marks for second user too There should be 4 mangle rules for twogroups15
Advanced Queuing Replace hundreds of queues with just few Set the same limit to any user Equalize available bandwidth betweenusers15
PCQ PCQ is advanced Queue type PCQ uses classifier to divide traffic (fromclient point of view; src-address is upload,dst-address is download)15
PCQ, one limit to all PCQ allows to set one limit to all userswith one queue15
One limit to all Multiple queue rules are changed by one15
PCQ, equalizebandwidth Equally share bandwidth betweencustomers15
Equalize bandwidth 1M upload/2M download is shared betweenusers15
PCQ Lab Teacher is going to make PCQ lab on therouter Two PCQ scenarios are going to be usedwith mangle16
Summary16
Wireless16
What is Wireless RouterOS supports various radiomodules that allow communication overthe air (2.4GHz and 5GHz) MikroTik RouterOS provides a completesupport for IEEE 802.11a, 802.11b and802.11g wireless networking standards16
Wireless Standards IEEE 802.11b - 2.4GHz frequencies,11Mbps IEEE 802.11g - 2.4GHz frequencies,54Mbps IEEE 802.11a - 5GHz frequencies,54Mbps IEEE 802.11n -draft, 2.4GHz - 5GHz16
802.11 b/g Channels12345678910112400 (11) 22 MHz wide channels (US) 3 non-overlapping channels 3 Access Points can occupy same area withoutinterfering162483
802.11a 557455765525652505200152505240160526016158055815 (12) 20 MHz wide channels (5) 40MHz wide turbo channels166064530053205290580057855852805350
Supported BandsAll 5GHz (802.11a) and 2.4GHz (802.11b/g),including small channels16
SupportedFrequencies Depending on your country regulationswireless card might support 2.4GHz: 2312 - 2499 MHz 5GHz: 4920 - 6100 MHz16
Apply CountryRegulationsSet wireless interfaceto apply yourcountry regulations16
RADIO Name We will use RADIO Name for the samepurposes as router identity Set RADIO Name as Number YourName17
Wireless Network17
Station Configuration Set Interfacemode station Select band Set SSID, WirelessNetwork Identity Frequency is notimportant for client,use scan-list17
Connect List Set of rulesused bystation toselectaccesspoint17
Connect List Lab Currently your router is connected toclass access-point Let’s make rule to disallow connection toclass access-point Use connect-list matchers17
Access PointConfiguration Set Interfacemode ap-bridge Select band Set SSID, WirelessNetwork Identity Set Frequency17
Snooper wirelessmonitor Use Snooper toget total view ofthe wirelessnetworks onused band Wirelessinterface isdisconnectedat this moment17
Registration Table View allconnectedwirelessinterfaces17
Security on Access Point Access-list isused to set MACaddress security Disable DefaultAuthentication touse only Accesslist17
Default Authentication Yes, Access-List rules are checked,client is able to connect, if there is nodeny rule No, only Access-List rule are checked17
Access-List Lab Since you have mode station configuredwe are going to make lab on teacher’srouter Disable connection for specific client Allow connection only for specific clients18
Security Let’s enable encryption on wirelessnetwork You must use WPA or WPA2 encryptionprotocols All devices on the network should havethe same security options18
Security Let’s create WPAencryption for ourwireless network WPA Pre-SharedKey ismikrotiktraining18
Configuration Tip To view hidden PreShared Key, click onHide Passwords It is possible to viewother hiddeninformation, exceptrouter password18
Drop Connectionsbetween clientsDefault-Forwarding usedto disablecommunications betweenclients connected to thesame access-point18
Default Forwarding Access-List rules have higher priority Check your access-list if connectionbetween client is working18
Nstreme MikroTik proprietary wireless protocol Improves wireless links, especially longrange links To use it on your network, enableprotocol on all wireless devices of thisnetwork18
Nstreme Lab Enable Nstremeon your router Check theconnection status Nstreme shouldbe enabled onboth routers18
Summary18
Bridging18
Bridge Wireless NetworkYour LaptopClass APYour Router192.168.X. 192.168.X.2514DHCP-ClientLet’s get back to our configuration19
Bridge WirelessNetworkWe are going to createone big network19
Bridge We are going to bridge local Ethernetinterface with Internet wireless interface Bridge unites different physical interfacesinto one logical interface All your laptops will be in the samenetwork19
Bridge To bridge you need to createbridge interface Add interfaces to bridge ports193
Create Bridge Bridge is configured from /interfacebridge menu194
Add Bridge Port Interfaces are added to bridge viaports195
Bridge There are no problems to bridge Ethernetinterface Wireless Clients (mode station) do notsupport bridging due the limitation of802.1119
Bridge Wireless WDS allows to add wireless client tobridge WDS (Wireless Distribution System)enables connection between AccessPoint and Access Point19
Set WDS Mode Station-wds isspecial stationmode withWDS support19
Add Bridge Ports Add public andlocal interface tobridge Ether1 (local),wlan1 (public)19
Access Point WDS Enable WDS on AP-bridge, usemode dynamic-mesh WDS interfaces are created on the fly Use default bridge for WDS interfaces Add Wireless Interface to Bridge20
AP-bridge Set AP-bridgesettings Add Wirelessinterface to bridge20
WDS configuration Use dynamic-meshWDS mode WDS interfaces arecreated on the fly Others AP should usedynamic-mesh too20
WDS WDS link isestablished Dynamic interfaceis present20
WDS Lab Delete masquerade rule Delete DHCP-client on router wirelessinterface Use mode station-wds on router Enable DHCP on your laptop Can you ping neighbor’s laptop20
WDS Lab Your Router is Transparent Bridge now You should be able to ping neighborrouter and computer now Just use correct IP address20
Restore Configuration To restore configuration manually change back to Station mode Add DHCP-Client on correct interface Add masquerade rule Set correct network configuration tolaptop20
Summary20
Routing20
Route Networks Configuration is back Try to ping neighbor’s laptop Neighbor’s address 192.168.X.1 We are going to learn how to use routerules to ping neighbor laptop20
Route ip route rules define where packetsshould be sent Let’s look at /ip route rules21
Routes Destination:networkswhich can bereached Gateway:IP of the nextrouter to reachthedestination21
Default GatewayDefault gateway:next hop routerwhere all (0.0.0.0)traffic is sent21
Set Default Gateway Lab Currently you have default gatewayreceived from DHCP-Client Disable automatic receiving of defaultgateway in DHCP-client settings Add default gateway manually21
Dynamic Routes Look at theother routes Routes withDAC areaddedautomatically DAC routecomes from IPaddressconfiguration21
Routes A - active D - dynamic C - connected S - static21
Static Routes Our goal is to ping neighbor laptop Static route will help us to achieve this21
Static Route Static route specifies how to reachspecific destination network Default gateway is also static route, itsends all traffic (destination 0.0.0.0) tohost - the gateway21
Static Route Additional static route is required toreach your neighbor laptop Because gateway (teacher’s router)does not have information aboutstudent’s private network21
Route to YourNeighbor Remember the network structure Neighbor’s local network is192.168.x.0/24 Ask your neighbor the IP address of theirwireless interface21
Network Structure22
Route To YourNeighbor Add one route rule Set Destination, destination isneighbor’s local network Set Gateway, address which is used toreach destination - gateway is IPaddress of neighbor’s router wirelessinterface22
Route Your Neighbor Add static route Set Destinationand Gateway Try to pingNeighbor’sLaptop22
Router To YourNeighborYou should be able to ping neighbor’s laptop now22
Dynamic Routes The same configuration is possible withdynamic routes Imagine you have to add static routes toall neighbors networks Instead of adding tons of rules, dynamicrouting protocols can be used22
Dynamic Routes Easy in configuration, difficult inmanaging/troubleshooting Can use more router resources22
Dynamic Routes We are going to use OSPF OSPF is very fast and optimal fordynamic routing Easy in configuration22
OSPF configuration Add correctnetwork toOSPF OSPFprotocol willbe enabled22
OSPF LAB Check route table Try to ping other neighbor now Remember, additional knowledge requiredto run OSPF on the big network22
Summary22
Local NetworkManagement23
Access to LocalNetwork Plan network design carefully Take care of user’s local access to thenetwork Use RouterOS features to secure localnetwork resources23
ARP Address Resolution Protocol ARP joins together client’s IP addresswith MAC-address ARP operates dynamically, but can alsobe manually configured23
ARP TableARP tableprovides: IPaddress, MACaddress andInterface23
Static ARP table To increase network security ARP entriescan be crated manually Router’s client will not be able to accessInternet with changed IP address23
Static ARPconfiguration Add Static Entry toARP table Set for interfacearp reply-only todisable dynamicARP creation Disable/enableinterface or rebootrouter23
Static ARP Lab Make your laptop ARP entry as static Set arp reply-only to Local Networkinterface Try to change computer IP address Test Internet connectivity23
DHCP Server Dynamic Host Configuration Protocol Used for automatic IP addressdistribution over local network Use DHCP only in secure networks23
DHCP Server To setup DHCP server you should have IPaddress on the interface Use setup command to enable DHCP server It will ask you for necessary information23
DHCP-Server clientaddressmaythatuseSetSetNetworkGatewayfor DHCP,forWearedone!to sstoto aceforclientsDHCP server23
Important To configure DHCP server on bridge,set server on bridge interface DHCP server will be invalid, when it isconfigured on bridge port24
DHCP Server Lab Setup DHCP server on EthernetInterface where Laptop is connected Change computer Network settings andenable DHCP-client (Obtain an IPaddress Automatically) Check the Internet connectivity24
DHCP ServerInformationLeases provideinformation aboutDHCP clients24
Winbox Configuration TipShow orhidedifferentWinboxcolumns24
Static Lease We can makelease to be static Client will not getother IP address24
Static Lease DHCP-server could run without dynamicleases Clients will receive only preconfigured IPaddress24
Static Lease Set Address-Pool tostatic-only Create Static leases24
HotSpot24
HotSpot Tool for Instant Plug-and-Play Internetaccess HotSpot provides authentication ofclients before access to public network It also provides User Accounting24
HotSpot Usage Open Access Points, Internet Cafes,Airports, universities campuses, etc. Different ways of authorization Flexible accounting24
HotSpot Requirements Valid IP addresses on Internet and LocalInterfaces DNS servers addresses added to ip dns At least one HotSpot user25
HotSpot Setup HotSpot setup is easy Setup is similar to DHCP Server setup25
HotSpot Setup Run ip hotspotsetup Select Inteface Proceed toanswer thequestionsThat’s all for resswillcertificatewillbe erfaceDNS nameHotSpottoserverbe(e-mails)togetherselectedfor urHotSpotclientsclientsSMTPorservernotrun HotSpot on25
Important Notes Users connected to HotSpot interface willbe disconnected from the Internet Client will have to authorize in HotSpot toget access to Internet25
Important Notes HotSpot default setup creates additionalconfiguration: DHCP-Server on HotSpot Interface Pool for HotSpot Clients Dynamic Firewall rules (Filter and NAT)25
HotSpot Help HotSpot login page is provided whenuser tries to access any web-page To logout from HotSpot you need to go tohttp://router IP orhttp://HotSpot DNS25
HotSpot Setup Lab Let’s create HotSpot on local Interface Don’t forget HotSpot login and passwordor you will not be able to get the Internet25
HotSpot Network HostsInformation about clients connected to HotSpot router25
HotSpot Active TableInformation aboutauthorizedHotSpot clients25
User ManagementAdd/Edit/RemoveHotSpot users25
HotSpot WalledGarden Tool to get access to specific resourceswithout HotSpot authorization Walled-Garden for HTTP and HTTPS Walled-Garden IP for other resources(Telnet, SSH, Winbox, etc.)26
HotSpot Walled-GardenAllow access tomikr
What is RouterOS ? RouterOS is an operating system that will make your device: a dedicated router a bandwidth shaper a (transpa
MikroTik 2012 MikroTik RouterOS Workshop Load Balancing Best Practice Warsaw MUM Europe 2012
RouterOS history 2001 – MikroTik v2.2 Router Software – MikroTik v2.3 Router Software npk first mentioned as method for extending functionality Jan 2002 – MikroTik
Media Convertor AT-MC103XL-20 3 Mikrotik S-3553LC20D SFP 20km BiDir (pair) 4 Mikrotik S 31DLC10D SFP 10km 3 Mikrotik S 2332LC10D SFP 10km BiDir (pair) 3 Mikrotik SFP 3m direct attach cable 2 Mikrotik S-31DLC20D 2 D-Link DGE-528T 5 Dell Memory Upgrade - 32GB - 4Rx4 DDR
How to use RouterOS on GNS3 Amnuay Pintong (MTCNA,MTCTCE,MTCUME) - Otik Nework Co.,Ltd. Start emulator for install RouterOS from ISO file. Start to install RouterOS Press ‘ a ‘ for select all package (you can choose some items fo
MikroTik RouterOS Online Training Class –Special Series 3 Burmese Version. EOIP VPN in Hub and Spoke Topology Presented by Phyo
10 Learn RouterOS – Second Edition by Dennis Burgess Introduction MikroTik RouterOS is a routing software that has been growing in popularity extremely quickly. When it is combined with reliabl
RESET RouterOS reset jumper hole (RESET, marked with a black circle in the diagram above, below S301) – resets RouterOS software to defaults. Must short circuit the metallic sides of the hole (with a screwdriver, for example) and boot the device. Hold screwdriver in place until RouterOS
making formal decisions at the final “appeal” stage of our process (see page 75 for more details ) All figures relate to the financial year 2012/2013. 4 annual review 2012/2013 . Financial Ombudsman Service Financial Ombudsman Service . annual review 2012/2013 5. chairman’s foreword. Sir Nicholas Montagu . kcb. we have resolved . more cases. than in any previous year – and each of .