Solutions To Review Questions And Problems
Computer Networking: A Top-Down ApproachFeaturing the Internet, 5th EditionSolutions to Review Questions and ProblemsVersion Date: 1 September 2009This document contains the solutions to review questions and problems for the 5thedition of Computer Networking: A Top-Down Approach Featuring the Internet by JimKurose and Keith Ross. These solutions are being made available to instructors ONLY.Please do NOT copy or distribute this document to others (even other instructors). Pleasedo not post any solutions on a publicly-available Web site. We’ll be happy to provide acopy (up-to-date) of this solution manual ourselves to anyone who asks.Acknowledgments: Over the years, several students and colleagues have helped usprepare this solutions manual. Special thanks goes to Honggang Zhang, Rakesh Kumar,and Prithula Dunghel.All material copyright 1996-2009 by J.F. Kurose and K.W. Ross. All rights reserved
Chapter 1 Review Questions1. There is no difference. Throughout this text, the words “host” and “end system” areused interchangeably. End systems include PCs, workstations, Web servers, mailservers, Internet-connected PDAs, WebTVs, etc.2. Suppose Alice, an ambassador of country A wants to invite Bob, an ambassador ofcountry B, over for dinner. Alice doesn’t simply just call Bob on the phone and say,“come to our dinner table now”. Instead, she calls Bob and suggests a date and time.Bob may respond by saying he’s not available that particular date, but he is availableanother date. Alice and Bob continue to send “messages” back and forth until theyagree on a date and time. Bob then shows up at the embassy on the agreed date,hopefully not more than 15 minutes before or after the agreed time. Diplomaticprotocols also allow for either Alice or Bob to politely cancel the engagement if theyhave reasonable excuses.3. A networking program usually has two programs, each running on a different host,communicating with each other. The program that initiates the communication is theclient. Typically, the client program requests and receives services from the serverprogram.4. 1. Dial-up modem over telephone line: residential; 2. DSL over telephone line:residential or small office; 3. Cable to HFC: residential; 4. 100 Mbps switchedEtherent: company; 5. Wireless LAN: mobile; 6. Cellular mobile access (for example,WAP): mobile5. HFC bandwidth is shared among the users. On the downstream channel, all packetsemanate from a single source, namely, the head end. Thus, there are no collisions inthe downstream channel.6. Current possibilities include: dial-up; DSL; cable modem; fiber-to-the-home.7. Ethernet LANs have transmission rates of 10 Mbps, 100 Mbps, 1 Gbps and 10 Gbps.For an X Mbps Ethernet (where X 10, 100, 1,000 or 10,000), a user cancontinuously transmit at the rate X Mbps if that user is the only person sending data.If there are more than one active user, then each user cannot continuously transmit atX Mbps.8. Ethernet most commonly runs over twisted-pair copper wire and “thin” coaxial cable.It also can run over fibers optic links and thick coaxial cable.9. Dial up modems: up to 56 Kbps, bandwidth is dedicated; ISDN: up to 128 kbps,bandwidth is dedicated; ADSL: downstream channel is .5-8 Mbps, upstream channelis up to 1 Mbps, bandwidth is dedicated; HFC, downstream channel is 10-30 Mbpsand upstream channel is usually less than a few Mbps, bandwidth is shared. FTTH: 210Mbps upload; 10-20 Mbps download; bandwidth is not shared.
10. There are two most popular wireless Internet access technologies today:a) Wireless LANIn a wireless LAN, wireless users transmit/receive packets to/from a base station(wireless access point) within a radius of few tens of meters. The base station istypically connected to the wired Internet and thus serves to connect wireless usersto the wired network.b) Wide-area wireless access networkIn these systems, packets are transmitted over the same wireless infrastructureused for cellular telephony, with the base station thus being managed by atelecommunications provider. This provides wireless access to users within aradius of tens of kilometers of the base station.11. A circuit-switched network can guarantee a certain amount of end-to-end bandwidthfor the duration of a call. Most packet-switched networks today (including theInternet) cannot make any end-to-end guarantees for bandwidth.12. In a packet switched network, the packets from different sources flowing on a link donot follow any fixed, pre-defined pattern. In TDM circuit switching, each host getsthe same slot in a revolving TDM frame.13. At time t0 the sending host begins to transmit. At time t1 L/R1, the sending hostcompletes transmission and the entire packet is received at the router (no propagationdelay). Because the router has the entire packet at time t1, it can begin to transmit thepacket to the receiving host at time t1. At time t2 t1 L/R2, the router completestransmission and the entire packet is received at the receiving host (again, nopropagation delay). Thus, the end-to-end delay is L/R1 L/R2.14. A tier-1 ISP connects to all other tier-1 ISPs; a tier-2 ISP connects to only a few ofthe tier-1 ISPs. Also, a tier-2 ISP is a customer of one or more tier-1.15. a) 2 users can be supported because each user requires half of the link bandwidth.b) Since each user requires 1Mbps when transmitting, if two or fewer users transmitsimultaneously, a maximum of 2Mbps will be required. Since the availablebandwidth of the shared link is 2Mbps, there will be no queuing delay before thelink. Whereas, if three users transmit simultaneously, the bandwidth requiredwill be 3Mbps which is more than the available bandwidth of the shared link. Inthis case, there will be queuing delay before the link.c) Probability that a given user is transmitting 0.2 3 3 3d) Probability that all three users are transmitting simultaneously p 3 (1 p )3
(0.2)3 0.008. Since the queue grows when all the users are transmitting, thefraction of time during which the queue grows (which is equal to the probabilitythat all three users are transmitting simultaneously) is 0.008.16. The delay components are processing delays, transmission delays, propagationdelays, and queuing delays. All of these delays are fixed, except for the queuingdelays, which are variable.17. Java Applet18. 10msec; d/s; no; no19. a) 500 kbpsb) 64 secondsc) 100kbps; 320 seconds20. End system A breaks the large file into chunks. To each chunk, it adds headergenerating multiple packets from the file. The header in each packet includes theaddress of the destination: end system B. The packet switch uses the destinationaddress to determine the outgoing link. Asking which road to take is analogous to apacket asking which outgoing link it should be forwarded on, given the packet’saddress.21. Java Applet22. Five generic tasks are error control, flow control, segmentation and reassembly,multiplexing, and connection setup. Yes, these tasks can be duplicated at differentlayers. For example, error control is often provided at more than one layer.23. The five layers in the Internet protocol stack are – from top to bottom – theapplication layer, the transport layer, the network layer, the link layer, and thephysical layer. The principal responsibilities are outlined in Section 1.5.1.24. Application-layer message: data which an application wants to send and passed ontothe transport layer; transport-layer segment: generated by the transport layer andencapsulates application-layer message with transport layer header; network-layerdatagram: encapsulates transport-layer segment with a network-layer header; linklayer frame: encapsulates network-layer datagram with a link-layer header.25. Routers process layers 1 through 3. (This is a little bit of a white lie, as modernrouters sometimes act as firewalls or caching components, and process layer four aswell.) Link layer switches process layers 1 through 2. Hosts process all five layers.26. a) VirusRequires some form of human interaction to spread. Classic example: E-mailviruses.
b)WormsNo user replication needed. Worm in infected host scans IP addresses and portnumbers, looking for vulnerable processes to infect.c) Trojan horseHidden, devious part of some otherwise useful software.27. Creation of a botnet requires an attacker to find vulnerability in some application orsystem (e.g. exploiting the buffer overflow vulnerability that might exist in anapplication). After finding the vulnerability, the attacker needs to scan for hosts thatare vulnerable. The target is basically to compromise a series of systems byexploiting that particular vulnerability. Any system that is part of the botnet canautomatically scan its environment and propagate by exploiting the vulnerability. Animportant property of such botnets is that the originator of the botnet can remotelycontrol and issue commands to all the nodes in the botnet. Hence, it becomespossible for the attacker to issue a command to all the nodes, that target a singlenode (for example, all nodes in the botnet might be commanded by the attacker tosend a TCP SYN message to the target, which might result in a TCP SYN floodattack at the target).28. Trudy can pretend to be Bob to Alice (and vice-versa) and partially or completelymodify the message(s) being sent from Bob to Alice. For example, she can easilychange the phrase “Alice, I owe you 1000” to “Alice, I owe you 10,000”.Furthermore, Trudy can even drop the packets that are being sent by Bob to Alice(and vise-versa), even if the packets from Bob to Alice are encrypted.Chapter 1 ProblemsProblem 1There is no single right answer to this question. Many protocols would do the trick.Here's a simple answer below:Messages from ATM machine to ServerMsg name-------HELO userid PASSWD passwd BALANCEWITHDRAWL amount BYEpurpose------Let server know that there is a card in theATM machineATM card transmits user ID to ServerUser enters PIN, which is sent to serverUser requests balanceUser asks to withdraw moneyuser all done
Messages from Server to ATM machine (display)Msg name-------PASSWDOKERRAMOUNT amt BYEpurpose------Ask user for PIN (password)last requested operation (PASSWD, WITHDRAWL)OKlast requested operation (PASSWD, WITHDRAWL)in ERRORsent in response to BALANCE requestuser done, display welcome screen at ATMCorrect operation:clientserverHELO (userid)-------------- ------------PASSWD passwd -------------- ------------BALANCE-------------- ------------WITHDRAWL amt -------------- (check if valid userid)PASSWD(check password)OK (password is OK)AMOUNT amt check if enough to coverwithdrawlOK ------------ATM dispenses BYE-------------- ------------- BYEIn situation when there's not enough money:HELO (userid)-------------- ------------PASSWD passwd -------------- ------------BALANCE-------------- ------------WITHDRAWL amt -------------- withdrawl ------------error msg displayedno given outBYE-------------- -------------(check if valid userid)PASSWD(check password)OK (password is OK)AMOUNT amt check if enough tocoverERR (not enough funds)BYEProblem 2a) A circuit-switched network would be well suited to the application described, becausethe application involves long sessions with predictable smooth bandwidthrequirements. Since the transmission rate is known and not bursty, bandwidth can be
reserved for each application session circuit with no significant waste. In addition, weneed not worry greatly about the overhead costs of setting up and tearing down acircuit connection, which are amortized over the lengthy duration of a typicalapplication session.b) Given such generous link capacities, the network needs no congestion controlmechanism. In the worst (most potentially congested) case, all the applicationssimultaneously transmit over one or more particular network links. However, sinceeach link offers sufficient bandwidth to handle the sum of all of the applications' datarates, no congestion (very little queuing) will occur.Problem 3a) We can have n connections between each of the four pairs of adjacent switches. Thisgives a maximum of 4n connections.b) We can n connections passing through the switch in the upper-right-hand corner andanother n connections passing through the switch in the lower-left-hand corner,giving a total of 2n connections.Problem 4Tollbooths are 75 km apart, and the cars propagate at 100km/hr. A tollbooth services acar at a rate of one car every 12 seconds.a) There are ten cars. It takes 120 seconds, or 2 minutes, for the first tollbooth to servicethe 10 cars. Each of these cars has a propagation delay of 45 minutes (travel 75 km)before arriving at the second tollbooth. Thus, all the cars are lined up before thesecond tollbooth after 47 minutes. The whole process repeats itself for travelingbetween the second and third tollbooths. It also takes 2 minutes for the third tollboothto service the 10 cars. Thus the total delay is 96 minutes.b) Delay between tollbooths is 8*12 seconds plus 45 minutes, i.e., 46 minutes and 36seconds. The total delay is twice this amount plus 8*12 seconds, i.e., 94 minutes and48 seconds.Problem 5a) d prop m / s seconds.b) d trans L / R seconds.c) d end to end (m / s L / R ) seconds.d) The bit is just leaving Host A.e) The first bit is in the link and has not reached Host B.f) The first bit has reached Host B.g) Want
m ()L120s 2.5 108 536 km.3R56 10Problem 6Consider the first bit in a packet. Before this bit can be transmitted, all of the bits in thepacket must be generated. This requires56 8sec 7msec.64 103The time required to transmit the packet is56 8sec 224 μ sec.2 106Propagation delay 10 msec.The delay until decoding is7msec 224 μ sec 10msec 17.224msecA similar analysis shows that all bits experience a delay of 17.224 msec.Problem 7a) 20 users can be supported.b) p 0.1 . 120 n p (1 p )120 n .c) n 20 120 n120 n p (1 p )d) 1 .n 0 n We use the central limit theorem to approximate this probability. Let X j be independentrandom variables such that P (X j 1) p .P ( “21 or more users” 120 ) 1 P X j 21 j 1 120 X j 12 120 9 j 1P X j 21 P 120 0.1 0.9 120 0.1 0.9 j 1
9 P Z P (Z 2.74 )3.286 0.997when Z is a standard normal r.v. Thus P ( “21 or more users” ) 0.003 .Problem 8a) 10,000M M M nb) p n (1 p )n N 1 n Problem 9The first end system requires L/R1 to transmit the packet onto the first link; the packetpropagates over the first link in d1/s1; the packet switch adds a processing delay of dproc;after receiving the entire packet, the packet switch connecting the first and the secondlink requires L/R2 to transmit the packet onto the second link; the packet propagates overthe second link in d2/s2. Similarly, we can find the delay caused by the second switch andthe third link: L/R3, dproc, and d3/s3.Adding these five delays givesdend-end L/R1 L/R2 L/R3 d1/s1 d2/s2 d3/s3 dproc dprocTo answer the second question, we simply plug the values into the equation to get 6 6 6 20 16 4 3 3 64 msec.Problem 10Because bits are immediately transmitted, the packet switch does not introduce any delay;in particular, it does not introduce a transmission delay. Thus,dend-end L/R d1/s1 d2/s2 d3/s3For the values in Problem 9, we get 6 20 16 4 46 msec.Problem 11The arriving packet must first wait for the link to transmit 6,750 bytes or 54,000 bits.Since these bits are transmitted at 2 Mbps, the queuing delay is 27 msec. Generally, thequeuing delay is (nL (L - x))/R.
Problem 12The queuing delay is 0 for the first transmitted packet, L/R for the second transmittedpacket, and generally, (n-1)L/R for the nth transmitted packet. Thus, the average delay forthe N packets is(L/R 2L/R . (N-1)L/R)/N L/(RN) * (1 2 . (N-1)) L/(RN) * N(N-1)/2 LN(N-1)/(2RN) (N-1)L/(2R)Note that here we used the well-known fact that1 2 . N N(N 1)/2Problem 13It takes LN / R seconds to transmit the N packets. Thus, the buffer is empty when abatch of N packets arrive.The first of the N packets has no queuing delay. The 2nd packet has a queuing delay ofL / R seconds. The n th packet has a delay of ( n 1) L / R seconds.The average delay isL 11 N(n 1) L / R N n 1RNN 1L 1 ( N 1) N L ( N 1). R22 n R Nn 0Problem 14a) The transmission delay is L / R . The total delay isILL L/R R(1 I ) R 1 Ib) Let x L / R .xTotal delay 1 axProblem 15Total delay L/ RL/ R1/ μ1 .1 I 1 aL / R 1 a / μ μ a
Problem 16The total number of packets in the system includes those in the buffer and the pack isbeing transmitted. So, N 10 1.Because N a d , so (10 1) a*(queuing delay transmission delay). That is,11 a*(0.01 1/100) a*(0.01 0.01), thus, a 550 packets/sec.Problem 17qa) There are Q nodes (the source host and the Q 1 routers). Let d procdenote theprocessing delay at the q th node. Let R q be the transmission rate of the q th link and letqqbe the propagation delay across the q th link. Thend trans L / R q . Let d propQ[]qqqd end to end d proc d trans d prop.q 1qb) Let d queuedenote the average queuing delay at node q . ThenQ[]qqqqd end to end d proc d trans d prop d queue.q 1Problem 18The command:traceroute -q 20 www.eurecom.frwill get 20 delay measurements from the issuing host to the host, www.eurecom.fr. Theaverage and standard deviation of these 20 measurements can then be collected. Do yousee any differences in your answers as a function of time of day?Problem 19Throughput min{Rs, Rc, R/M}Problem 20If only use one path, the max throughput is given bymax{min{ R11 , R21 , K , R1N }, min{ R12 , R22 , K , R N2 }, K , min{ R1M , R2M , K , R NM }} .
If use all paths, the max throughput is given byM min{Rk 1k1, R2k , K , RNk } .Problem 21Probability of successfully receiving a packet is:ps (1-p)N.The number of transmissions needs to be performed until the packet is successfullyreceived by the client is a geometric random variable with success probability ps.Thus, the average number of transmissions needed is given by: 1/psThen, the average number of re-transmissions needed is given by: 1/ps -1.Problem 22Lets call the first packet A and call the second packet B.a). If the bottleneck link is the first link, then, packet B is queued at the first link waitingfor the transmission of packet A. So, the packet inter-arrival time at the destination issimply L/Rs.b). If the second link is the bottleneck link and since both packets are sent back to back, itmust be true that the second packet arrives at the input queue of the second link beforethe second link finishes the transmission of the first packet. That is,L/Rs L/Rs dprop L/Rs dprop L/Rc (1)The left hand side of the above inequality represents the time needed by the secondpacket to arrive at the input queue of the second link (the second link has not startedtransmitting the second packet yet).The right hand side represents the time needed by the first packet to finish itstransmission onto the second link.We know that (1) is possible as Rc Rs. And it is clear that (1) shows that the secondpacket must have queuing delay at the input queue of the second link.If we send the second packet T seconds later, then we can ensure the there is no queuingdelay for the second packet at the second link if we have,L/Rs L/Rs dprop T L/Rs dprop L/RcThus, T must be L/Rc L/Rs .Problem 2340 terabytes 40 * 1012 * 8 bits.So, if using the dedicated link, it will take 40 * 1012 * 8 / (100 *106 ) 3200000 seconds 37 days.
But with FedEx overnight delivery, you can guarantee the data arrives in one day, and itonly costs you no more than 100.Problem 24a) 160,000 bitsb) 160,000 bitsc) The bandwidth-delay product of a link is the maximum number of bits that can be inthe link.d) the width of a bit length of link / ban
Computer Networking: A Top-Down Approach Featuring the Internet, 5th Edition . Solutions to Review Questions and Problems . Version Date: 1 September 2009 . This document contains the solutions to review questions and problems for the 5th edition of Computer Networking: A Top-Down Approach Featuring the Internet by Jim Kurose and Keith Ross.
work/products (Beading, Candles, Carving, Food Products, Soap, Weaving, etc.) ⃝I understand that if my work contains Indigenous visual representation that it is a reflection of the Indigenous culture of my native region. ⃝To the best of my knowledge, my work/products fall within Craft Council standards and expectations with respect to
EXAM MFE MODELS FOR FINANCIAL ECONOMICS . EXAM MFE SAMPLE QUESTIONS AND SOLUTIONS ADVANCED DERIVATIVES . These questions and solutions are from McDonald Chapters 9-14, 18-19, 23, and 25 only and are identical to questions from the former set of MFE sample questions. These questions are representative of the types of questions that might be asked of
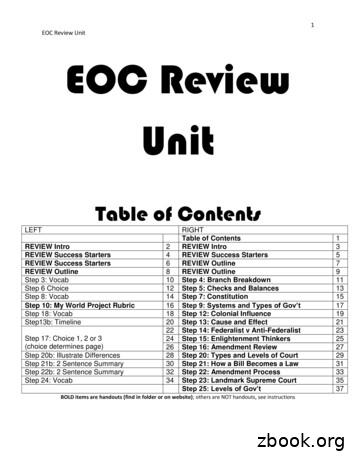
1 EOC Review Unit EOC Review Unit Table of Contents LEFT RIGHT Table of Contents 1 REVIEW Intro 2 REVIEW Intro 3 REVIEW Success Starters 4 REVIEW Success Starters 5 REVIEW Success Starters 6 REVIEW Outline 7 REVIEW Outline 8 REVIEW Outline 9 Step 3: Vocab 10 Step 4: Branch Breakdown 11 Step 6 Choice 12 Step 5: Checks and Balances 13 Step 8: Vocab 14 Step 7: Constitution 15
the public–private partnership law review the real estate law review the real estate m&a and private equity review the renewable energy law review the restructuring review the securities litigation review the shareholder rights and activism review the shipping law review the sports law review the tax disputes and litigation review
EXAM SRM SAMPLE QUESTIONS AND SOLUTIONS . These questions and solutions are representative of the types of questions that might be asked of candidates sitting for Exam SRM. These questions are intended to represent the . SRM-02-18 16 . 18. For a simple linear regress
Some of the questions have been reformatted from previous versions of this note. Questions 154-155 were added in October 2014. Questions 156-206 were added January 2015. Questions 207-237 were added April 2015. Questions 238-240 were added May 2015. Questions 241-242 were added November 2015. Questions 243-326 were added September 2016.
the product regulation and liability review the shipping law review the acquisition and leveraged finance review the privacy, data protection and cybersecurity law review the public-private partnership law review the transport finance law review the securities litigation review the lending and secured finance review the international trade law .
- licence for broadcasting means the document of the state sample, which is given out by the National Council of Ukraine concerning TV and broadcastings and confirms the right of the licensee in accordance with licence standards as to carry out the broadcasting, to use broadcast channels, broadcast networks, the channels of multi-channel TV networks; - licence of program service provider means .