Cryptography Based Authentication Methods
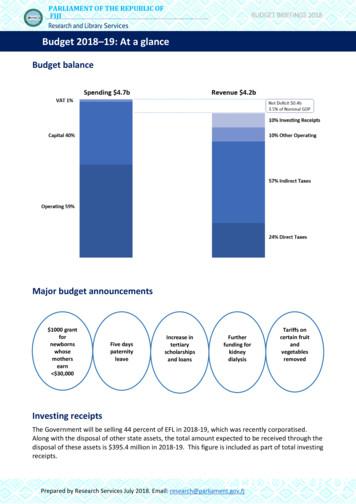
Proceedings of the World Congress on Engineering and Computer Science 2014 Vol IWCECS 2014, 22-24 October, 2014, San Francisco, USACryptography Based Authentication MethodsMohammad A. Alia, Abdelfatah Aref Tamimi, and Omaima N. A. AL-Allaf Abstract—This paper reviews a comparison study on themost common used authentication methods. Some of thesemethods are actually based on cryptography. In this study, weshow the main cryptographic services. As well as, this studypresents a specific discussion about authentication service.Since the authentication service is classified into severalcategorizes according to their methods. However, this studygives more about the real life example for each of theauthentication methods. It talks about the simplestauthentication methods as well about the available biometricauthentication methods such as voice, iris, fingerprint, and faceauthentication.increased recently for the public especially after the fastdevelopment of the Internet in the last 10 years tography, system access control, authentication, andnetwork security.Figure 1: Network security system [1]I. INTRODUCTIONIsecurity is the process which describes allmeasures taken to prevent unauthorized use of electronicdata, whether this unauthorized use takes the form ofdestruction, use, disclosure, modification, or disruption.Information security and cryptography are interconnectedand share the common services of protecting theconfidentiality, integrity and availability of the informationignoring data form (electronic document, printeddocument). In the encryption process, information securityuses cryptograph to shift the information into the cipherform which does not allow it to be used by unauthorizedpersonnel.NFORMATIONCryptography provides the information security for otheruseful applications such as in encryption, message digests,and digital signatures. The length and strength of theCryptography keys are considered an important mechanism.The keys used for encryption and decryption must be strongenough to produce strong encryption. They must beprotected from unauthorized users and must be availablewhen they are needed. Cryptography also contributes tocomputer science, particularly, in the techniques used incomputer and network security for access control andinformation confidentiality. Cryptography is also used inmany applications encountered in everyday life such as:computer passwords, ATM cards, and electronic commerce(refer to Figure 1). The request for Cryptography system hasManuscript received June 10, 2014; revised July 09, 2014. This workwas supported in part by Al Zaytoonah University of Jordan.All authors are with Faculty of Science and Information Technology –Al Zaytoonah University of Jordan, P.O.Box: 130 Amman (11733) Jordan.Email of Dr. Mohammad A. Alia is dr.m.alia@zuj.edu.jo.Email of Dr. Abdelfatah Aref Tamimi is drtamimi@zuj.edu.jo.Email of Dr. Omaima N. A. AL-Allaf is omaimaalallaf@zuj.edu.joISBN: 978-988-19252-0-6ISSN: 2078-0958 (Print); ISSN: 2078-0966 (Online)This paper summarized the development in cryptographybased authentication. The paper discusses the latestdevelopment on the real life authentication methods whichinclude symmetric, public-key, token, and biometricauthentication methods.II. CRYPTOGRAPHYCryptography is one of the most important fields incomputer security. It is a method of transferring privateinformation and data through open network communication,so only the receiver who has the secret key can read theencrypted messages which might be documents, phoneconversations, images or other form of data (refer to Figure2).Figure 2: Cryptography schemeTo implement privacy simply by encrypting theinformation intended to remain secret can be achieved byusing methods of Cryptography. The information must bescrambled, so that other users will not be able to access theactual information. For example, in a multi-users system,each user may keep his privacy intact via her/his ownpassword. On internet, a large number of internet users useWCECS 2014
Proceedings of the World Congress on Engineering and Computer Science 2014 Vol IWCECS 2014, 22-24 October, 2014, San Francisco, USAinternet application, such as business, research, learning,etc. These activities are very important for the users’application; hence, the importance of using Cryptographyhas been highlighted to help them keep the privacy.Cryptography services in general help to ensure thefollowing [3]: Authentication: Authentication is a service used toprovide the identity of an entity. Confidentiality: Confidentiality is a service used toguarantee information it is accessible only to authorizedentities and is inaccessible to others. Integrity: Integrity is a service used to guarantee that theinformation remains unchanged from the source entity tothe destination entity. Non-repudiation: Non-repudiation is a service used toconfirm the involvement of an entity in a certain formcommunication, and prevents any party from denyingthe sent message. Accessibility: Accessibility is a service put in place toallow the use of information resources by authorizedentities.Cryptography algorithms can be classified into threeboard categories, asymmetric (public-key) cryptosystem,symmetric (secret-key) cryptosystem and hash functions(refer to Figure 3). In general, Cryptography protocolemploys asymmetric cryptosystem to exchange the secretkey and then uses faster secret key algorithms to ensureconfidentiality of the data stream [2, 3]. Symmetriccryptosystem (Secret-key algorithm) is used to encrypt anddecrypt messages by using the same secret key. While hashfunctions are a non-public key cryptography and workwithout key. As well hash functions are normally used asdata integrity primitive in more complicated cryptographicprotocols. However, the secure hash algorithm (SHA) wasissued by the National Institute of Standards andTechnology in 1995 as a FIPS [4]. Asymmetriccryptosystem on the other hand, works in a very differentway. In public key algorithm, there are two keys; bothbelong to one party, either the recipient or the sender. Onekey is used to accomplish half of the task (e.g. encryption)while the other key will be used to complete the rest of thetask (e.g. decryption).III. SYSTEM ACCESS CONTROL (LOGGING TO SYSTEM)The system access control process [5] is interconnectedand shared between the information security andcryptographic aspects. Ensuring that unauthorized usersdon't get into the system. The system control also protectspassword data and keeps track of who's doing what in thesystem. However, this process is used to ensure that thesystem it is accessible only to authorized entities and isinaccessible to others. System access control processprovides the computer security with the first security layerby controlling access to that system: Who's allowed to login? How does the system decide whether a user islegitimate? How does the system keep track of who's doingwhat in the system?However, logging into a system by the access controlprocess is a kind of challenge/response scenario. Thisscenario should be done by identification and authenticationprocesses.Identification and authentication [5] (I&A) is the processthat can be used to identify and verify the users on theirsecure systems. In secure system, the user must identifyhimself/herself, then the system will authenticate theidentity before using the system. However, authenticationverifies the user who is requesting access process ofdetermining the identity of a user that is attempting to accessa system [5, 7]. Therefore, the identification andauthentication processes can be done successfully throughthe following three classical ways:1. Something known: password, or a personalidentification number (PIN).2. Something possessed: smart card or token.3. Something inherent: face (Biometric) detection andrecognition, fingerprint, voice, retina, or irischaracteristics.Figure 3: Main branches of CryptographyISBN: 978-988-19252-0-6ISSN: 2078-0958 (Print); ISSN: 2078-0966 (Online)WCECS 2014
Proceedings of the World Congress on Engineering and Computer Science 2014 Vol IWCECS 2014, 22-24 October, 2014, San Francisco, USAOn other hand, the identification and authenticationprocessed can be also professionally seen as:4. SMS based authentication5. Symmetric-key authentication6. Public-key authenticationMeanwhile, this study discusses the common usedauthentication techniques on our lifetime. As well as, itshows a performance comparison study between them intem of the security level and the execution time.IV. AUTHENTICATION METHODSA. Password authentication protocolA password authentication protocol (PAP) is anauthentication protocol used by Point to Point Protocol toauthenticate users before allowing them access to dataresources. Password [6] is the most common used method inauthentication protocols. Whereby, the user should provehis/her username and password by comparing it with thesystem stored value. This authentication method isimportant for users since it is easy to be memorized.However, password can be recently classified into two maintypes; textual password and graphical password.Graphical password: A graphical password (refer toFigure 4) is one of the most important fields ofauthentication in system access control techniques. It allowsusers to draw or select their passwords from images bar, in aspecific order. Then the password will be presented in agraphical user interface (GUI). On other hand, the graphicalpassword is also defined as graphical user authentication(GUA). Therefore, graphical password is considered easierthan other password techniques base text, since it is easy tobe remembered for most computer users. In term of security,graphical password offers better security than other textualpasswords because the graphical password is created byselectable images as a series. These series is normallycombined in specific order of images. Therefore, thegraphical passwords are recently designed to be resisted tomany kinds of attacks such as; shoulder-surfing. Whereas, itwill be difficult to recognize the exact images series order(graphical password) by attackers [7].Figure 4: Graphical password [7]Figure 5: the challenge response card from Cryptocard [8]Figure 6: An example of the Time-based Token Authentication System [8].B. Authentication TokenIs a portable device used for authenticating users (refer tofigures 5, 6, 7, and 8), thereby it is allowing authorizedaccess into a network system. Authentication techniqueusing a portable device to carry the embedded software thatis called software token. There are several token systems,among these are: RSA SecureID Token Cryptocards,Challenge Response Token, and Time based Tokens.However, Challenge Response Token is an authenticationtechnique using a calculator type token that containsidentical security keys or algorithms as a Network AccessServer (NAS) [8].Figure 7: Token Authentication System [8 ].ISBN: 978-988-19252-0-6ISSN: 2078-0958 (Print); ISSN: 2078-0966 (Online)WCECS 2014
Proceedings of the World Congress on Engineering and Computer Science 2014 Vol IWCECS 2014, 22-24 October, 2014, San Francisco, USAE. Biometric authenticationFigure 8: RSA SecureID Token [8]C. Symmetric-key AuthenticationIn symmetric key authentication, the user shares a single,secret key with an authentication server (normally the key isembedded in a token) [9]. The user is authenticated bysending to the authentication server his/her usernametogether with a randomly challenge message that isencrypted by the secret key. Whereby, the user is consideredas authenticated user if the server can match the receivedencrypted message using its share secret key.D. Public key authentication: Diffie-Hellman AuthenticationThe key exchange is an important method in public-keyCryptography for providing authentication cryptographicservice. It was the first public-key cryptographic scenario asdeveloped by Whitfield Diffie and Martin Hellman [10],were the first who developed the key exchange algorithmthat is called DH. In DH, keys are exchanged between theusers according to Cryptography protocols which are basedon the key exchange problem. They highlighted the mostimportant method of exchanging the keys by using thediscrete logarithm hard problem (refer to Figure 9).A biometric authentication is a digitizing measurementsof a physiological or behavioral characteristic for human. Abiometric authentication systems can theoretically be usedto distinguish one person from. However, many biometricauthentication systems have been proposed which arecategorized as; face detection authentication system,fingerprint authentication system, Iris authentication system,and voice authentication system [11] (refer to Table 1).1) Fingerprint recognitionA fingerprint system uses an electronic device to capturea digital image of the fingerprint pattern. This capturedimage in fingerprint system is called a live scan which isdigitally processed to create a biometric template (fingerfeatures). The biometric features will be later stored andused for matching process.2) Voice biometric authenticationVoice biometric authentication is the use of the voicepattern to recognize the identity of the person. Meanwhile,voice authentication is now considered as a fast widedeployed form of biometric authentication. However, it isone of the best methods of determining the biometricmethod efficacy. However, voice recognition is categorizedinto five types: speaker dependent system, speakerindependent system, discrete speech recognition, continuousspeech recognition, and natural language.3) Face detectionFace detection and recognition systems are a twocomplementary scenarios [11]. Face detection is astechnology uses learning algorithms to allocate human facesin digital images. As shown by Figure 10, face detectionalgorithm focuses and determines the facial features andignores anything else in the digital images [11, 12].Moreover, many face detection techniques have beenpresented such as; Viola and Jones face detection [13], facedetection based Adaboost [14], semi-supervised learning forfacial expression recognition [15], and etc.Figure 9: Diffie-Hellman key exchange protocolISBN: 978-988-19252-0-6ISSN: 2078-0958 (Print); ISSN: 2078-0966 (Online)Figure 10: Face detection [11].WCECS 2014
Proceedings of the World Congress on Engineering and Computer Science 2014 Vol IWCECS 2014, 22-24 October, 2014, San Francisco, USAFurthermore, face recognition technology is a naturalbiological authentication process according to the cognitiverule of human beings. This technology is used to identifyany given face image using the main features of thisface [16]. Normally, face recognition process works afterface detection process to identify the detected face bycomparing the detected faces with the stored faces images.In general, different artificial neural network algorithmshave been proposed such as; feedforwardbackpropagation neural network (FFBPNN), cascade forwardback propagation neural network (CFBPNN), functionfitting neural network (FitNet), and pattern recognitionneural network (PatternNet) algorithms [16]. Since, Soonand Seiichi [17], While Volkan [18], Weihua and WeiFu[19] are recognition systems applied on neural algorithms.security (refer to Table 1).TABLE 1:PERFORMANCE COMPARISON BETWEEN BIOMETRIC AUTHENTICATIONMETHODS [20]VI. CONCLUSION4) Iris AuthenticationActually, iris and fingerprints are parallel in theiruniqueness technology. Worldly, the statistical result of theiris usage in authentication is presents that iris is one of thebest ways of meeting high risk situations. Iris recognitionsoftware is currently in wide use at airport borders. As wellas, it is also widely used at many other industries for doingauthentication.V. DISCUSSIONAs discussed earlier, password authentication system isthe most common used method in authentication protocols.In the meantime, password works with very low cos, since itjust needs keyboard system or mouse system in best cases.In term of security, the use of password authentication isconsidered very weak, this is because of the softwareattacks. However, password software attack is embeddedand activated by visiting a fake site that looks like thenormal commercial site (phishing attack). As well as, somefake web site has developed keyboard logging software tocopy the user ID and password. On other hand, this studyshows that the password authentication system is highlysecure if the password is computed between thecommunication parties over insecure medium by usingpublic-key cryptographic system such as DH protocol.However, the comparison talks about the security tokenwhich is more closely with the users. It reduces the risk onthe user password, since the password can be sometimeencrypted by the embedded public key cryptosystem.Moreover, the standard token system is only useful for lowto medium risk type authentication situations. Whereby,High risk authentications should implement multi-factorauthentication.In biometric systems, iris biometric authentication shouldbe provided for high risk conditions. Whereby, voiceauthentication is efficiently the fast wide deployed form ofbiometric authentication. As well as, face recognitionalgorisms are considered more complex and secure thanother authentication algorithms such as fingerprint, iris andvoice authentication algorithms. Comparing facerecognition to other techniques, face recognition is featuredas: accurate and fast Identification, and high usability andISBN: 978-988-19252-0-6ISSN: 2078-0958 (Print); ISSN: 2078-0966 (Online)This paper summarizes the difference betweencryptography based authentication methods. It shows thepossibility of using public key cryptosystem to provide highlevel of authentication security. The surveyed methods arepassword, public key sharing, symmetric key, token, andbiometric authentication methods. The performance of thesemethods are actually different according to their tools cost,execution time and the security. However, this studyhighlights that the DH public key method provides highlevel of security to distribute the secret key (password)between users over insecure communication without anyextra tool cost. Whereby, most of the biometric methods arealso secure, professional and provides very accurateauthentication process, but sometime they need extra toolswhich are required extra cost. Therefore, the surveyedpublic key authentication is good alternative to thetraditional biometric methods.ACKNOWLEDGMENTThe authors would like to thank Al Zaytoonah Universityof Jordan for supporting this study.REFERENCES[1][2][3][4][5][6][7][8]Macroview Telecom Group (2006) Network Security Solutions.Macroview Telecom Group. Available from World Wide vic, R. Giorgi, E. Martinelli, “Memory Performance of PublicKey Cryptography Methods in Mobile Environments”, ACMSIGARCH Workshop on Memory performance: Dealing withApplications, systems and architecture (MEDEA-03), New Orleans,LA, USA, pp. 24-31, 2003.Menezes, A., P. Van Oorschot, and S. Vanstone, Handbook ofApplied Cryptography, CRC Press, pp.4-15, 516, 1996.NIST, “Secure Hash Standard,” Federal Information ProcessingStandard, FIPS-180-1, 1995.R. Lehtinen, (2006), “Computer Security Basics”, 2nd Edition,O'Reilly, ISBN-10: 0-596-00669-1.W. Stallings, “Cryptography and Network Security Principles andPractices”, Pearson Education, 5rd edition, 2011.M. Alia, A. Hnaif, H. Al-Anie, and A. Tamimi. "Graphical PasswordBased On Standard Shapes", Science Series Data Report ,Vol 4, No.2;Feb 2012Cisco. Security Certified Program – SCP. 2007.WCECS 2014
Proceedings of the World Congress on Engineering and Computer Science 2014 Vol IWCECS 2014, 22-24 October, 2014, San Francisco, Government Chief Information Officer."e-Authntication".http://www.e- authentication.gov.
Email of Dr. Abdelfatah Aref Tamimi is drtamimi@zuj.edu.jo. Email of Dr. Omaima N. A. AL-Allaf is omaimaalallaf@zuj.edu.jo increased recently for the public especially after the fast development of the Internet in the last 10 years ago. Figure 1: Network security system [1] This paper summarized the development in cryptography based authentication.
Cryptography with DNA binary strands and so on. In terms of DNA algorithms, there are such results as A DNA-based, bimolecular cryptography design, Public-key system using DNA as a one-way function for key distribution, DNASC cryptography system and so on. However, DNA cryptography is an
unauthorised users. Generally, authentication methods are categorised based on the factor used: knowledge-based authentication uses factors such as a PIN and password, token-based authentication uses cards or secure devices, and biometric authentication uses fingerprints. The use of more than one factor is called . multifactor authentication
of public-key cryptography; providing hands-on experience with some of the most common encryption algorithms that are used on the internet today. Modern Cryptography Introduction Outline 1 Introduction 2 Historical Cryptography Caesar Cipher 3 Public{Key Cryptography
Cryptography and Java Java provides cryptographic functionality using two APIs: JCA - Java Cryptography Architecture - security framework integrated with the core Java API JCE - Java Cryptography Extension - Extensions for strong encryption (exported after 2000 US export policy)
Broken Authentication - CAPTCHA Bypassing Broken Authentication - Forgotten Function Broken Authentication - Insecure Login Forms Broken Authentication - Logout Management Broken Authentication - Password Attacks Broken Authentication - Weak Passwords Session Management - Admin
utilize an authentication application. NFC provides a list of possible authentication applications for employees to use on the two-factor authentication screen in My EPP, but they may use other authentication applications or browser plugins. Authentication applications are device specific i.e. Windows, iOS (Apple), and Android.
RSA Authentication Agent for Microsoft Windows RSA Authentication Agent for Mi crosoft Windows works with RSA Authentication Manager to allow users to perform two-factor authentication when accessing Windows computers. Two-factor authentication requires something you know (for example, an RSA SecurID PIN) and something you have (for
The Concept of Two Factor Authentication Two factor authentication is an extra layer of authentication added to the conventional single factor authentication to an account login, which requires users to have additional information before access to a system is granted (Gonzalez, 2008). The traditional method of authentication requires the