Protecting Your Network From The Inside-Out - Terrapin
WHITE PAPERProtecting Your NetworkFrom the Inside-OutInternal Segmentation Firewall (ISFW)
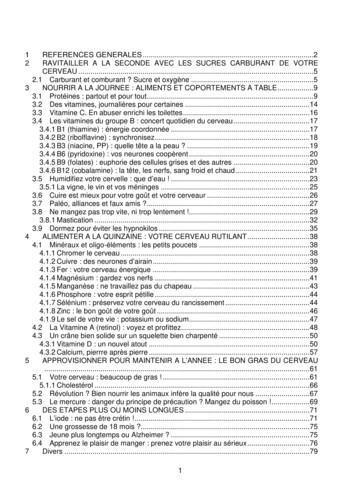
WHITE PAPER: PROTECTING YOUR NETWORK FROM THE INSIDE–OUT – INTERNAL SEGMENTATION FIREWALL (ISFW)Protecting Your NetworkFrom the Inside-OutInternal Segmentation Firewall (ISFW)Table of ContentsSummary3Advanced Threats Take Advantage of the “Flat Internal” Network4The Answer is a New Class of Firewall – Internal Segmentation Firewall 5ISFW Technology Requirements6Conclusion82www.fortinet.com
WHITE PAPER: PROTECTING YOUR NETWORK FROM THE INSIDE–OUT – INTERNAL SEGMENTATION FIREWALL (ISFW)SummaryFor the last decade organizations have been trying to protect theirnetworks by building defenses across the borders of their network.This includes the Internet edge, perimeter, endpoint, and datacenter (including the DMZ). This ‘outside-in’ approach has beenbased on the concept that companies can control clearly definedpoints of entry and secure their valuable assets. The strategywas to build a border defense as strong as possible and assumenothing got past the firewall.As organizations grow and embrace the latest IT technology such as Mobility and Cloudthe traditional network boundaries are becoming increasingly complex to control andsecure. There are now many different ways into an enterprise network.Key RequirementsnnnCOMPLETE PROTECTION –Continuous inside-out protectionagainst advanced threats with asingle security infrastructureEASY DEPLOYMENT –Default Transparent Mode meansno need to re-architect thenetwork and centrally deployedand ManagedHIGH PERFORMANCE –Multi-gigabit performance supportswire speed East-West trafficNot long ago, firewall vendors marked the ports on their appliances ‘External’ (Untrusted)and ‘Internal’ (Trusted). However, advanced threats use this to their advantage because,once inside, the network is very flat and open. The inside of the network usually consistsof non-security aware devices such as switches, routers and even bridges. So once yougain access to the network as a hacker, contractor or even rogue employee, then youget free access to the entire enterprise network including all the valuable assets.The solution is a new class of firewall – Internal Segmentation Firewall (ISFW), that sits atstrategic points of the internal network. It may sit in front of specific servers that containvaluable intellectual property or a set of user devices or web applications sitting inthe cloud.3www.fortinet.com
WHITE PAPER: PROTECTING YOUR NETWORK FROM THE INSIDE–OUT – INTERNAL SEGMENTATION FIREWALL (ISFW)Once in place, the ISFW must provide instant “visibility” to traffictraversing into and out of that specific network asset. Thisvisibility is needed instantly, without months of network planningand deployment.Most importantly the ISFW must also provide “protection”because detection is only a part of the solution. Sifting throughlogs and alerts can take weeks or months; the ISFW needs todeliver proactive segmentation and real-time protection basedon the latest security updates.Finally, the ISFW must be flexible enough to be placedanywhere within the internal network and integrate with otherparts of the enterprise security solution under a single pane ofmanagement glass. Other security solutions can also provideadditional visibility and protection. This includes the emailgateway, web gateway, border firewalls, cloud firewalls andendpoints. Further, Internal Segmentation Firewalls need toscale from low to high throughputs allowing deployment acrossthe global network.FIGURE 1 – ADVANCED THREAT LIFE CYCLE1It can be seen from the threat life cycle in Figure 1 that once theperimeter border is penetrated, the majority of the activity takesplace inside the boundary of the network. Activities includedisabling any agent-based security, updates from the botnetcommand and control system, additional infection/recruitmentand extraction of the targeted assets.InternalSocial EngineeringZero Days ExploitsMalicious URLsMalicious Apps, moreInfectionThreat VectorThreat Production ReconAPP4ExtractionPackage &Encrypt Stage4Cybercriminals are creating customized attacks to evadetraditional defenses, and once inside, to avoid detection andenable egress of valuable data. Once inside the network thereare few systems in place to detect or better still protectagainst APTs.ExternalScan for vulnerabilitiesDesign phishing emailsCustomize malware, etc.DisposalAdvanced Threats Take Advantageof the “Flat Internal” Network2URLCommunication3Hide, Spread,Disarm, Access,Contact Botnet C&C,Updatewww.fortinet.com
WHITE PAPER: PROTECTING YOUR NETWORK FROM THE INSIDE–OUT – INTERNAL SEGMENTATION FIREWALL (ISFW)The Answer is a New Class of Firewall –Internal Segmentation Firewall (ISFW)Most firewall development over the past decade has beenfocused on the border, the Internet edge, perimeter (hostfirewall), endpoint, data center (DMZ) or the cloud. Thisstarted with the stateful firewall but has evolved to includeUnified Threat Management (UTM) for distributed networks,which brought together the firewall, intrusion detection andantivirus. Later came the Next Generation Firewall (NGFW),which included intrusion prevention, and application controlfor the Internet edge. More recently because of the hugeincrease in speeds, Data Center Firewalls (DCFW) havearrived to provide more than 100Gbps of throughput. All ofthese firewalls have in common an approach designed toprotect from the “outside-in.”For rapid internal deployment and protection, a new class offirewall is required – Internal Segmentation Firewall (ISFW).The Internal Segmentation Firewall has some differentcharacteristics when compared to a border firewall. Thedifferences are laid out in figure 2.FIGURE 2 – FIREWALL TYPE DIFFERENCESDeployment ModeISFWNGFWPurposeVisibility & protectionfor internal segmentsLocationAccess LayerThe ISFW needs to provide complete protectionThe first element of security is visibility. And visibility is onlyas good as network packet knowledge. What does a packetstream look like for a specific application, where did it comefrom, where is it going, even what actions are being taken(download, upload ).The second and equally important element is protection. Isthe application, content or actions malicious? Should thistype of traffic be communicating from this set of assetsto another set of assets? While this is very difficult acrossdifferent content and application types, it is an essential partof the ISFW. The ability to detect a malicious file, applicationor exploit gives an enterprise time to react and contain thethreat. All of these protection elements must be on a singledevice to be effective.Both visibility and protection are heavily reliant on a realtime central security threat intelligence service. A questionthat always needs to posed – how good is the visibility andprotection. Is it keeping up with the latest threats? That’s whyall security services should be measured on a constant basiswith 3rd party test and certification services.UTMCCFWVisibility & protectionHigh performance, lowagainst external threats latency networkand internet activitiesaprotectionVisibility & protectionagainst external threatsand user activitiesNetwork security forService ProvidersInternet GatewayCore Layer/DC GatewayInternet GatewayVariousNetwork Operation Mode Transparent ModeNAT/Route ModeNAT/Route ModeNAT/Route ModeNAT/Route ModeHardware RequirementsHigher port density toprotect multiple assetsGbE and 10GbE portsHigh speed (GbE/10GbE/40 GbE/100) &high port density,hardware accelerationHigh GbE port density,integrated wirelessconnectivity and POEHigh speed (GbE/10GbE/40 GbE) &high port density,hardware accelerationSecurity ComponentsFirewall, IPS, ATP,Application Control(User-based) Firewall,VPN, IPS, ApplicationControlFirewall, DDoS protection Comprehensive andextensible, client anddevice integrationFirewall, CGN, LTE& mobile securityOther CharacteristicsRapid Deployment –Integration withnear zero configuration Advanced ThreatProtection (Sandbox)High AvailabilityHigh Availability5DCFWDifferent WANConnectivity Optionssuch as 3G4Gwww.fortinet.com
WHITE PAPER: PROTECTING YOUR NETWORK FROM THE INSIDE–OUT – INTERNAL SEGMENTATION FIREWALL (ISFW)The ISFW needs to provide easy deploymentThe ISFW must be easy to deploy and manage. Keepingit simple for IT means being able to deploy with minimumconfiguration requirements and without having to re-architectthe existing network.The ISFW must also be able to protect different types ofinternal assets placed at different parts of the network. Itcould be a set of servers containing valuable customerinformation or a set of endpoint devices that may not be ableto be updated with the latest security protection.Additionally the ISFW must be able to integrate with otherparts of the enterprise security solution. Other securitysolutions can also provide additional visibility and protection.This includes the email gateway, web gateway, borderfirewalls, cloud firewalls and endpoints. This all needs to bemanaged with a ‘single pane of glass’ approach. This allowssecurity policies to be consistent at the border, inside thenetwork and even outside the network in clouds.Additionally, traditional firewalls are usually deployed in routingmode. Interfaces (ports) are well defined with IP addresses.This often takes months of planning and deployment. This isvaluable time in today’s instant cyber attack world. An ISFWcan be deployed in the network rapidly and with minimumdisruption. It must be as simple as powering on a deviceand connecting. It must be transparent to the network andapplication.The ISFW needs to provide wire-speed performanceBecause internal segmentation firewalls are deployed in-linefor network zoning, they must be very high performance inorder to meet the demands of internal or “East/West” traffic,and to ensure they do not become a bottleneck at thesecritical points. Unlike firewalls at the border which deal withWide Area Network (WAN) access or Internet speeds ofless than 1 gigabit per second, internal networks run muchfaster – multi-gigabit speeds. There, ISFWs need to operateat multi-gigabit speeds and be able to provide deep packet/connect inspection without slowing down the network.6ISFW Technology RequirementsA Flexible Network Operating SystemAlmost all firewall “deployments modes” require IP allocationand reconfiguration of the network. This is known as networkrouting deployment and provides traffic visibility and threatprevention capabilities. At the other end of the spectrumis sniffer mode, which is easier to configure and providesvisibility, but does not provide protection.Transparent mode combines the advantages of NetworkRouting and Sniffer modes – it provides rapid deploymentand visibility plus, more importantly, protection. Thedifferences are summarized in Figure 3.DeploymentDeploymentNetworkFIGURE3 – FIREWALLTYPE DIFFERENCESHighTrafficAvailability xityFunctionsHighL3-Routing rent mode combines the advantages of NetworkRouting and Sniffer mode. So it provides rapid deploymentand visibility plus more importantly, protection. Thedifferences are summarized in Figure 3.A Scalable Hardware ArchitectureBecause internal networks run at much higher speedsthe ISFW needs to be architected for multi-gigabit protectionthroughput. Although CPU-only based architectures areflexible they become bottlenecks when high throughput isrequired. The superior architecture still uses a CPUfor flexibility but adds custom ASICs to accelerate networktraffic and content inspection.Because the ISFW is deployed in closer proximity to the dataand devices, it may sometimes need to cope with harsherenvironments. Availability of a more ruggedized form factor istherefore another requirement of ISFWs.www.fortinet.com
WHITE PAPER: PROTECTING YOUR NETWORK FROM THE INSIDE–OUT – INTERNAL SEGMENTATION FIREWALL (ISFW)CLOUDINTERNALApplicationsData CenterCampusINTERNALVirtual ISFWISFWEdgeFirewall(NGFW)Data CenterFirewall(DCFW)ISFWFIGURE 4 – Internal Segmentation Firewall(ISFW) eatManagement(UTM)INTERNALNetwork Segmentation –High Speed Integrated SwitchingAn evolving aspect of transparent mode is the ability tophysically separate subnetworks and servers via a switch.Firewalls are starting to appear on the market with fullyfunctional, integrated switches within the appliance. Thesenew firewalls, with many 10GbE port interfaces, become anideal data center ‘top-of-rack’ solution, allowing servers to bephysically and virtually secured. Also, similar switch-integratedfirewalls with a high density of 1GbE port interfaces becomeideal for separation of LAN subsegments. ISFWs should be ableto fulfill both of these roles, and as such should ideally have fullyfunctional, integrated switching capabilities.Segment ISFW Deployment ExampleThe ISFW is usually deployed in the access layer and protectsa specific set of assets. Initially the deployment is transparentbetween the distribution and access switches. Longer term theintegrated switching could take the place of the access anddistribution switch and provide additional physical protection.FIGURE 5 –INTERNAL SEGMENTATION FIREWAL (ISFW) DEPLOYMENTTo InternetReal-time SecurityInternal Segmentation Firewalls must be able to deliver afull spectrum of advanced security services, including IPS,application visibility, antivirus, anti-spam, and integration withcloud-based sandboxing, allowing for the enforcement ofpolicies that complement standard border firewalls. This realtime visibility and protection is critical to limiting the spread ofmalware inside the network.Network Wide ISFW Deployment ExampleMost companies have set up border protection with firewalls,NGFWs and UTMs. These are still critical parts of the networkprotection. However to increase the security posture, InternalSegmentation Firewalls can be placed strategically internally.This could be a specific set of endpoints where it is hard toupdate security or servers where intellectual property is stored.7DISTRIBUTION/CORE LAYERCore/Distribution SwitchAccess Switch / VLANLOCAL SERVERSnFortiGate wireintercept usingtransparentport pairnHigh speedinterfaceconnectivitynIPS, ATP &App ControlUSER NETWORKDEVICESACCESS LAYERwww.fortinet.com
WHITE PAPER: PROTECTING YOUR NETWORK FROM THE INSIDE–OUT – INTERNAL SEGMENTATION FIREWALL (ISFW)Enhancing Advanced ThreatProtection with Internal VisibilityA proper approach to mitigating advanced threats shouldinclude a continuous cycle of Prevention, Detection, andMitigation. Very typically a Next-Generation Firewall wouldserve as a key foundation of the Prevention component,enabling L2/L3 firewall, intrusion prevention, applicationcontrol and more to block known threats, while passinghigh-risk unknown items to a sandbox for Detection. But withNGFW’s deployed traditionally at the network edge, this onlyprovides partial visibility into the attack life cycle by primarilyobserving ingress and egress activity.Deployment of an ISFW can provide more complete visibilityinto the additional internal activity of the hackers once they’vecompromised the edge. Lateral movement can account fora significant portion of the malicious activity as the hackerstry to identify valuable assets and extract data, and having acomplete picture of both internal and edge activity enhancesall phases of a complete ATP framework. With internalnetwork traffic often being several times the bandwidth ofedge traffic, an ISFW can provide many more opportunitiesto limit the spread of the compromise from known techniquesand more high-risk items to be passed to sandboxes fordeeper inspection.ConclusionAdvanced Threats are taking advantage of the flat Internalnetwork. Once through the border defense there is little tostop their spread and eventual extraction of valuable targetedassets. Because traditional firewalls have been architected toslower speeds of the Internet Edge its hard to deploy thesesecurity devices internally. And firewall network configurationdeployments (IP addresses) take a long time to deploy.FIGURE 5 – ADVANCED THREAT PROTECTION (ATP) FRAMEWORKGLOBAL HEADQUARTERSFortinet Inc.899 Kifer RoadSunnyvale, CA 94086United StatesTel: 1.408.235.7700www.fortinet.com/salesInternal Segmentation Firewalls are a new class of firewallthat can be deployed rapidly with minimum disruption whilekeeping up the multi-gigabit speeds of internal networks.Instant visibility and protection can be applied to specificparts of the internal network.EMEA SALES OFFICE120 rue Albert Caquot06560, Sophia Antipolis,FranceTel: 33.4.8987.0510APAC SALES OFFICE300 Beach Road 20-01The ConcourseSingapore 199555Tel: 65.6513.3730LATIN AMERICA SALES OFFICEPaseo de la Reforma 412 piso 16Col. JuarezC.P. 06600México D.F.Tel: 011-52-(55) 5524-8428Copyright 2015 Fortinet, Inc. All rights reserved. Fortinet , FortiGate , FortiCare and FortiGuard , and certain other marks are registered trademarks of Fortinet, Inc., and other Fortinet names herein may also be registered and/or common lawtrademarks of Fortinet. All other product or company names may be trademarks of their respective owners. Performance and other metrics contained herein were attained in internal lab tests under ideal conditions, and actual performance and otherresults may vary. Network variables, different network environments and other conditions may affect performance results. Nothing herein represents any binding commitment by Fortinet, and Fortinet disclaims all warranties, whether express or implied,except to the extent Fortinet enters a binding written contract, signed by Fortinet’s General Counsel, with a purchaser that expressly warrants that the identified product will perform according to certain expressly-identified performance metrics and, insuch event, only the specific performance metrics expressly identified in such binding written contract shall be binding on Fortinet. For absolute clarity, any such warranty will be limited to performance in the same ideal conditions as in Fortinet’s internallab tests. Fortinet disclaims in full any covenants, representations, and guarantees pursuant hereto, whether express or implied. Fortinet reserves the right to change, modify, transfer, or otherwise revise this publication without notice, and the mostcurrent version of the publication shall be applicable.July 14, 2015
WHITE PAPER: PROTECTING YOUR NETWORK FROM THE INSIDE-OUT - INTERNAL SEGMENTATION FIREWALL (ISFW) The Answer is a New Class of Firewall - Internal Segmentation Firewall (ISFW) Most firewall development over the past decade has been focused on the border, the Internet edge, perimeter (host firewall), endpoint, data center (DMZ) or the cloud.
May 02, 2018 · D. Program Evaluation ͟The organization has provided a description of the framework for how each program will be evaluated. The framework should include all the elements below: ͟The evaluation methods are cost-effective for the organization ͟Quantitative and qualitative data is being collected (at Basics tier, data collection must have begun)
Silat is a combative art of self-defense and survival rooted from Matay archipelago. It was traced at thé early of Langkasuka Kingdom (2nd century CE) till thé reign of Melaka (Malaysia) Sultanate era (13th century). Silat has now evolved to become part of social culture and tradition with thé appearance of a fine physical and spiritual .
̶The leading indicator of employee engagement is based on the quality of the relationship between employee and supervisor Empower your managers! ̶Help them understand the impact on the organization ̶Share important changes, plan options, tasks, and deadlines ̶Provide key messages and talking points ̶Prepare them to answer employee questions
On an exceptional basis, Member States may request UNESCO to provide thé candidates with access to thé platform so they can complète thé form by themselves. Thèse requests must be addressed to esd rize unesco. or by 15 A ril 2021 UNESCO will provide thé nomineewith accessto thé platform via their émail address.
Dr. Sunita Bharatwal** Dr. Pawan Garga*** Abstract Customer satisfaction is derived from thè functionalities and values, a product or Service can provide. The current study aims to segregate thè dimensions of ordine Service quality and gather insights on its impact on web shopping. The trends of purchases have
Chính Văn.- Còn đức Thế tôn thì tuệ giác cực kỳ trong sạch 8: hiện hành bất nhị 9, đạt đến vô tướng 10, đứng vào chỗ đứng của các đức Thế tôn 11, thể hiện tính bình đẳng của các Ngài, đến chỗ không còn chướng ngại 12, giáo pháp không thể khuynh đảo, tâm thức không bị cản trở, cái được
Le genou de Lucy. Odile Jacob. 1999. Coppens Y. Pré-textes. L’homme préhistorique en morceaux. Eds Odile Jacob. 2011. Costentin J., Delaveau P. Café, thé, chocolat, les bons effets sur le cerveau et pour le corps. Editions Odile Jacob. 2010. Crawford M., Marsh D. The driving force : food in human evolution and the future.
Le genou de Lucy. Odile Jacob. 1999. Coppens Y. Pré-textes. L’homme préhistorique en morceaux. Eds Odile Jacob. 2011. Costentin J., Delaveau P. Café, thé, chocolat, les bons effets sur le cerveau et pour le corps. Editions Odile Jacob. 2010. 3 Crawford M., Marsh D. The driving force : food in human evolution and the future.